
Anshum Garg

David M. Lentz
Auth0 provides identity as a service (IDaaS), allowing you to secure your apps and APIs without having to write your own authorization code. Auth0 can work with social identity providers (IdP) like Google and Facebook so your users can access your app by using their existing accounts for authentication. You can also use an existing enterprise identity provider (e.g., LDAP) to allow your users to leverage single sign-on (SSO) across multiple apps. Auth0 helps you implement login features like these—along with options like multi-factor authentication (MFA) and passwordless authentication—while removing the burden of maintaining your own authentication functionality.
Datadog’s Auth0 integration allows you to monitor and analyze Auth0 logs to detect user actions that could indicate security concerns and to better understand how users interact with your application. You can graph and alert on the number of logins to your application and use data from your Auth0 logs to automatically trigger notifications based on threat detection rules you define. And you can easily configure long-term retention to meet regulatory requirements by archiving Auth0 logs in your preferred cloud storage service.
Analyze and audit Auth0 activity
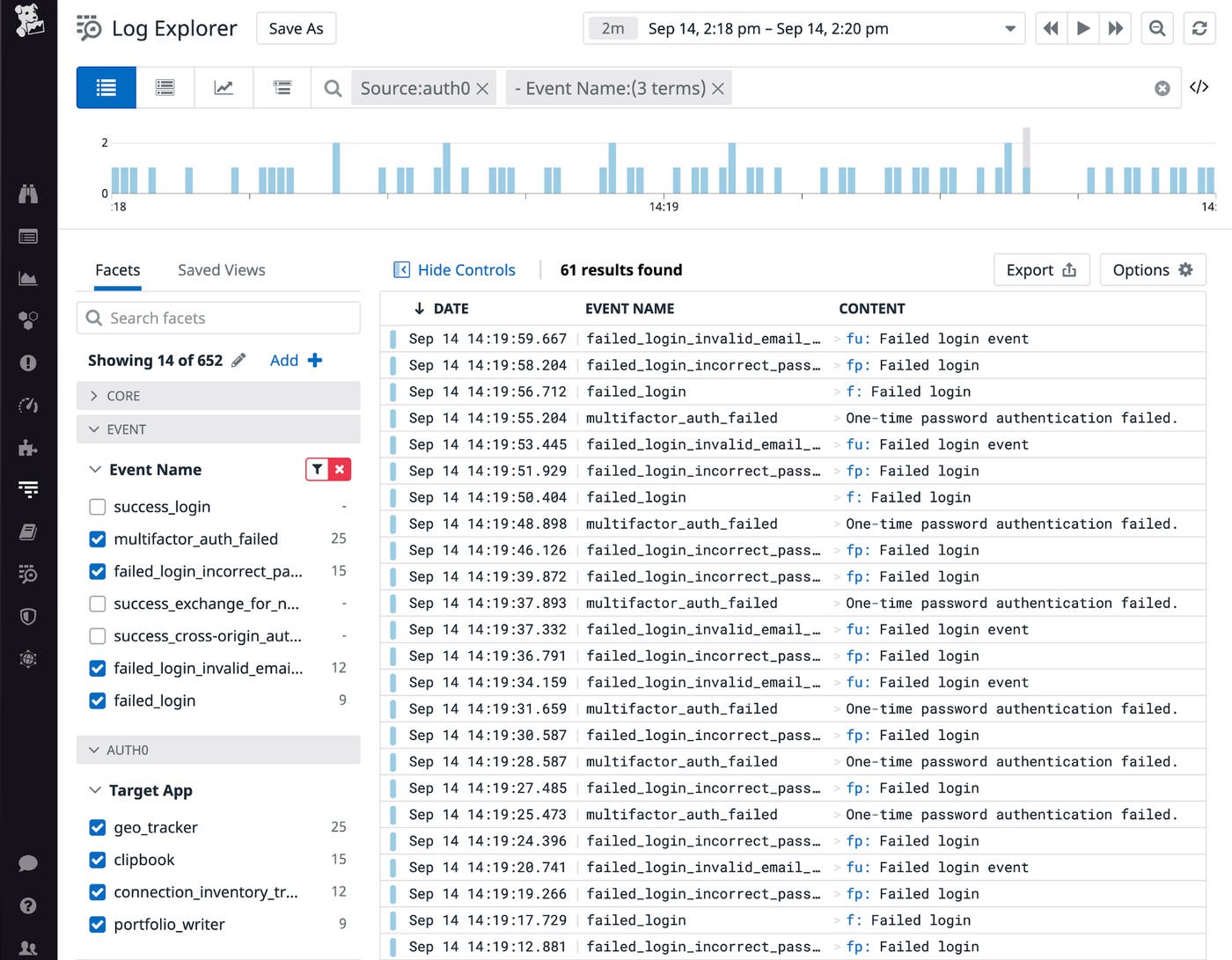
As Datadog ingests your Auth0 logs, it sends them through a log processing pipeline. The pipeline automatically parses each log to extract key data as standard attributes, which provide a naming convention you can use to easily correlate events from multiple sources. Datadog automatically maps the Auth0 event type code to evt.name, which appears as the standard Event Name facet. You can use this facet to analyze user activity such as account creation and deletion, password changes, and more. In the screenshot above, we’ve filtered the view to graph log data only from apps that use Auth0 as an authentication provider (source:auth0), and to display logs that have one of the event names that indicate a failed login.
Visualize key Auth0 events
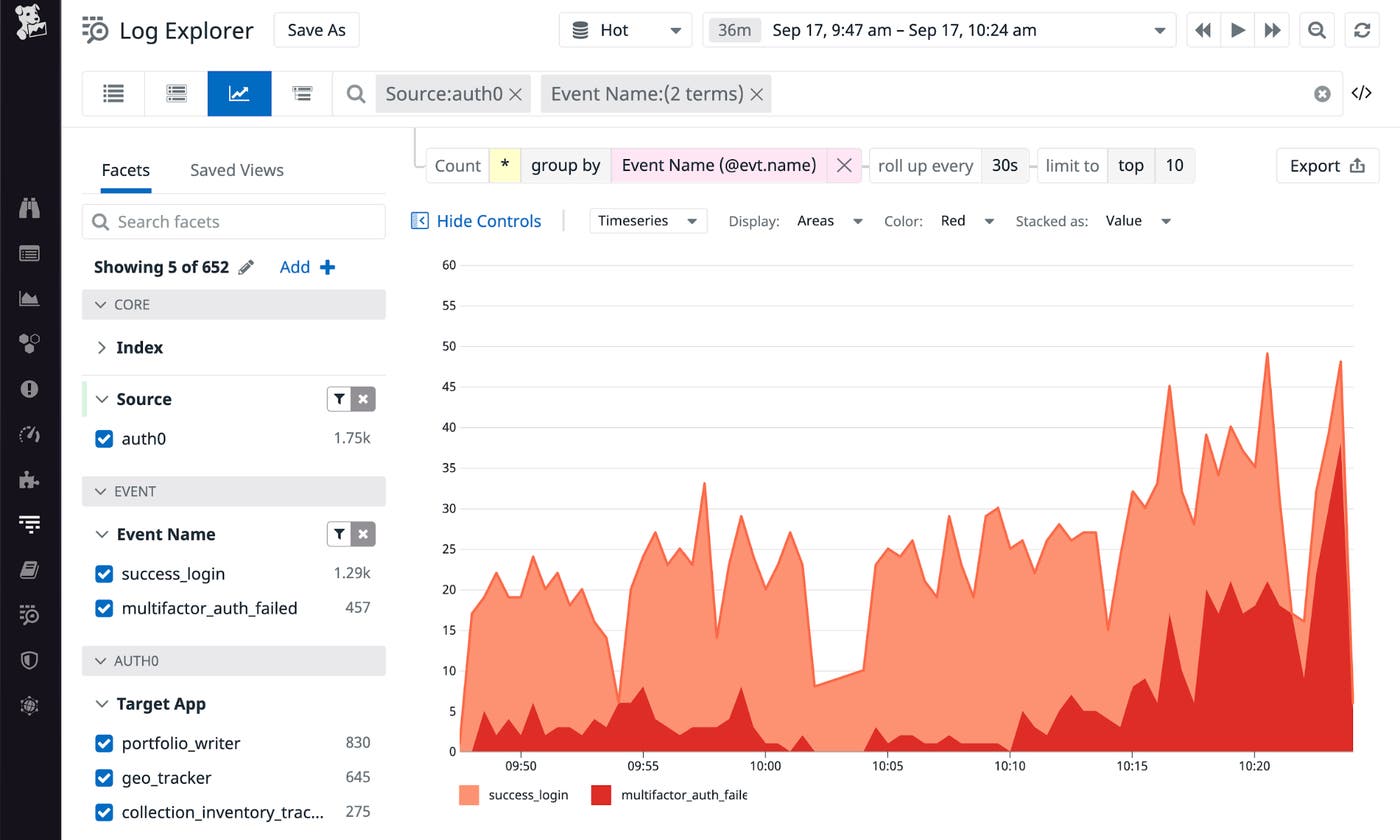
You can use log analytics to visualize log data in Datadog, revealing potentially suspicious patterns in user activity. For example, logins and multi-factor authentications commonly fail due to user error, but if your log data shows a rising frequency of events like these, it could be evidence of automated attacks against your application. In the screenshot below, the graph visualizes successful logins in orange and failed MFA logins in red. To investigate a spike like the one shown here, you can click a point on the graph to see related logs that give you deeper context on the issue.
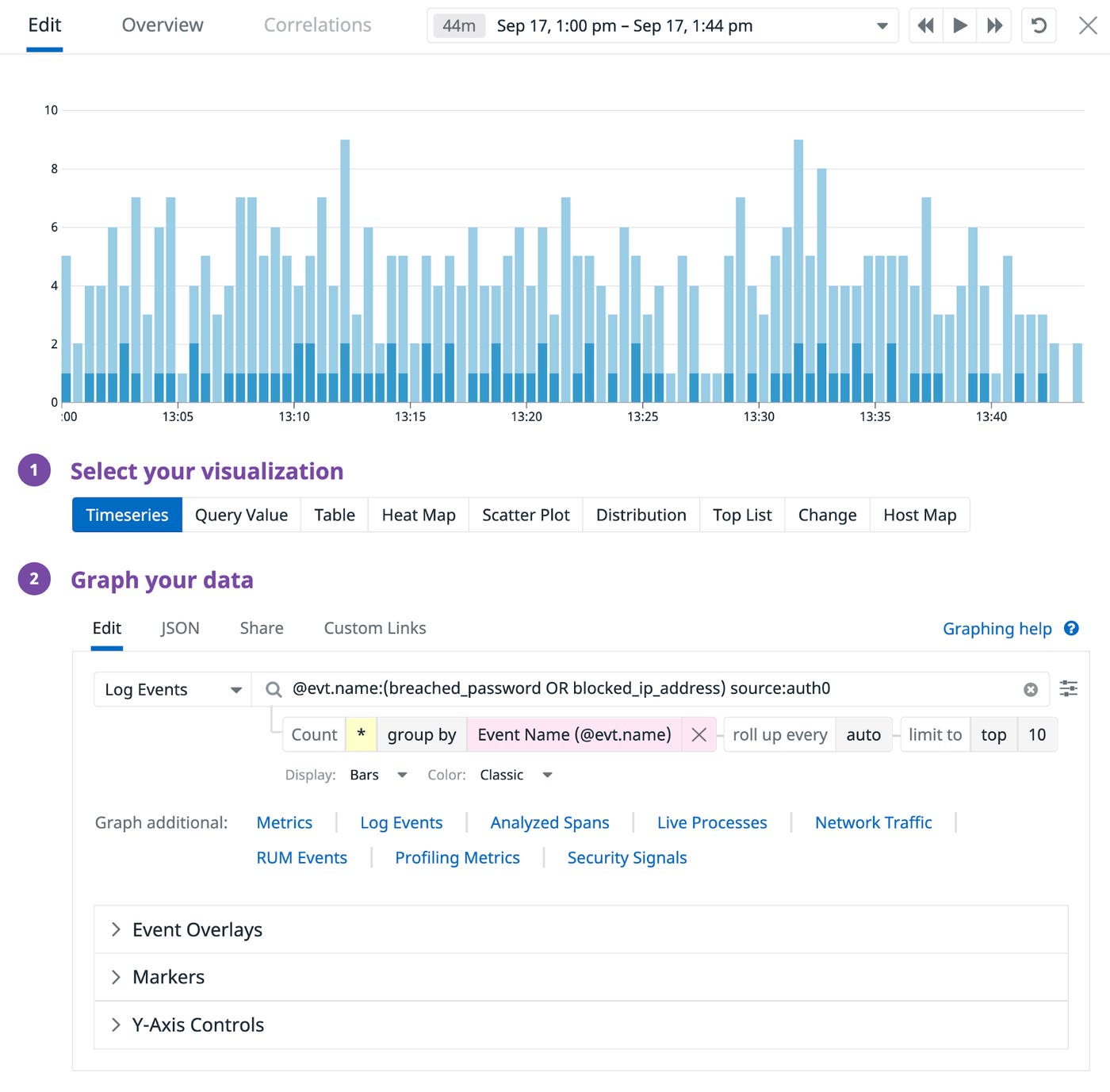
Auth0’s anomaly detection feature automatically blocks an IP address that has generated an abnormally high rate of unsuccessful login attempts. A rising rate of blocking events could indicate an attack. The screenshot below shows how you can graph events like blocked IP addresses as well as attempted logins using breached passwords.
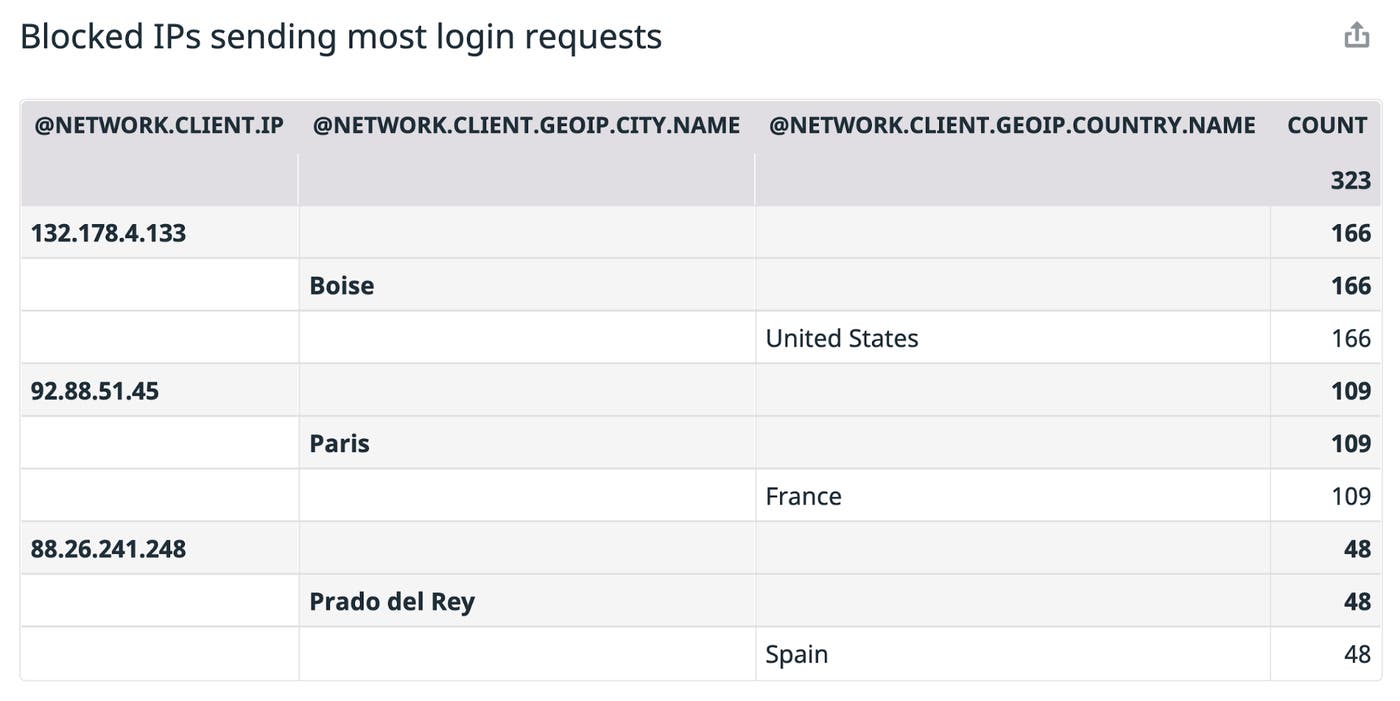
You can use a table like the one shown below—which lists the number of requests sent from the IP addresses blocked by Auth0—to investigate further.
In the next section, we’ll show you how you can also use Datadog Cloud SIEM to automatically notify you of potential issues detected in your Auth0 data.
Use Cloud SIEM and threat notifications
Datadog Cloud SIEM uses threat detection rules to alert you when a threat is detected. A collection of out-of-the-box rules for Auth0 logs makes it easy to monitor for some common threats in real time—such as a user authenticating from multiple countries, which indicates an attempt to compromise a user’s credentials.
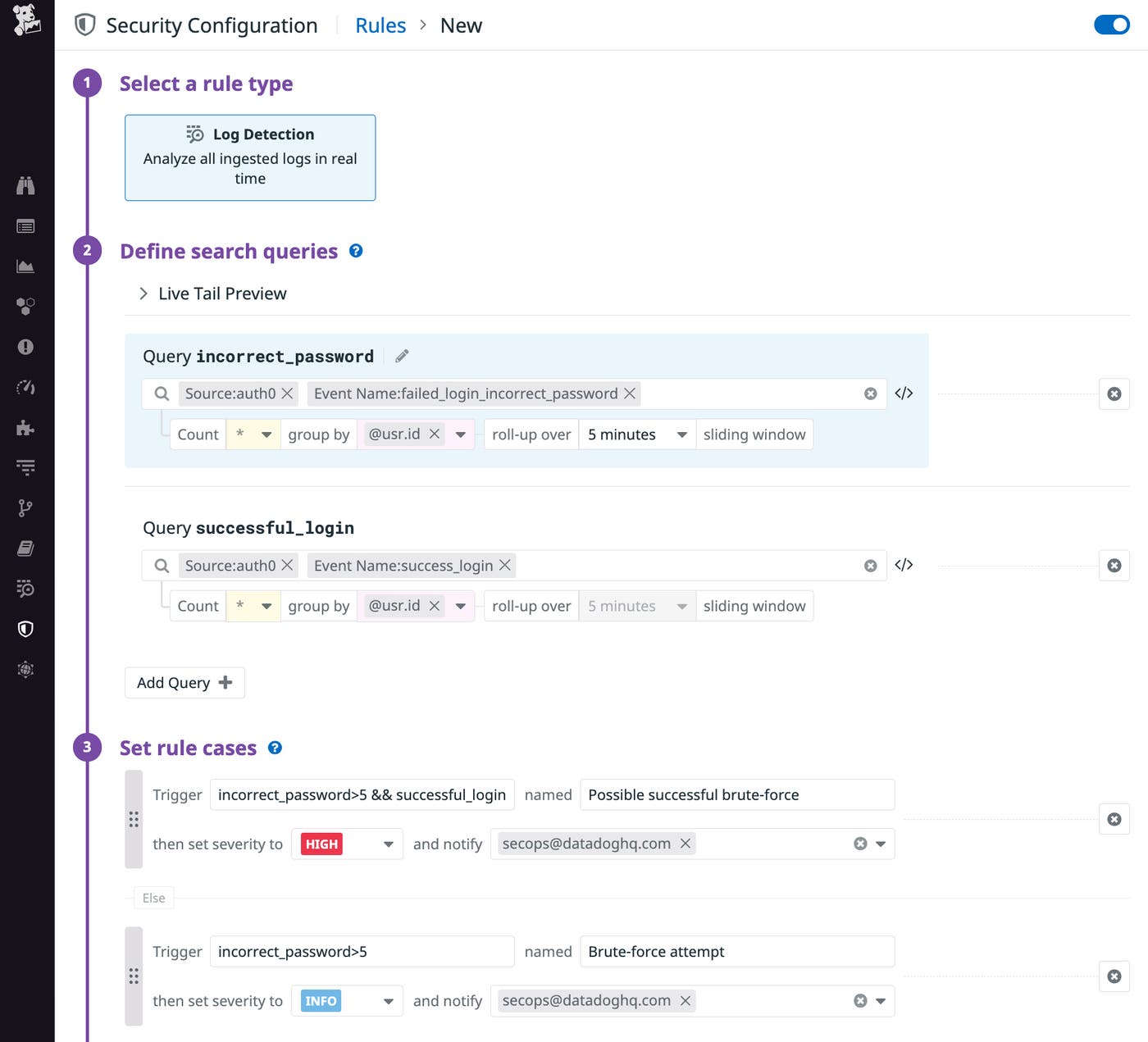
You can also create custom rules based on thresholds you define for identifying suspicious behavior. Datadog analyzes Auth0 logs in real time to detect any violations of your threat detection rules. If a rule is violated, Datadog will alert your team via email, Slack, Jira, or other collaboration tools that suit your incident response process.
In the screenshot below, we’ve configured Datadog to alert the security operations team via email if there are five failed logins and a successful login from a single user within five minutes, which could indicate a possible brute force attack.
Your security operations team can use the information in an alert like this to investigate and remediate the threat. If the information in the alert points to a specific IP address that shows a pattern of suspicious activity, you can investigate further by correlating your Auth0 logs with your other application logs. If necessary, you can take additional measures such as blocking the IP address in your web application firewall.
Extend your security visibility with Datadog
Datadog’s Auth0 integration brings deep visibility into your Auth0 logs, which—alongside Datadog Cloud SIEM and integrations for more than 1,000 other technologies—means you can ensure the security of your applications and the infrastructure that runs them.
To enable Auth0 monitoring in Datadog, check out our documentation. If you’re not already using Datadog, sign up today for a free 14-day trial.

