Lucas Maley

Christina DePinto
Organizations adopt multi-cloud architectures for many reasons, including compliance requirements, business strategy, and resiliency. Regardless of the cloud provider, the security challenges remain the same: Identify the most critical risks, prioritize them with business context, and remediate them before they are exploited by a bad actor.
To deliver greater visibility and actionable context across multi-cloud environments, Datadog Cloud Security now supports Oracle Cloud Infrastructure (OCI). This release builds on Datadog’s continued investment in OCI, following previous support in Cloud SIEM, Cloud Cost Management, and Database Monitoring. Security teams get the same trusted capabilities that they already rely on to help secure their AWS, Microsoft Azure, and Google Cloud infrastructure, all within a single platform.
In this post, we’ll show how Cloud Security extends to OCI to help you:
- Centralize visibility across your multi-cloud security posture
- Embed security findings into your existing workflows
Centralize visibility across your multi-cloud security posture
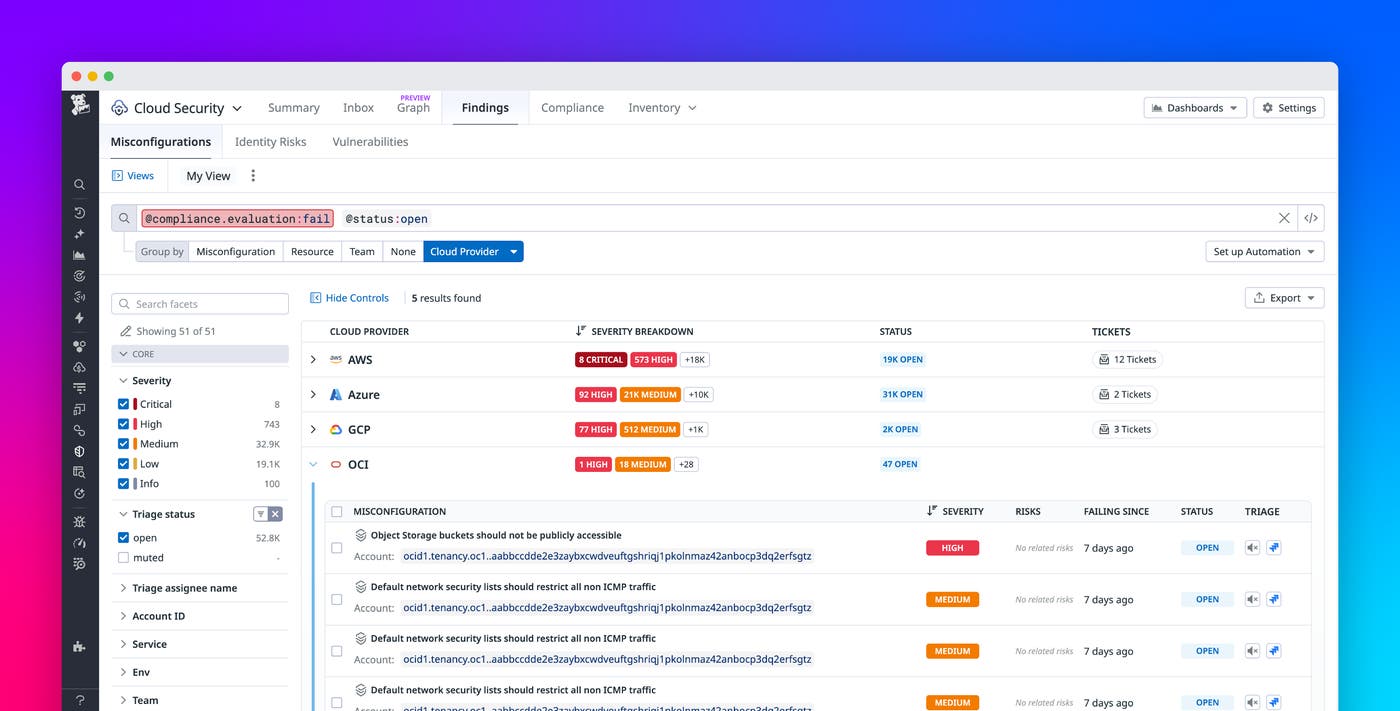
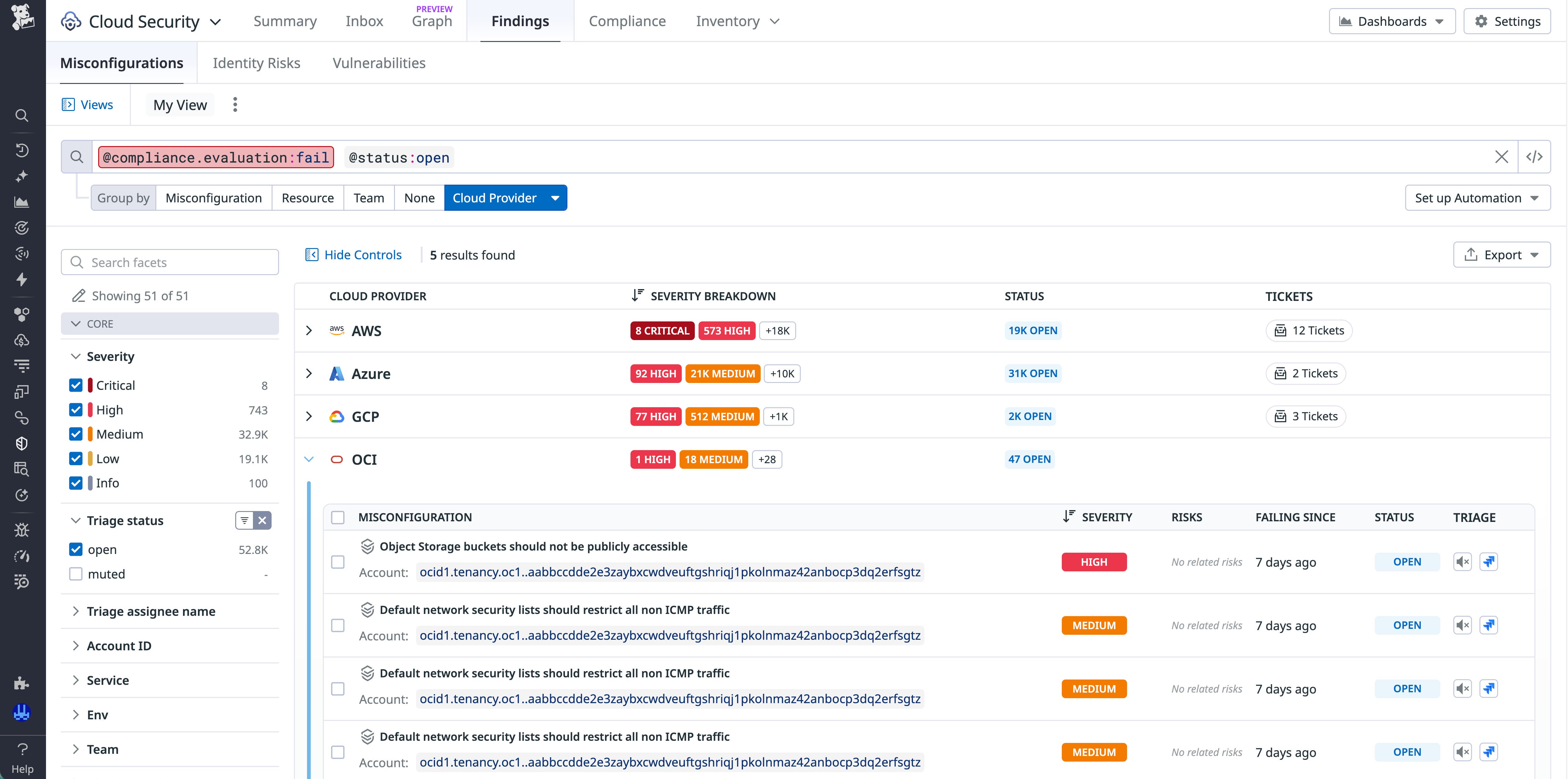
Often, security tools are purchased but not fully adopted because they are siloed from the critical operational insights that other monitoring tools provide. Cloud Security centralizes OCI security findings alongside findings from AWS, Azure, and Google Cloud, in addition to related metrics, traces, and logs. This unified view helps eliminate visibility gaps and reduce tool sprawl, and it saves time because you don’t need to toggle between screens to get full risk context for a postmortem or audit.
Embed security findings into your existing workflows
Cloud Security findings are surfaced directly within the Datadog workflows that DevOps and engineering teams use every day, including those in Case Management, On-Call, and Workflow Automation. With security embedded into existing monitoring and operational processes, findings become immediately accessible to the teams responsible for remediation.
Each OCI finding in Cloud Security contains detailed resource information, including the severity of the risk and the team that owns the resource. You can see who is on the team, page the team directly, or ping the person who is on call. You can also assign the risk to any Datadog user, who can then see the information about the risk and the steps for remediation.
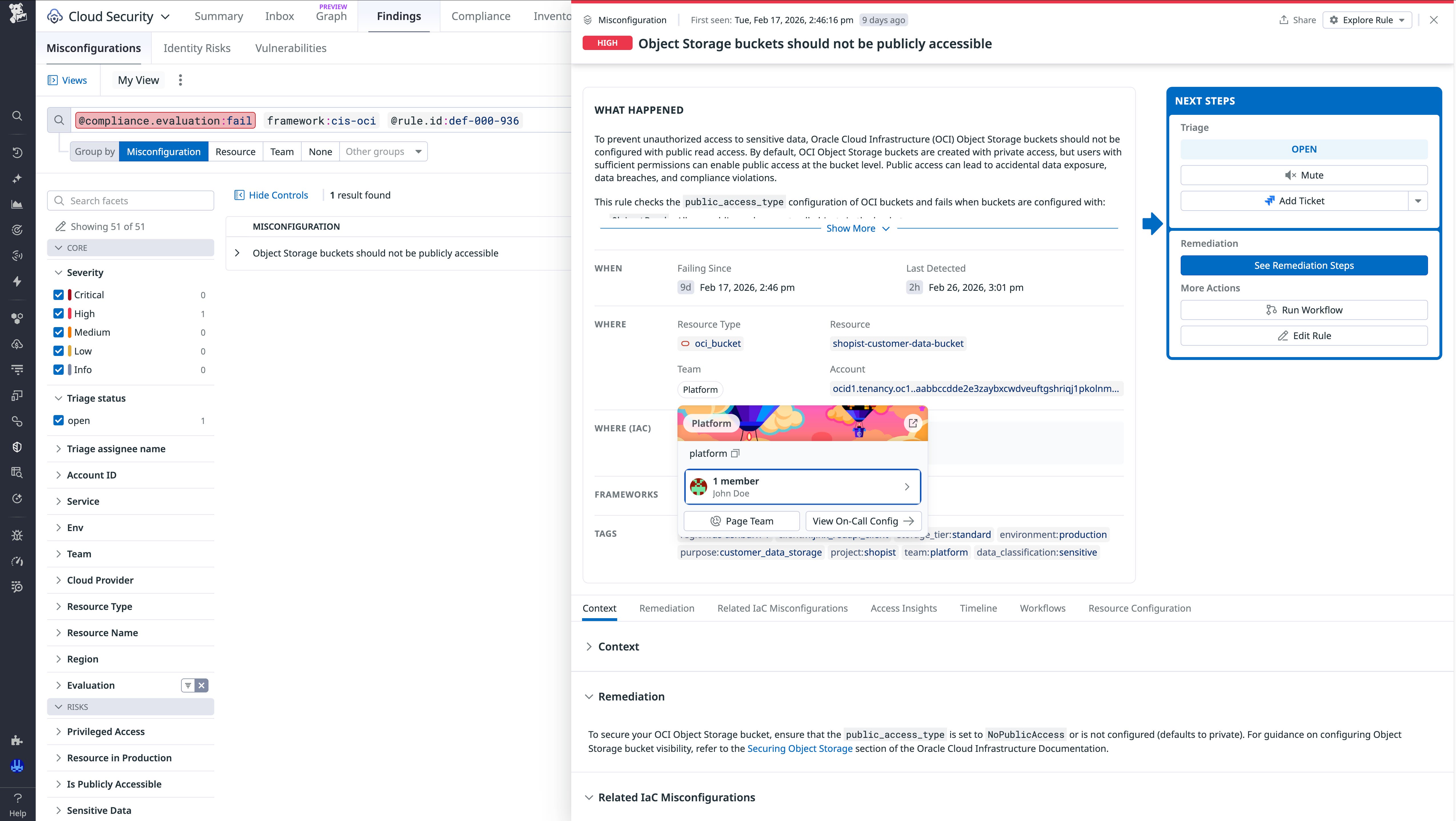
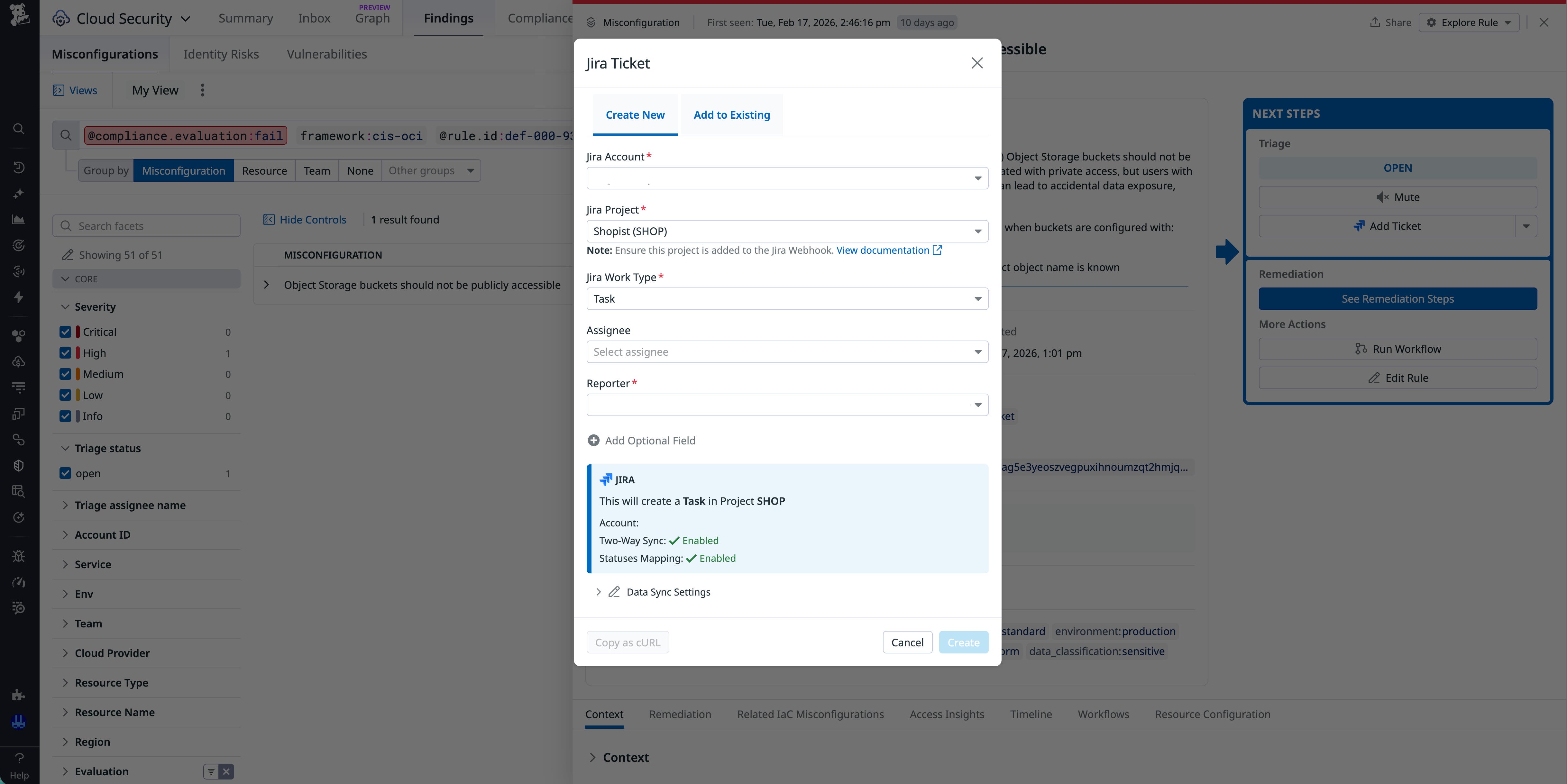
In addition, bidirectional Jira syncing keeps findings and tickets aligned across systems. You can create new tickets or add findings to existing tickets directly from Datadog or Jira, and the updates automatically sync between the platforms. Findings close only when remediation is completed or when an exception has been formally tracked for audit purposes. Related cases and tickets close automatically, reducing manual follow-up and maintaining clean audit trails. This shared context across systems reduces cross-team handoffs, accelerates response times, and helps you resolve security issues before they escalate.
Start securing your OCI environment with Datadog
With the addition of support for OCI, Datadog Cloud Security extends unified security visibility across your multi-cloud environment. Security teams can assess risk consistently across the major cloud providers, prioritize findings with appropriate context, and respond faster, all from a single platform. To learn more about how Cloud Security can help your organization detect and resolve security issues, check out the Cloud Security documentation.
If you’re new to Datadog, you can sign up for a 14-day free trial to get started.