Vera Chan

Ron Feldman

Rex Guo
Security analysts face unprecedented challenges in today's cloud landscape. Security operations center (SOC) teams are chronically understaffed, and cybersecurity threats are skyrocketing—further intensified by GenAI-driven attacks. High false positive rates add to this strain, fueling alert fatigue and delaying the detection of real threats. These hurdles make it harder for analysts to keep pace, which ultimately drives up mean time to resolution (MTTR).
Datadog Cloud SIEM has continually evolved to help SOC teams meet these challenges with powerful investigative capabilities, including:
Hundreds of out-of-the-box integrations and detection rules
Advanced graph-based visualizations
Native Security Orchestration, Automation, and Response (SOAR) workflows and case management
Intelligent, context-aware risk scoring
Bits AI Security Analyst, announced in Preview in June 2025, is now generally available. Bits AI has investigated tens of thousands of security alerts for Preview customers, saving hundreds of person-years of manual investigation time. It autonomously triages Datadog Cloud SIEM signals, conducts in-depth investigations of potential threats, and delivers clear, actionable recommendations without human prompting.
This is one of three AI agents, each designed to support cross-functional roles across security, SRE, and development. Since its launch, Bits AI has expanded its capabilities to support DevOps by investigating alerts, managing incidents, resolving coding errors, and more. With Bits AI Security Analyst, we're taking Cloud SIEM to the next level by fundamentally transforming how security teams investigate and resolve security signals.
Let's take a closer look at how Bits AI Security Analyst works.
Autonomous Cloud SIEM triage
Bits AI asynchronously investigates SIEM signals across the following attack surfaces and sources (additional surfaces and source coverage coming soon):
| Category | Tools / Services |
|---|---|
| Cloud Control Plane | AWS CloudTrail, Azure, GCP, Kubernetes |
| Identity | Okta, Entra ID, Google Workspace |
| SaaS and Collaboration | MS365, Google Workspace |
| Dev Tools | GitHub, Snowflake |
| Endpoint Detection and Response (EDR) | SentinelOne |
| User-reported phishing |
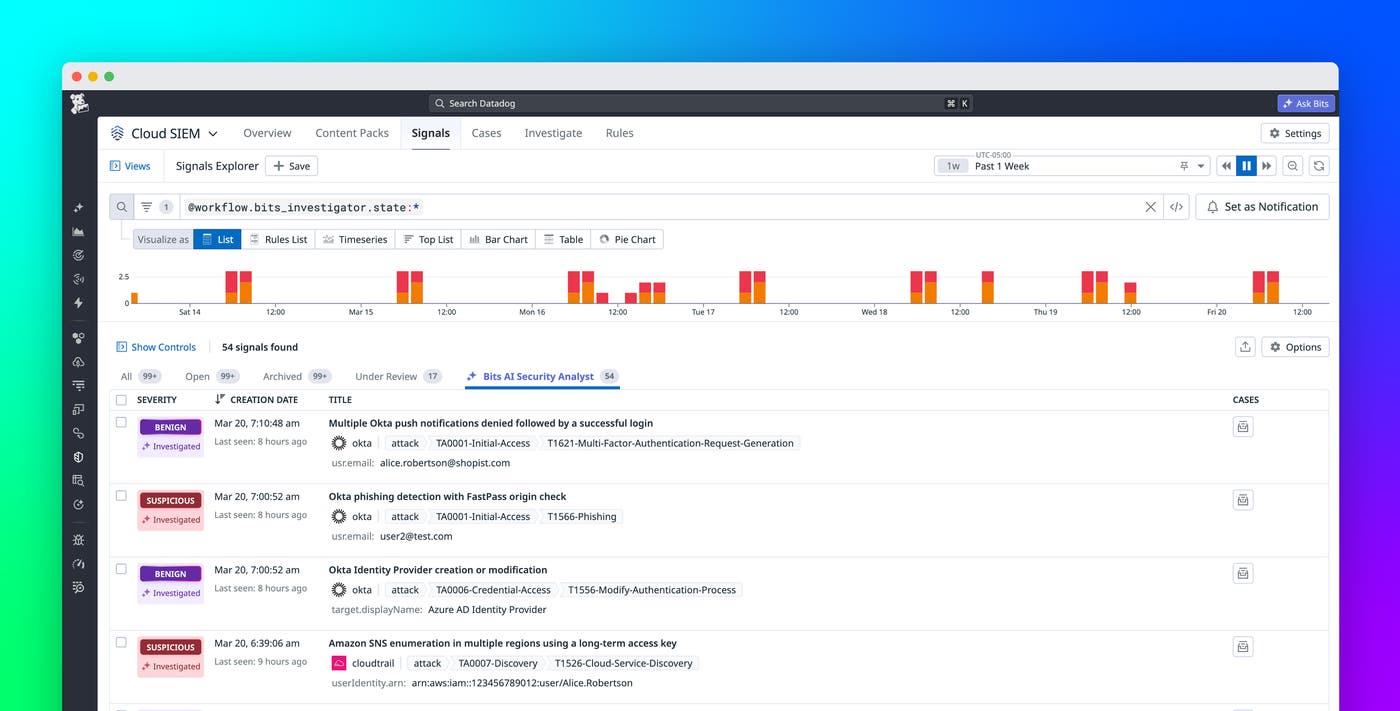
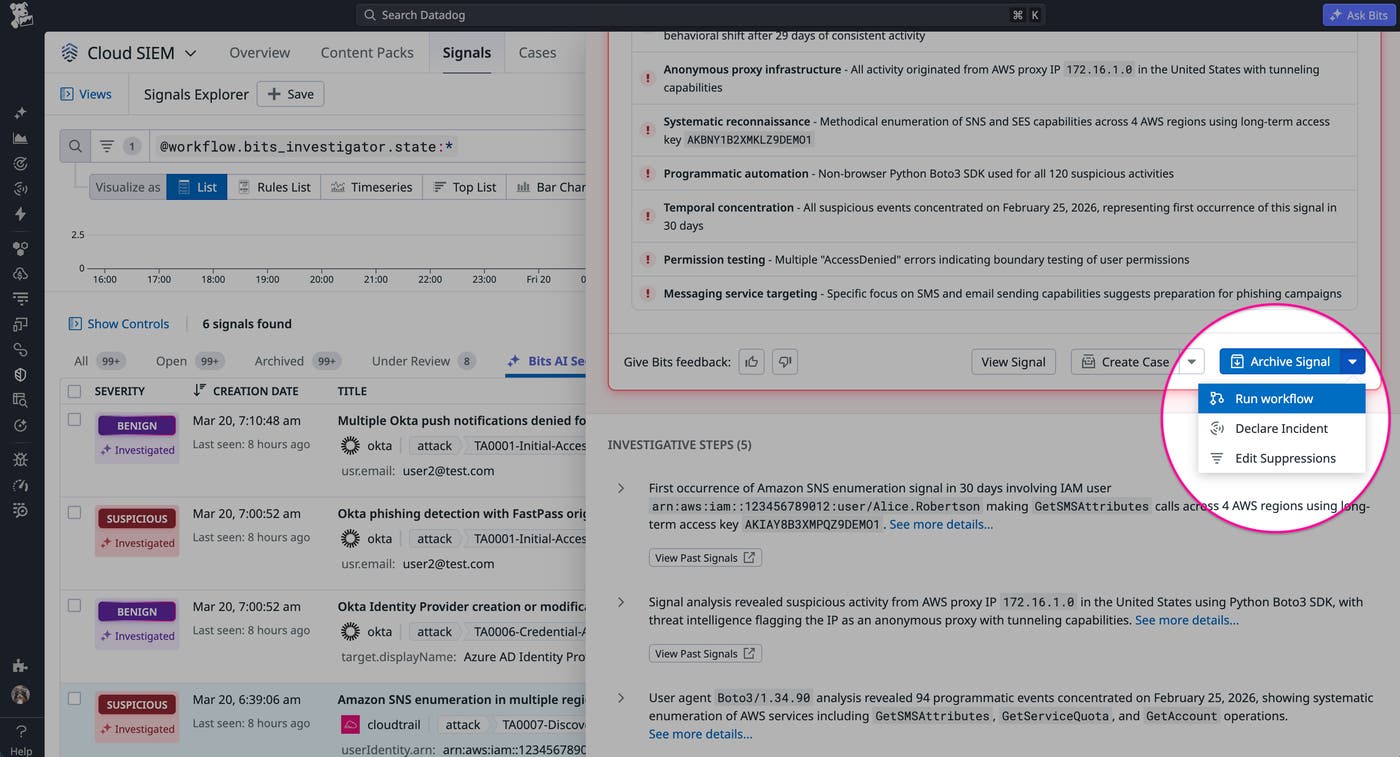
Each investigated signal is clearly marked with a dedicated facet, allowing you to filter the Cloud SIEM Signals list or trigger targeted notifications. To view a finding, just click the signal in the list or notification to open the Bits AI investigation side panel. In the following screenshot, Bits AI automatically investigated actions taken by an authorized Okta administrator, without human intervention.
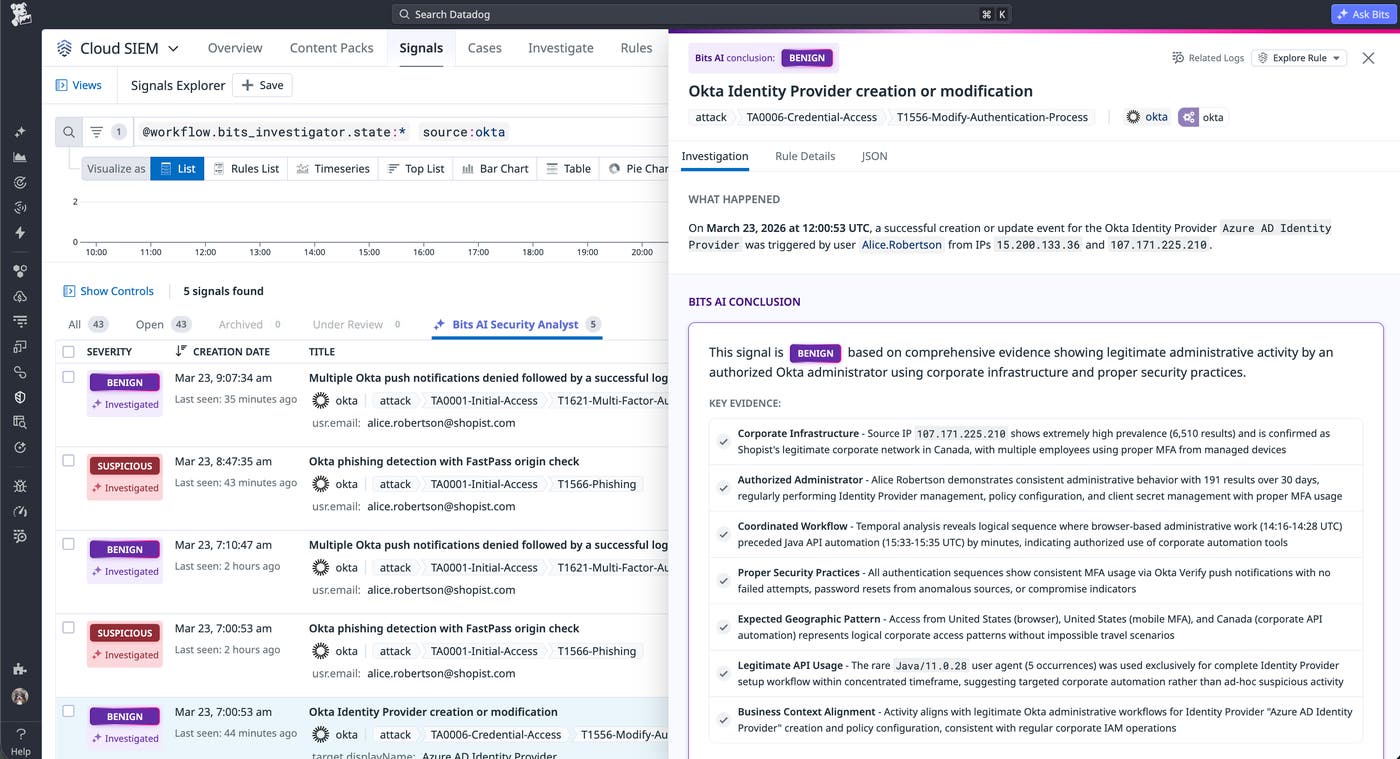
In-depth, evidence-based investigations
Bits AI Security Analyst draws on the expertise of Datadog's internal Security and Security Research teams. Using the MITRE ATT&CK framework as a foundation, the agent methodically plans and executes each step of its investigation, adapting its approach based on observed evidence. It also expertly pivots between indicators of compromise (IOCs) and pulls in relevant data from across the Datadog platform by querying historical signals and logs, linking to those queries, and providing clear, contextual analysis.
After completing its investigation, Bits AI provides one of the following verdict recommendations:
Benign: No security concern detected
Suspicious: Requires further investigation
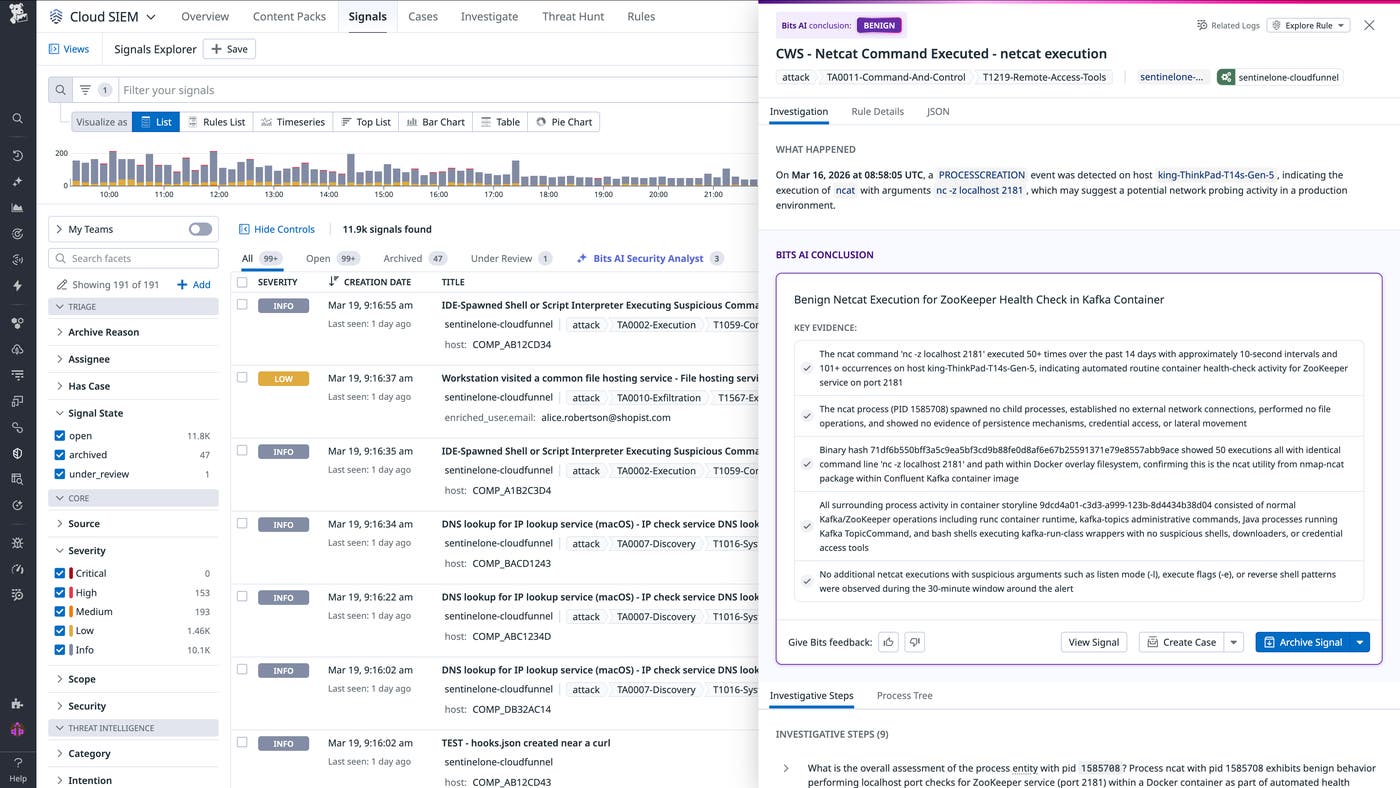
In the following screenshot, Bits AI Security Analyst investigated endpoint alerts, classified them as benign based on historical patterns of legitimate Kafka operations, and surfaced all of that context as part of its in-depth analysis.
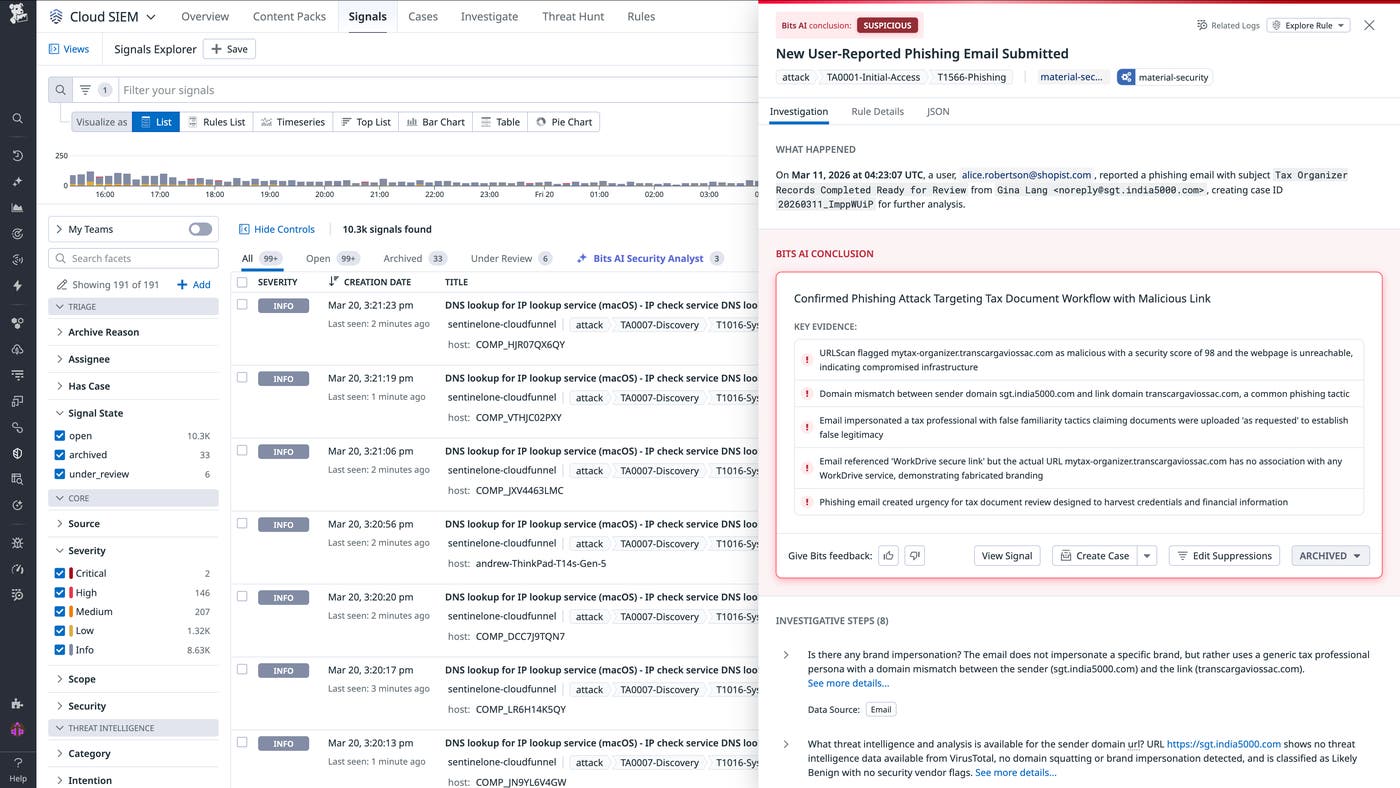
Bits AI Security Analyst will provide the same detailed analysis for suspicious activity, such as user-reported phishing attempts. As seen in the example signal below, it confirmed that a reported email was worth investigating further based on activity consistent with common phishing tactics.
The agent's reasoning at each step of its investigation and its final conclusions are thoroughly evaluated for reliability. Bits AI Security Analyst has been rigorously tested against historical datasets containing both benign and malicious signals to ensure its efficacy—and we're continuously refining its accuracy over time.
Take action to remediate suspicious signals immediately
Once you review a security signal, you can archive it, declare an incident for further investigation, edit suppressions, or run a workflow. Each option gives you a different way to respond, from archiving benign activity to automatically remediating the issue. For example, you can suspend a user flagged as suspicious by Bits AI Security Analyst by running a workflow directly from within the security signal.
Automate investigations with Bits AI Security Analyst
Bits AI Security Analyst is now generally available. Activate it in-app to get started or explore the documentation to learn more.
New to Datadog? Start a free 14-day trial to take advantage of autonomous Cloud SIEM investigations.