Lucas Masson

Max Gebhardt
In today’s complex cloud environments, security and engineering teams need to manage vulnerabilities and misconfigurations across multiple layers of the stack, including cloud resources, clusters, containers, and applications. Often, this results in a lengthy list of problems that lacks prioritization and is daunting for users to address.
Adding to the complexity, security teams often lack the ability to directly remediate vulnerabilities—they must partner with DevOps teams to address these findings at the resource level and achieve the security outcome customers expect. However, security issues are often delegated to DevOps without proper contextualization and prioritization, making prompt resolution more challenging.
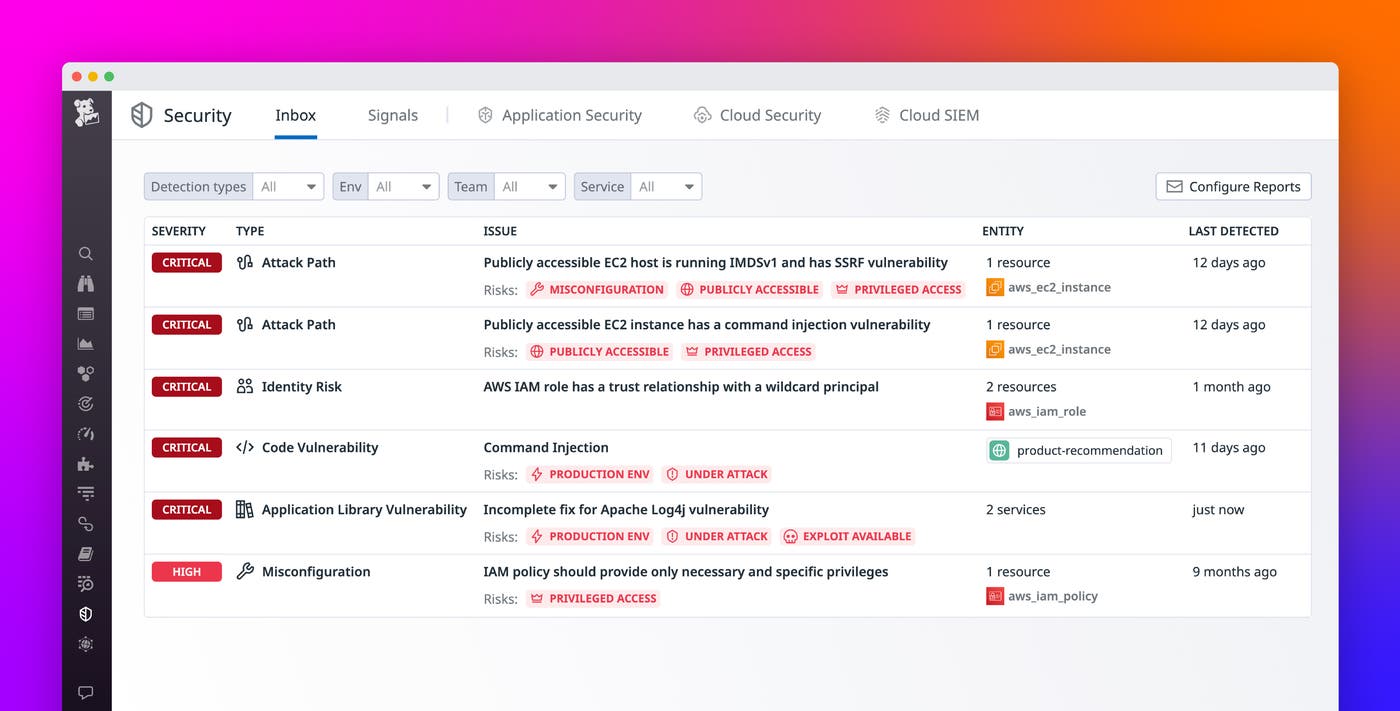
That’s why we’re excited to announce Datadog Security Inbox, a new solution within Datadog Security that is designed to equip engineering teams with actionable insights for meaningfully reducing risk. Security Inbox provides a consolidated, actionable list of your most critical security issues. It automatically gathers insights from Datadog Cloud Security and App and API Protection (AAP)—including vulnerabilities, security signals, misconfigurations, and identity risks—and consolidates them into a unified view. By contextualizing and prioritizing risks, Security Inbox helps teams identify the top actions they can take to strengthen their security posture across their cloud accounts, clusters, containers, and applications.
In this post, we’ll show you how Security Inbox enables you to:
Discover relevant risk findings
Cloud-based threats are often multifaceted, involving misconfigured cloud resources, vulnerabilities in container images, application vulnerabilities, and other weaknesses across multiple layers of the stack. Security Inbox unifies insights collected by Datadog Cloud Security and App and API Protection into a single view, simplifying the process of managing security issues.
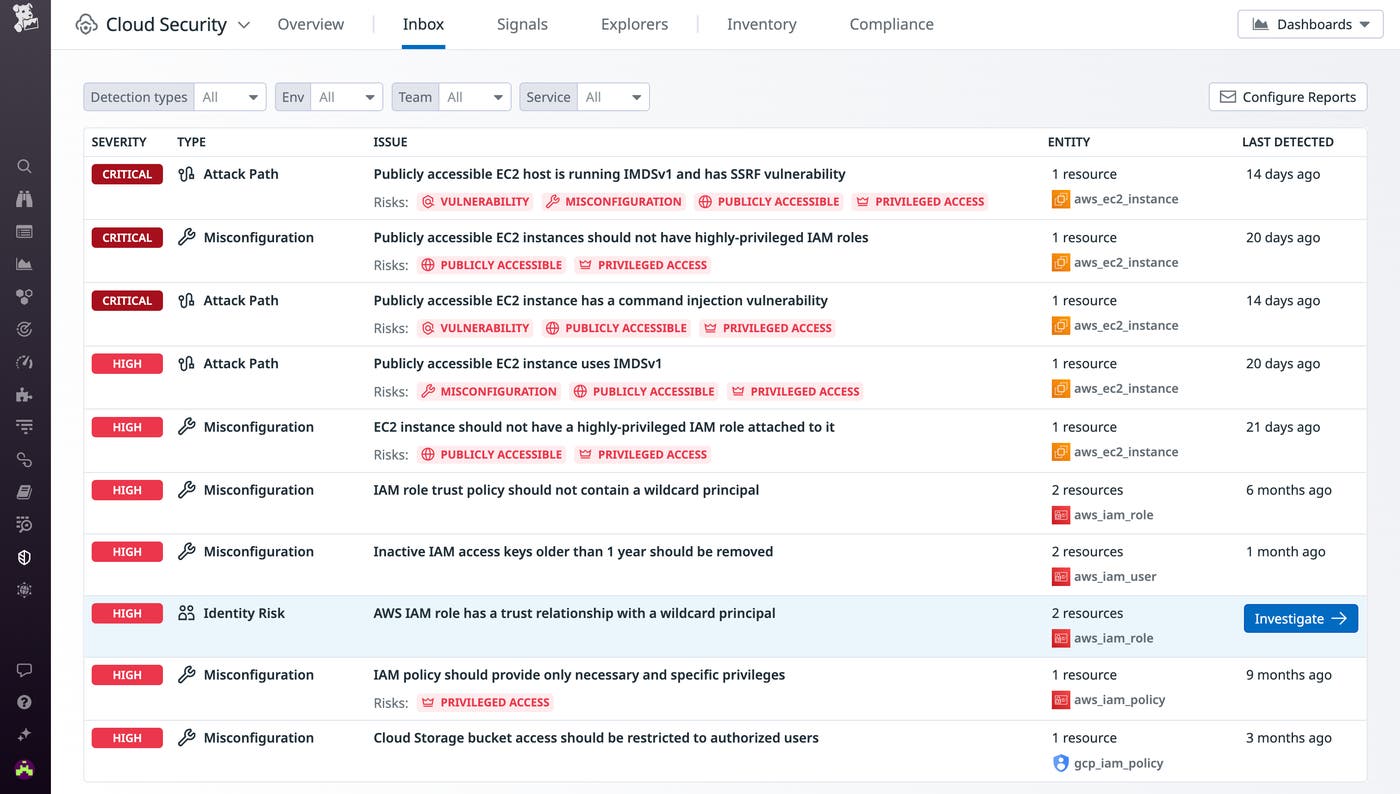
Engineers can filter this list based on their team, allowing them to view issues related to the resources they are responsible for. For example, one team may need to rightsize the permissions of a potentially risky identity and access management (IAM) role, while another might need to fix an application-layer vulnerability or upgrade a vulnerable code library on which their service depends. By selecting the team, service, or resource type specific to them, Security Inbox enables engineers to find the most pressing issues so they can take immediate action.
Prioritize risks based on severity
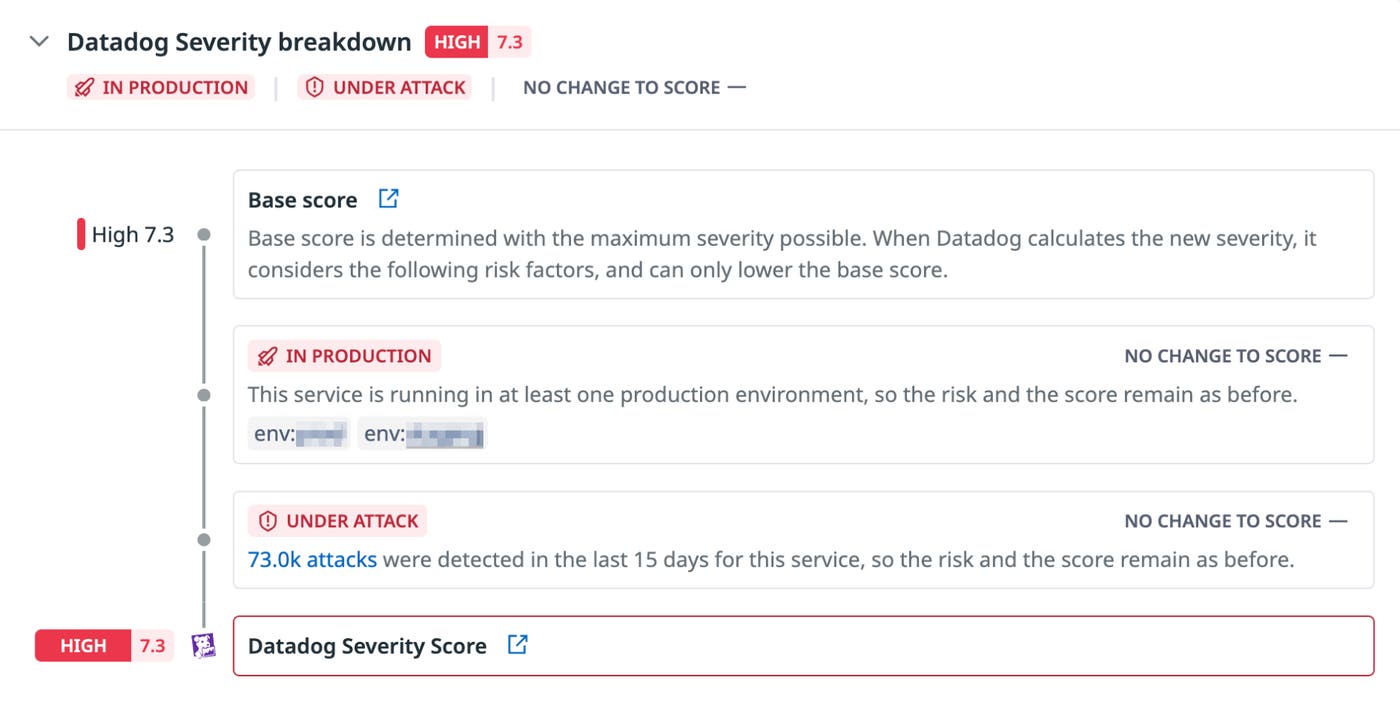
Not all issues pose the same risk. Datadog Security Inbox helps teams identify the issues that require immediate attention by providing context-based insights into risk severity.
Security findings in Datadog are enriched with attributes, such as whether the resource is publicly accessible, if the associated roles have high privileges, or if a public exploit exists. Additionally, each issue comes with context from relevant cloud logs, application traces, host activity, and other telemetry sources to help you better identify and understand suspicious activity.
Security Inbox uses this contextual data to provide a severity ranking and breakdown for each finding. This helps you concentrate on issues with a high likelihood of impact and ensure that your team prioritizes the most pressing concerns first.
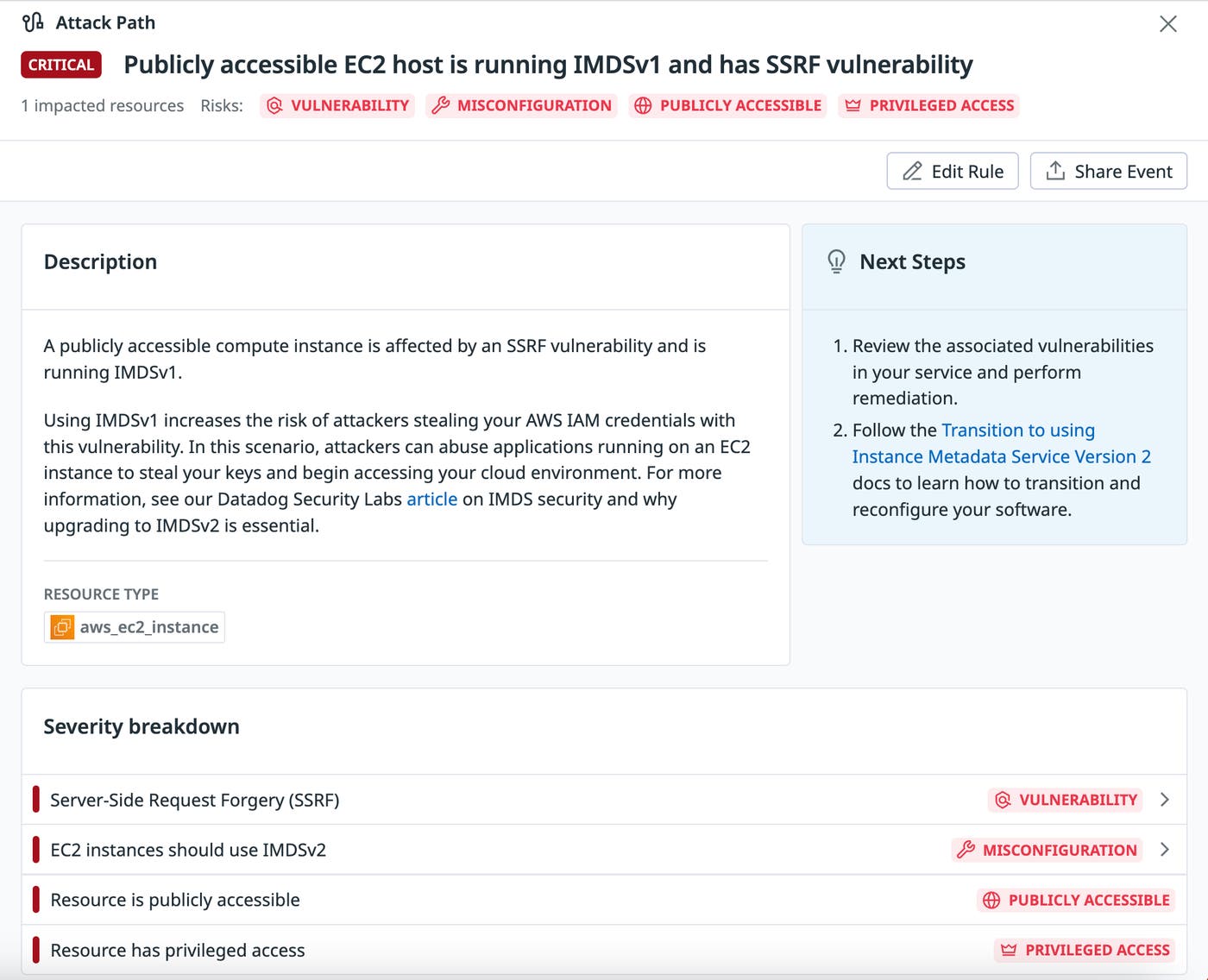
Correlate risks to detect attack paths
In cloud environments, many critical risks result from a convergence of multiple weaknesses across interconnected layers of the stack, such as storage buckets, compute resources, and applications. Datadog detects potential attack paths resulting from combinations of risks in your environment and generates a finding that appears in the Inbox whenever one is detected.
For example, an EC2 instance using IMDSv1 might not require immediate attention. However, if there is a server-side request forgery code vulnerability in the service running on that EC2, an attacker could gain access to sensitive metadata, potentially enabling privilege escalation or manipulation of security group rules. This combination of risks creates a concrete attack path, and engineering teams should address vulnerabilities in the affected cloud resources as soon as possible.
Immediate, actionable insights into critical cloud risks
With Datadog Security Inbox, you can easily surface the risks relevant to your team, prioritize issues based on potential impact, and identify attack paths stemming from multiple, correlated weak points. These capabilities enable security and engineering teams to easily remediate urgent security risks, save time triaging and responding to issues, and improve security posture.
Check out our documentation to learn more, or go to your Security Inbox to get started. If you don’t already have a Datadog account, you can sign up for a 14-day free trial today.