Bhavin Patel

Mallory Mooney
Datadog provides you with a comprehensive and highly customizable platform for monitoring the performance and security of your applications. Through Datadog components deployed in your environment—including the Agent, tracing libraries, and Observability Pipelines workers—you can easily configure monitoring across your hosts and services, regardless of the particular technology you’re using. But depending on the size of your environment, it can be challenging to manage all of your components’ configurations. That’s why we now offer even more customization options for Datadog monitoring—with the introduction of Remote Configuration.
Remote Configuration enables you to remotely configure the behavior of Datadog components deployed in your infrastructure for a select set of product features. With the ability to apply real-time Datadog component configurations, you can:
Receive protection configuration updates to block IPs, authenticated attackers, and suspicious requests for App and API Protection (AAP)
Update security detection rules for Workload Protection
Instrument tracing libraries and set Agent sampling rates for Application Performance Monitoring (APM)
Configure Observability Pipelines Workers
Capture data from live applications for Dynamic Instrumentation
Together, these features allow you to strengthen your overall security posture, decrease management costs, and shorten resolution times. We’re excited to announce the availability of both Remote Configuration and supported features for Datadog AAP.
Now it’s easier than ever to get real-time protection from attacks that target your web applications and APIs. In this post, we’ll show you how to enable Remote Configuration, which is a prerequisite to using it with our security products. Then we’ll walk through how to configure its supported features for Datadog AAP and Workload Protection.
Get started with Remote Configuration
Components with Remote Configuration enabled are designed to periodically poll Datadog for configuration updates and then automatically apply them to your environment—without the need for additional inbound access. To use these features, you first need to enable Remote Configuration for your organization, then add a small line of code to your Datadog components’ configuration files. We will focus on configuring Agents and tracing libraries in this post, which is necessary for using Datadog AAP. As a prerequisite, version 7.41.1+ of the Datadog Agent is required for Remote Configuration. For AAP, you also need to upgrade your tracing library.
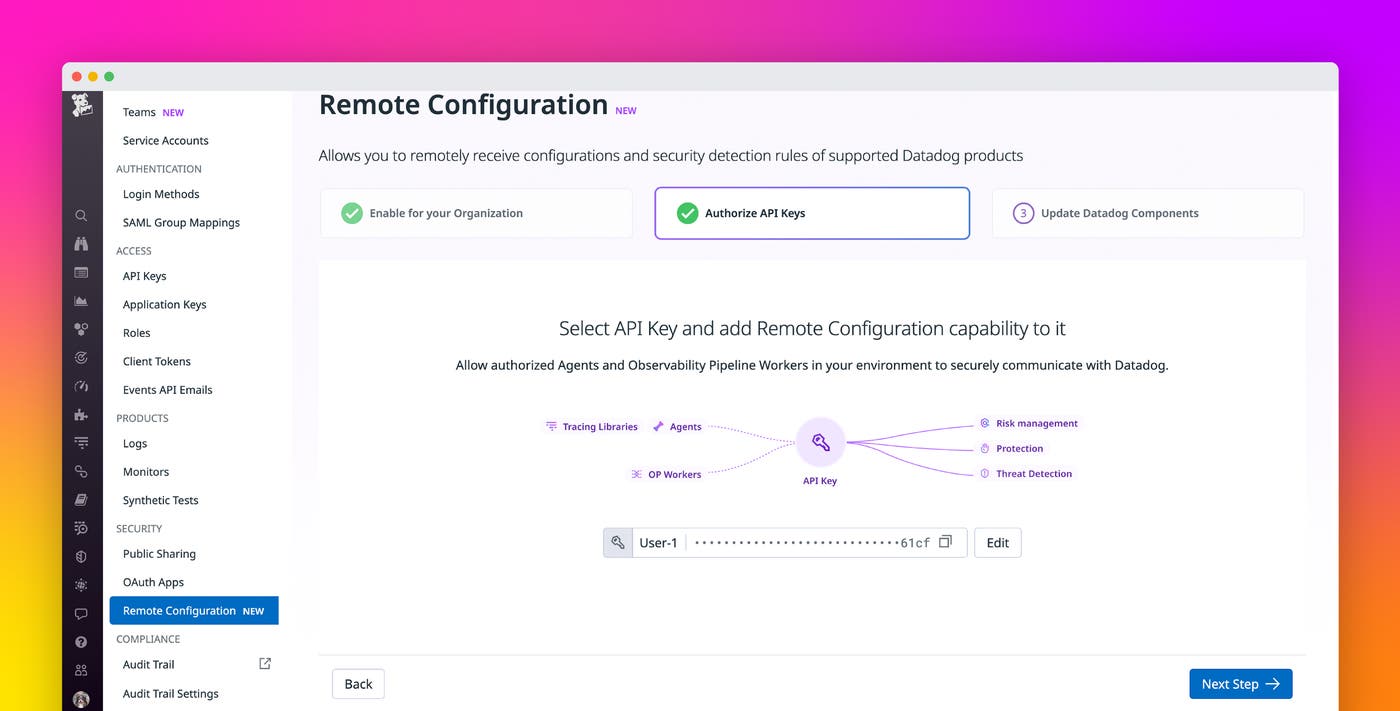
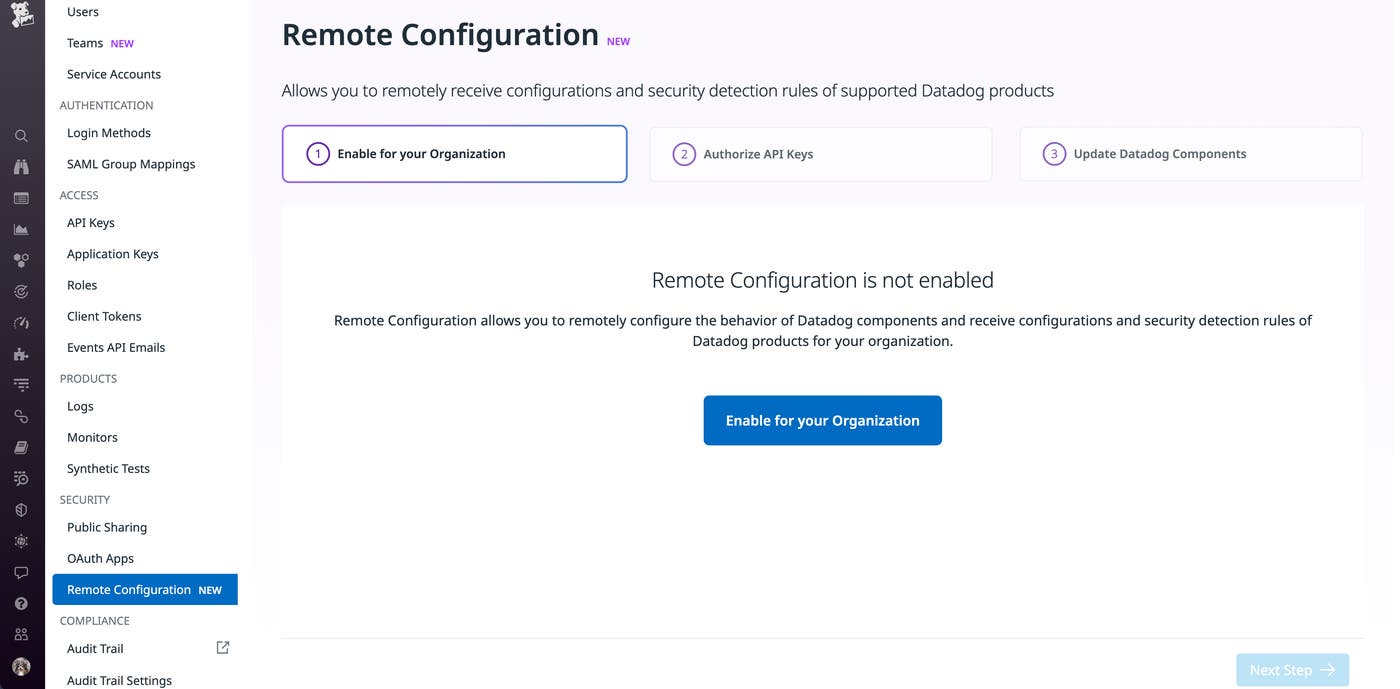
To get started, enable Remote Configuration from your organization’s settings page:
Then follow the in-app setup instructions to either create a new API key or select an existing one and enable Remote Configuration for it. This step allows Datadog to authenticate and authorize your Agent to receive configuration updates. Next, add the following snippet to your Agent’s datadog.yaml file to enable Remote Configuration locally:
api_key: xxxremote_configuration: enabled: trueWith this step, the Agent will periodically send configuration requests to Datadog. Finally, restart the Agent to apply these changes to your environment and activate Remote Configuration. This prepares your environment to use the supported features, such as those provided by Datadog AAP.
Enable Datadog AAP’s Protection capabilities
Datadog AAP’s Protection capabilities enable your teams to instantly block attackers (including authenticated ones) and their attempts to access your environment, giving them the time they need for further investigation and remediation. To begin, navigate to AAP’s configuration page and enable it for your services:
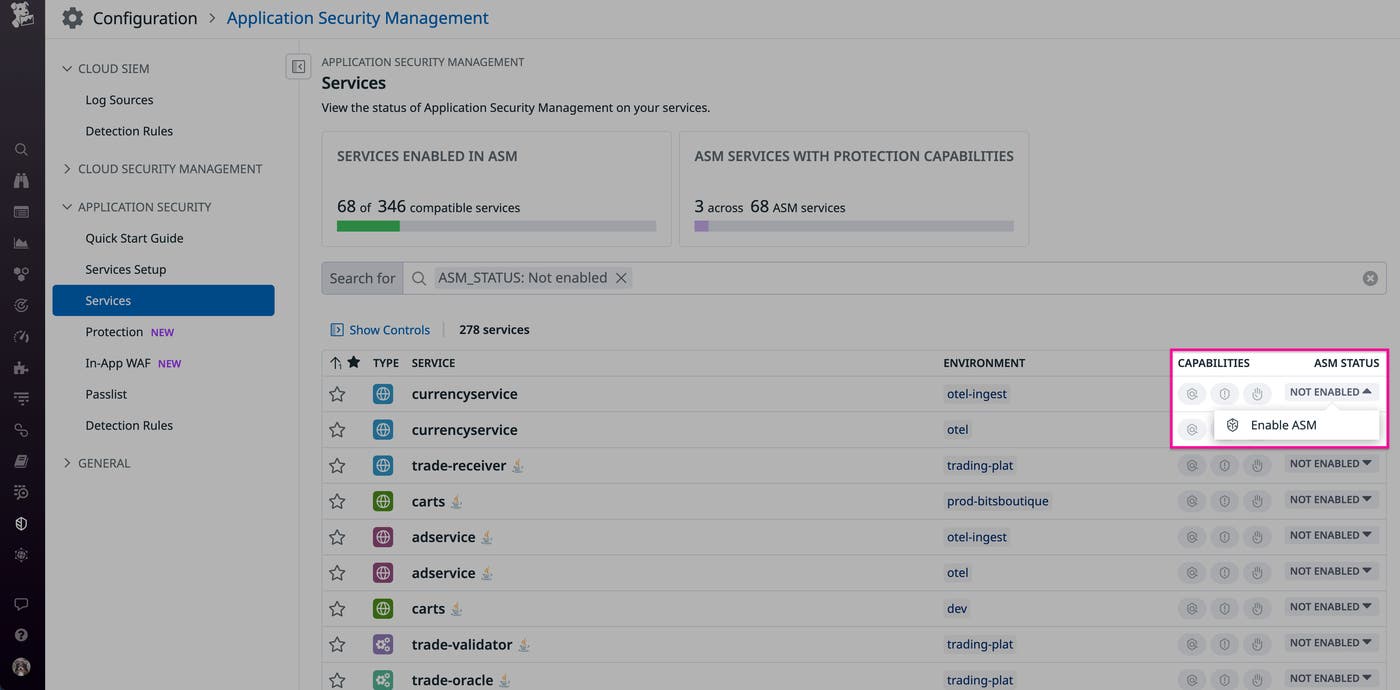
Once AAP is enabled, you can configure and deploy changes to your Datadog components directly from the UI for services that have Remote Configuration enabled.
Send configuration and rule updates to AAP’s In-App WAF
When Datadog releases an update to its in-app web application firewall (WAF), such as rules to detect new attack patterns, your configured tracing libraries will automatically receive them via Remote Configuration. This enables you to easily create and deploy custom policies for your environment, such as one that blocks traffic from malicious scanners:
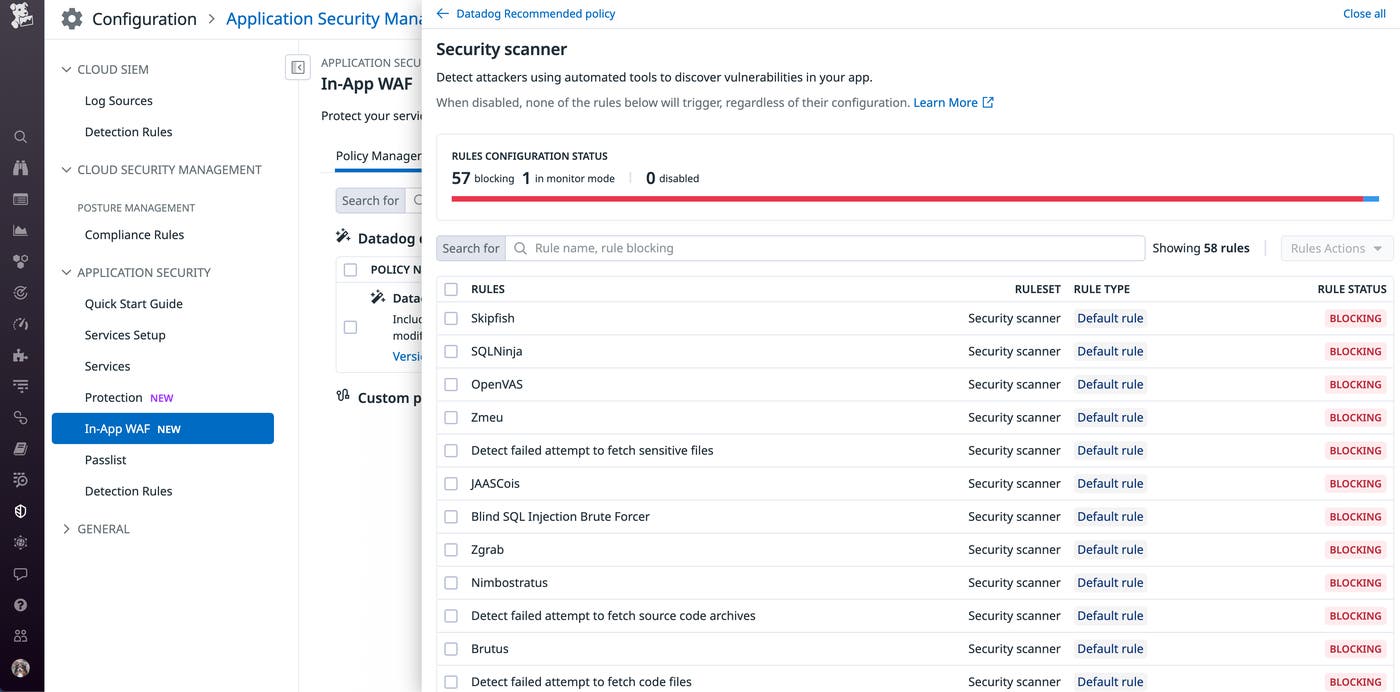
You can apply this policy for all services or only a subset. Once configured, Datadog will automatically deploy the policy via your Remote Configuration-enabled Agents and tracing libraries.
Issue blocking commands directly from the Datadog UI
In addition to instantly applying WAF policies to your services, Datadog AAP allows you to automatically block suspicious requests. When you block an attacker from an AAP security signal, your Remote Configuration-enabled tracing library will automatically receive the blocking command and intercept associated requests. For example, if you identify an attacker IP attempting to launch a scanner, you can block it from a signal before it accesses your environment:
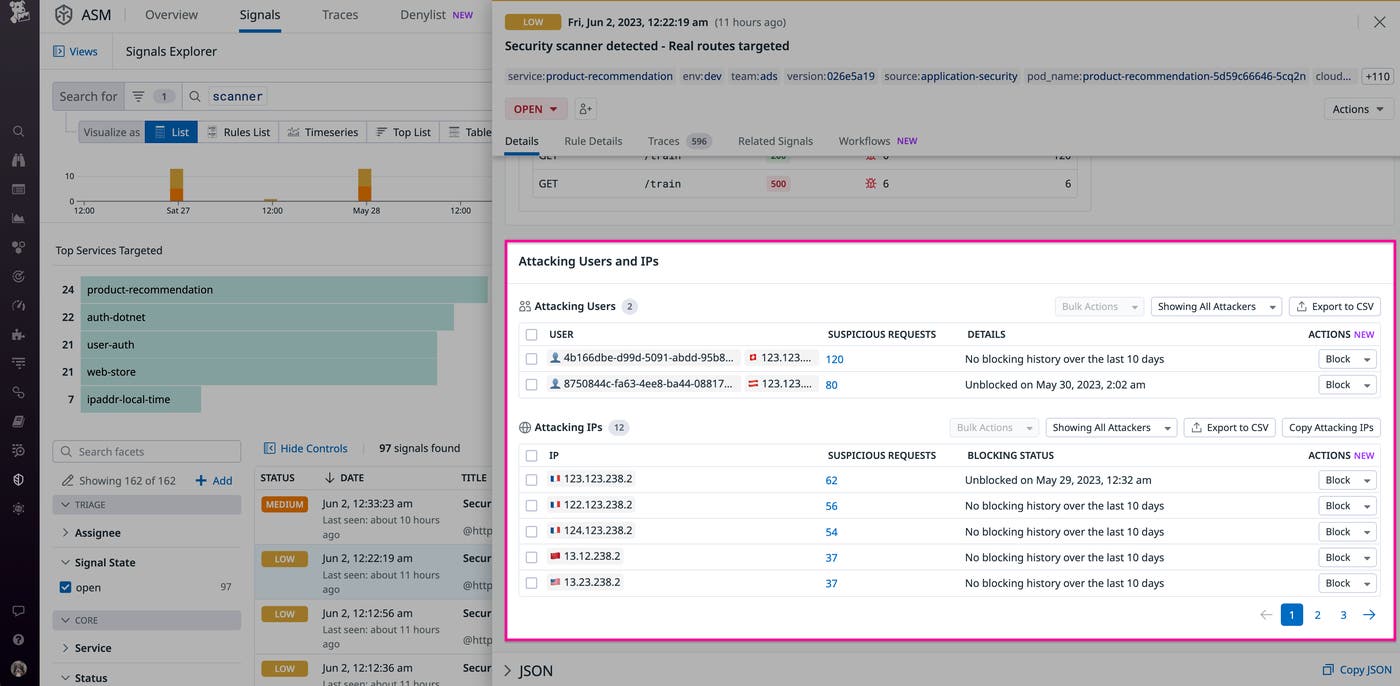
This capability helps you protect critical services from attacks on demand, instead of needing to update network firewall rules or other parts of your infrastructure.
Automatically keep your Workload Protection rules up to date
Datadog Workload Protection detects real-time threats to your production workloads by leveraging the Datadog Agent to monitor file, process, and network activity across your environments. As part of our security offering, we regularly deploy new and updated detection rules in order to maintain their fidelity and ensure that our customers can detect the latest attack scenarios. But manually downloading and deploying Agent updates can be complicated and time consuming.
Remote Configuration for Workload Protection eliminates these pain points by automatically deploying rule updates to each of your Agents as soon as they are available. This ensures that you always have the latest Agent rules to keep your environments protected against an evolving threat landscape.
To get started, after you’ve enabled Remote Configuration in the app, you will need to modify the deployment configurations of your Agents to start receiving rule updates. To do this, you can update the datadog section of your Agents’ values.yaml files with the following snippet:
datadog: remoteConfiguration: enabled: true securityAgent: runtime: enabled: trueTo learn more, check out our documentation about setting up Remote Configuration for Workload Protection for other deployment configurations, such as Kubernetes operators, AWS Elastic Beanstalk, and Docker. Note that this capability applies to the out-of-the-box Agent rules that Datadog manages—not custom rules.
Streamlined security monitoring for your environments
Remote Configuration allows you to easily configure the behavior and functionality of your Datadog components on demand and enhances Datadog product features. This enables you to significantly decrease your management costs and time to resolution in addition to strengthening your overall security posture. Check out our documentation to learn more or enable Remote Configuration for your environment. If you don’t already have a Datadog account, you can sign up for a 14-day free trial today.