Shreya Batra

Kyra Abbu

Elia Camposilvan

Andréa Piazza

Vera Chan
Recorded Future provides real-time threat intelligence about indicators of compromise (IOCs), including malicious IP addresses, domains, and vulnerabilities. It also adds context on threat actors and campaigns to help security teams understand which signals represent real risk and prioritize their responses accordingly.
Datadog supports threat intelligence through capabilities such as Bring Your Own Threat Intelligence (BYOTI) and built-in threat feeds. The Recorded Future integration, our first threat intelligence integration, builds upon this foundation by delivering threat intelligence in Datadog without the overhead of managing custom feeds. It automatically enriches security logs with context such as risk scores and threat associations, enabling faster triage and more confident responses to threats.
In this post, we’ll cover how the integration helps you:
- Continuously enrich logs with Recorded Future threat intelligence feeds
- Capture Recorded Future Classic Alerts and Playbook Alerts in Datadog
- Correlate threat intelligence with Datadog Cloud SIEM signals
- Get started quickly with the Recorded Future Content Pack
Continuously enrich logs with Recorded Future threat intelligence feeds
Recorded Future provides threat intelligence feeds that include live risk lists for IP addresses, file hashes, and domains. Datadog pulls these feeds directly into the platform and ingests the top 100,000 threats per category. It focuses on indicators that have a Recorded Future risk score above 65 and uses this data to continuously enrich security logs.
When a log event references a known malicious IP address or suspicious file hash, Datadog automatically surfaces the relevant context alongside the event. Indicators are refreshed on Recorded Future’s recommended cadence to keep enrichment data current as threat activity changes over time.
Capture Recorded Future alerts in Datadog
In addition to enrichment, the integration brings Recorded Future Classic Alerts and Playbook Alerts into Datadog. These alerts represent externally generated detections based on Recorded Future’s intelligence. Examples include suspicious infrastructure, emerging threats, and activity tied to known campaigns.
By ingesting these alerts directly into Datadog, you can investigate the corresponding signals alongside your application and infrastructure telemetry data. The unified Datadog view makes it easier to correlate external threat signals with internal activity, determine whether an alert is relevant to your environment, and take action without switching tools.
Correlate threat intelligence with Cloud SIEM signals
The integration delivers its deepest value by correlating Recorded Future intelligence with Cloud SIEM signals. Teams can more easily detect and prioritize malicious activity that might otherwise blend into background noise.
For example, a web application log might show repeated authentication attempts from a single IP address. On its own, this activity could look like routine scanning. But when that IP address matches a Recorded Future indicator that has a high risk score or is associated with active threat activity, Datadog enriches the event with that context. Cloud SIEM out-of-the-box (OOTB) detection rules then use that context to elevate the signal, helping analysts focus on activity that is more likely to represent a real threat. You can investigate and respond faster, without manual enrichment or triage.
Bits AI automatically uses this context to speed up triage, and you can analyze related activity for those indicators in the IOC Explorer.
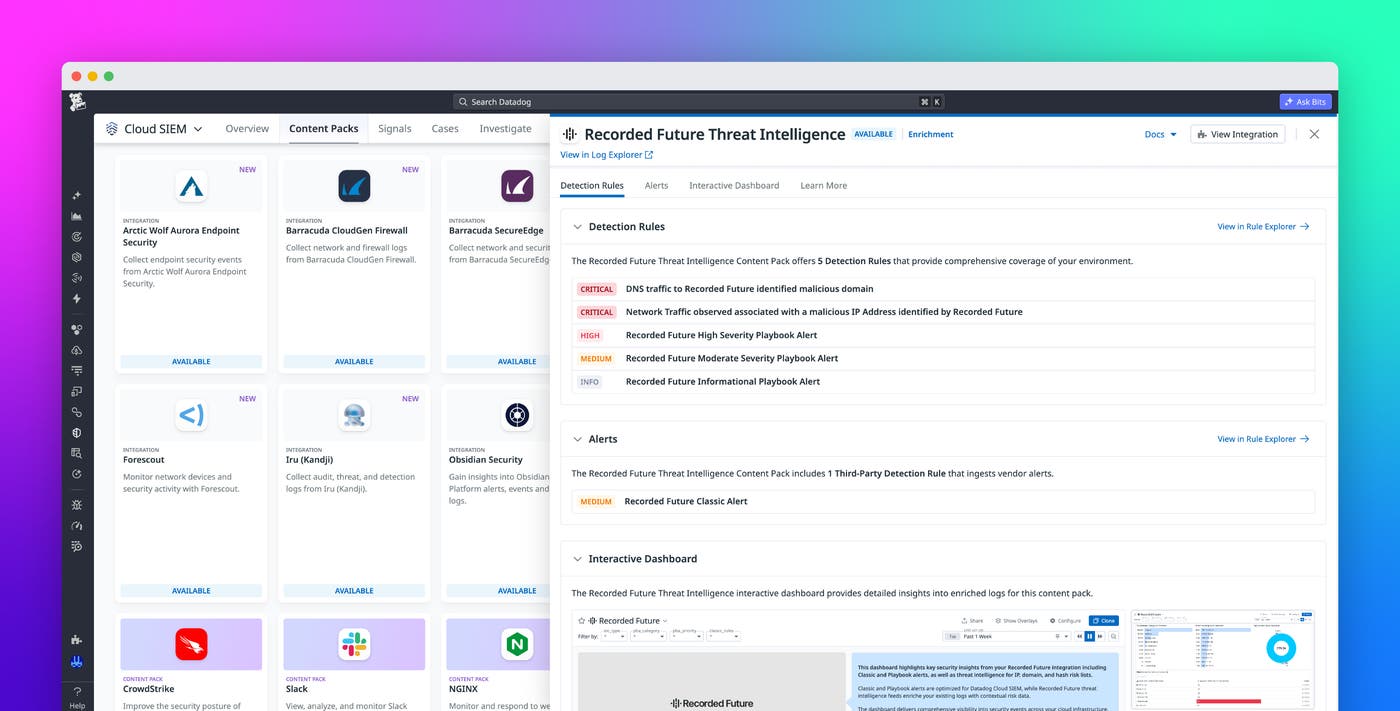
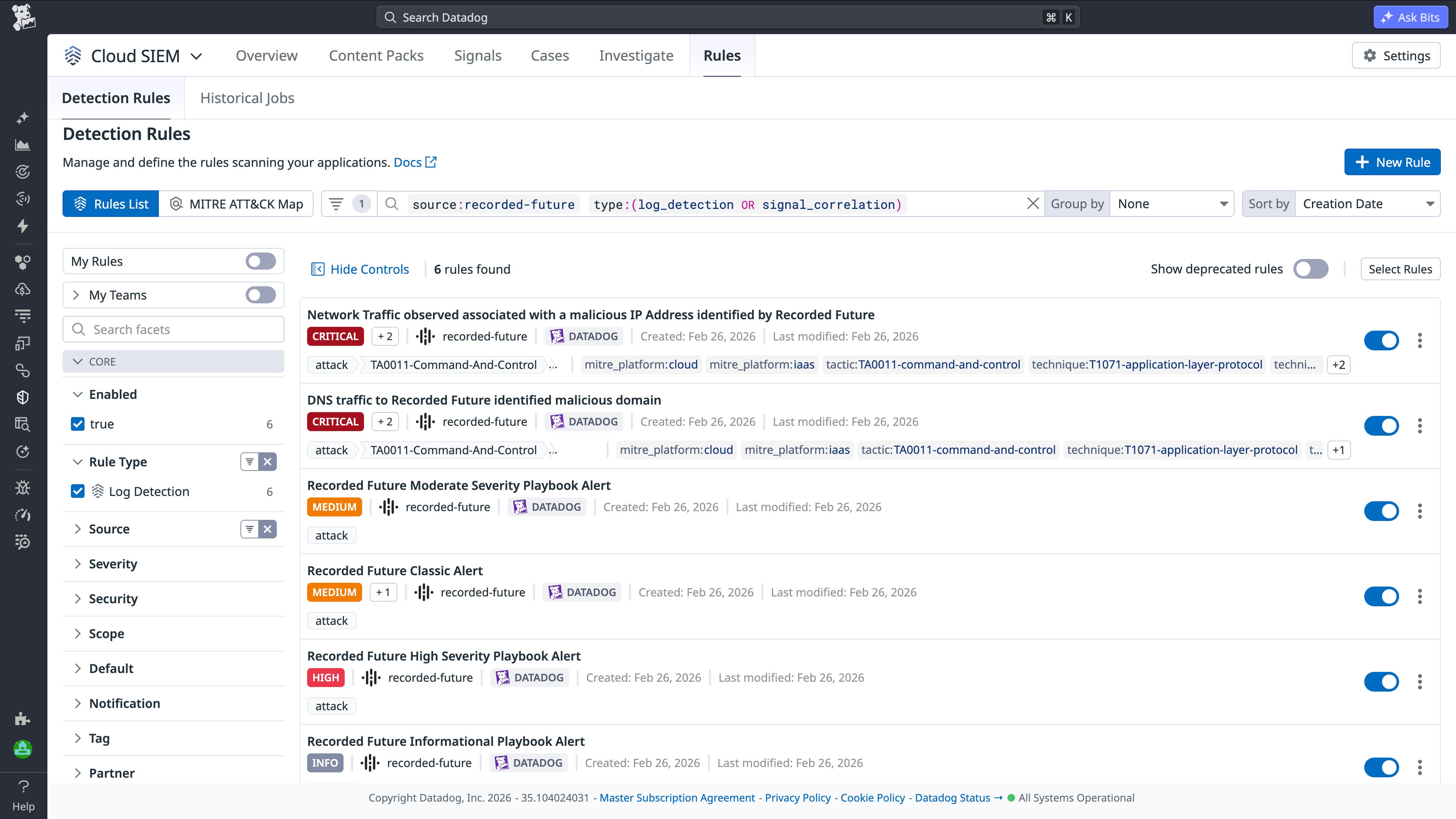
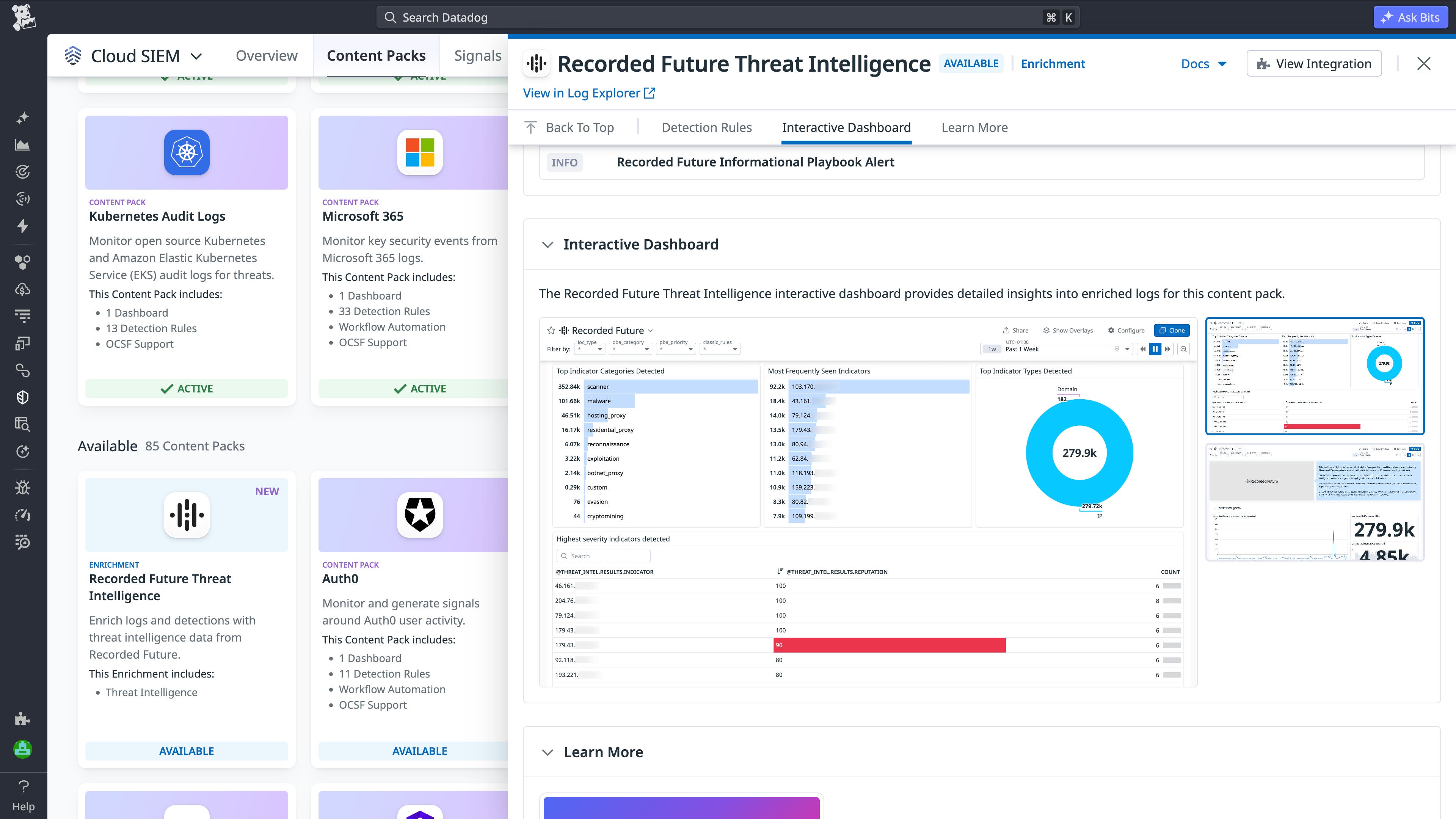
Get started quickly with the Recorded Future Content Pack
To help teams get started quickly, we’re introducing the Recorded Future Content Pack for Cloud SIEM. The Content Pack includes six OOTB detection rules that use Recorded Future intelligence to identify malicious DNS activity, suspicious IP traffic, and Recorded Future alerts across severity levels for prioritized threat response.
The Content Pack also includes prebuilt dashboards that consolidate Recorded Future alert activity and threat feed data into a unified view. The dashboard view helps analysts quickly understand what types of threats are showing up most frequently in their environment and how risky these threats are.
The dashboard shows:
- Types of activity, such as scanning, malware behavior, proxy traffic, and reconnaissance
- Specific IP addresses and domains that appear frequently, which are often a strong signal of persistent or automated activity
- Top indicator types detected (for example, domains vs. IP addresses)
- IP addresses with the highest risk
- Frequency and classification of indicators
You no longer have to manually correlate threat intelligence with logs. Datadog automatically enriches your security data and prioritizes relevant signals in one place.
Get started with Recorded Future in Cloud SIEM
Recorded Future threat intelligence in Datadog Cloud SIEM helps teams strengthen their security posture with unified, actionable context. By combining threat intelligence and security signals in one platform, teams can speed up investigations and respond more effectively. To set up the integration, check out the Recorded Future integration documentation. You can also get started with the Content Pack.
If you’re new to Datadog, you can sign up for a free 14-day trial.