
Mike Milner
Below is a guest post from Mike Milner, CTO and Co-Founder at IMMUNIO.
IMMUNIO provides real-time detection and defense against attacks for your web applications. For most popular web frameworks, IMMUNIO installs in two minutes, and protects you from account takeover attacks such as brute force and credential stuffing, as well as code vulnerabilities like XSS, SQL injection, and arbitrary file access.
IMMUNIO + Datadog
Now IMMUNIO has partnered with Datadog to integrate real-time security intelligence into the other operational data Datadog provides about your cloud environment and applications. This integration makes your existing Datadog monitoring even more powerful. By using IMMUNIO with Datadog, you gain critical insights into how attacks are affecting your system—and you get the tools you need to stop those attacks immediately.
The data provided by your IMMUNIO integration with Datadog will help you gain a clearer sense of what’s normal for your system and your apps—so you can quickly identify abnormal activity, determine whether it’s malicious, and take immediate action.
For example, with IMMUNIO you can:
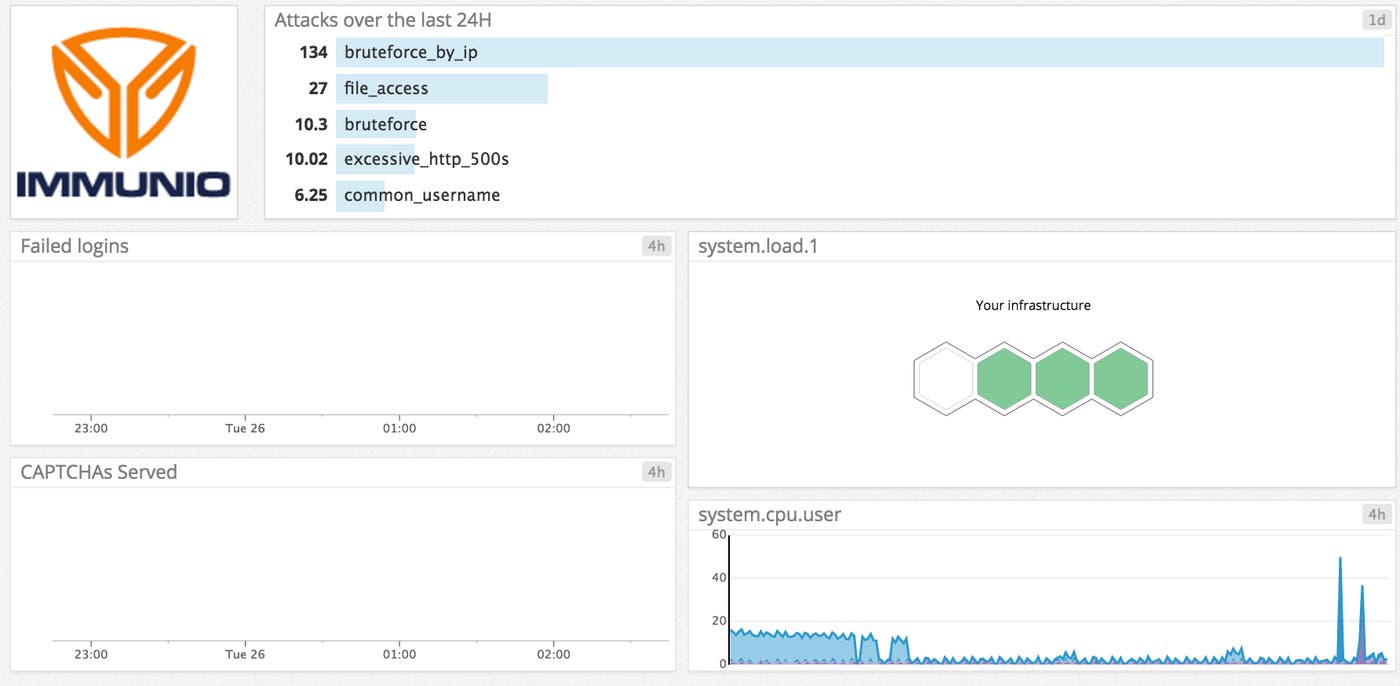
- Correlate CPU usage spikes with a brute force login attack
- Diagnose database query latency by matching to a blind SQL Injection attack
- Use IMMUNIO to stop bots by automatically serving CAPTCHAs, and set a Datadog alert based on number of CAPTCHAs served.
IMMUNIO can also:
- Prevent cross-site scripting (XSS) attacks from poisoning your web application templates and infecting your customers with malware
- Stop exfiltration of sensitive data by hardening your application against common injection attacks such as SQLi (SQL injections and remote command execution)
- Accelerate your response to publicly disclosed vulnerabilities in third party components and zero-day attacks
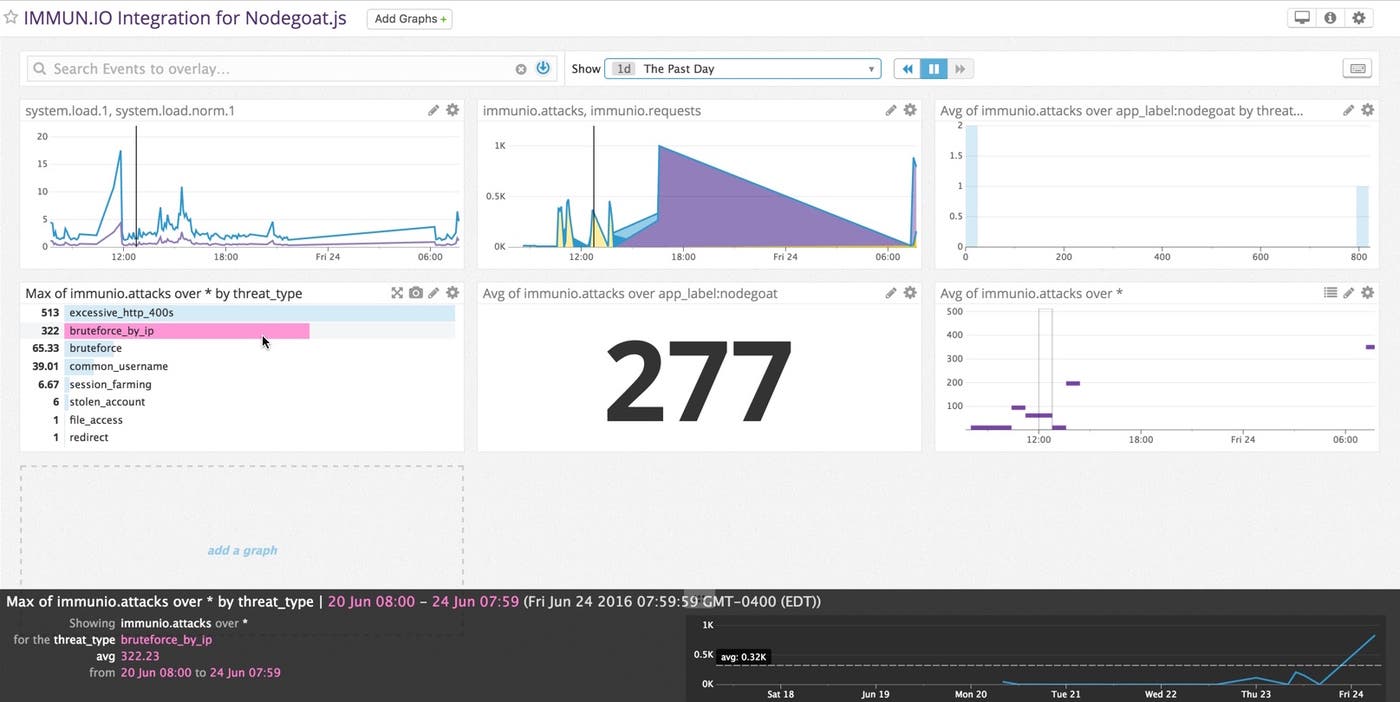
Here are the metrics that are available in Datadog:
immunio.requests: count of all requests seen by the IMMUNIO agent (the same values we bill against)immunio.attacks: count of all attacks, tagged with the attack type so they can be segmentedimmunio.mitigate.captcha: count of all captchas served by the IMMUNIO agentimmunio.mitigate.blocked: count of all requests that were blocked with a 403 Forbidden
Correlate to pinpoint root causes
For example, let’s look at how IMMUNIO metrics can be correlated with CPU usage. A normal baseline for CPU usage might be 20 percent of capacity, but if you have numerous spikes of near-100 percent capacity over the course of a day, this could indicate an attack taking place. But a machine malfunctioning or a sudden uptick in the number of users simultaneously accessing the system could also be to blame. With IMMUNIO’s capabilities integrated into Datadog, you can instantly pinpoint the cause. You have instant visibility via a single, integrated dashboard.
Agile software development processes have solved many problems for developers, but there’s still the challenge of keeping applications secure within production environments. Resource and time constraints mean organizations are finding it more difficult than ever to keep development on schedule without sacrificing application security.
With the emergence of DevSecOps methods and processes, for the first time, organizations can integrate security into every phase of the application development lifecycle.
Getting started with IMMUNIO
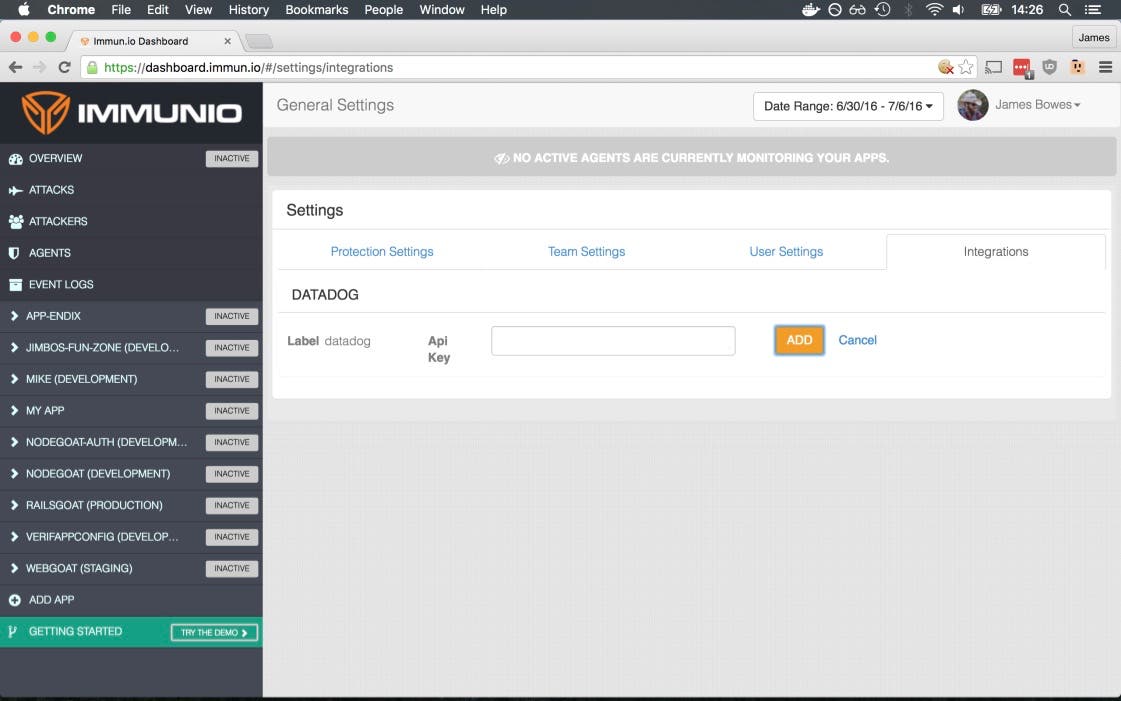
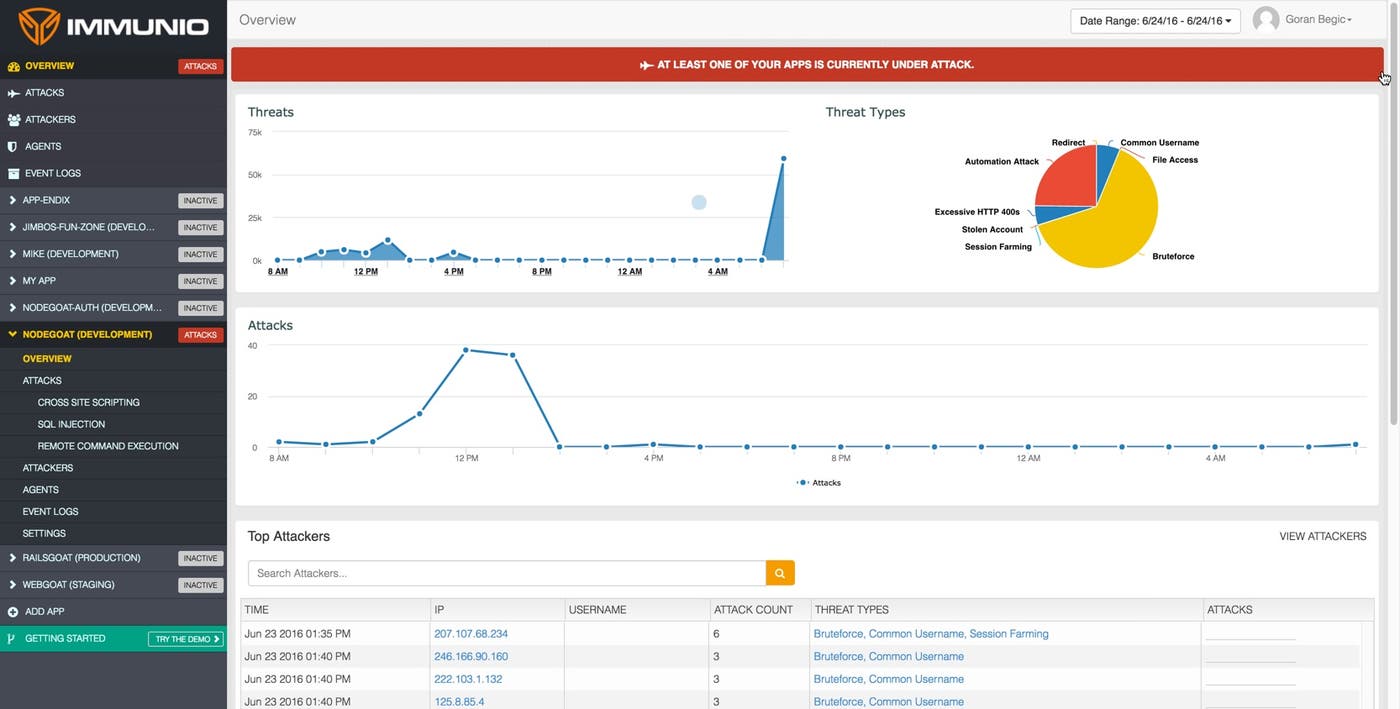
As seen in the above screenshot, getting started with the IMMUNIO integration is as simple as adding in your Datadog API key. And as seen below, clear, easy-to-use dashboards give you a comprehensive view of identified attacks broken down by type, time of day, and other critical metrics—giving your team the best available tools to protect your apps, even at runtime.
With IMMUNIO’s technology, companies can release apps into production, secure in the knowledge that those applications will be immune to exploitation and that vulnerabilities can be quickly and efficiently remediated. IMMUNIO addresses application security from the inside, monitoring to detect application layer attacks and other vulnerabilities, and immediately blocking unwanted activity in real time.
It’s the promise of DevSecOps put into practice: one integrated, single point of visibility into code as it’s being written by developers, tested, deployed, and along all the other steps of the software “manufacturing” process as code proceeds into production.
*If you’d like to learn more about the IMMUNIO-Datadog integration, you can watch the “How to View Real-Time Web Application Security Data in Datadog” on-demand webinar with Mike and Ilan. Watch now. *





