Bowen Chen
AWS Verified Access makes it easy and more secure for organizations to grant local or remote access to corporate applications without the use of a VPN. By using Verified Access, you can assign group policies to manage your organizations’ application access and administrative privileges at scale.
As a SIEM partner for the launch of AWS Verified Access, we’re pleased to announce that you can now integrate Verified Access logs with Datadog Cloud SIEM for analysis and real-time threat detection. You can monitor suspicious application access attempts with three Cloud SIEM detection rules for Verified Access and leverage Datadog’s out-of-the-box (OOTB) authentication dashboard to identify anomalous patterns.
In this post, we’ll cover how you can visualize authentication activity and investigate Verified Access logs in Datadog. We’ll also discuss how to enhance your security coverage and trace the footprint of malicious actors using Cloud SIEM Investigator and detection rules.
Detect suspicious trends in application authentication activity
As users across your organization access multiple applications on a daily basis, they generate large volumes of authentication logs that can be difficult to effectively monitor. To help you get insights into AWS Verified Access activity, Cloud SIEM will automatically analyze all of your Verified Access logs in real time and evaluate them against three out-of-the-box detection rules. Cloud SIEM uses these rules to generate a security signal when it detects an anomalous number of failed application authentication attempts from a host, user, or IP address.
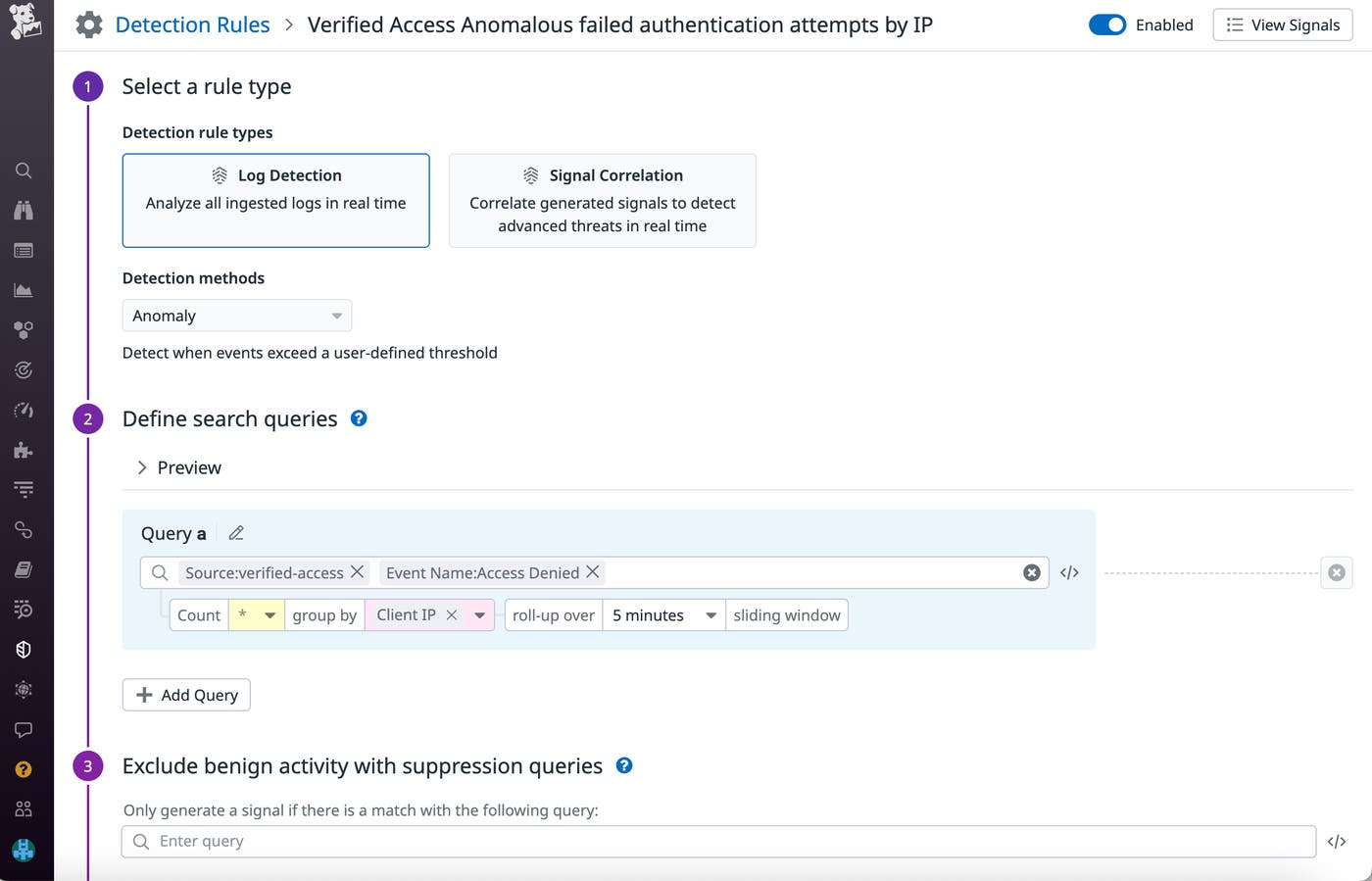
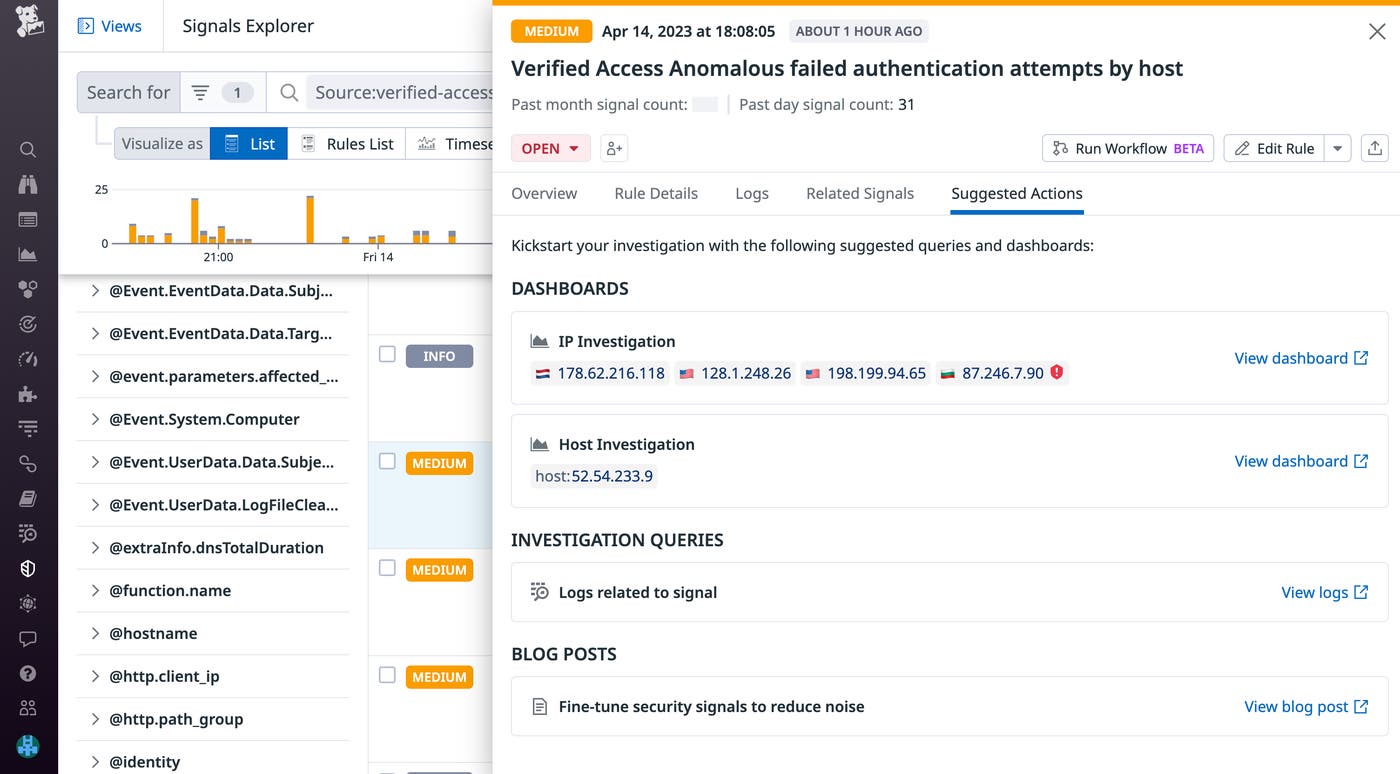
After a signal is generated, you can investigate by inspecting it in the Signals Explorer. Each signal includes context regarding its origins, such as the geolocation and domain of the failed authentication attempt. You can then follow the recommendations linked in the “Suggested Actions” tab to continue investigating by viewing a dashboard for the affected host machine or logs relating to the signal.
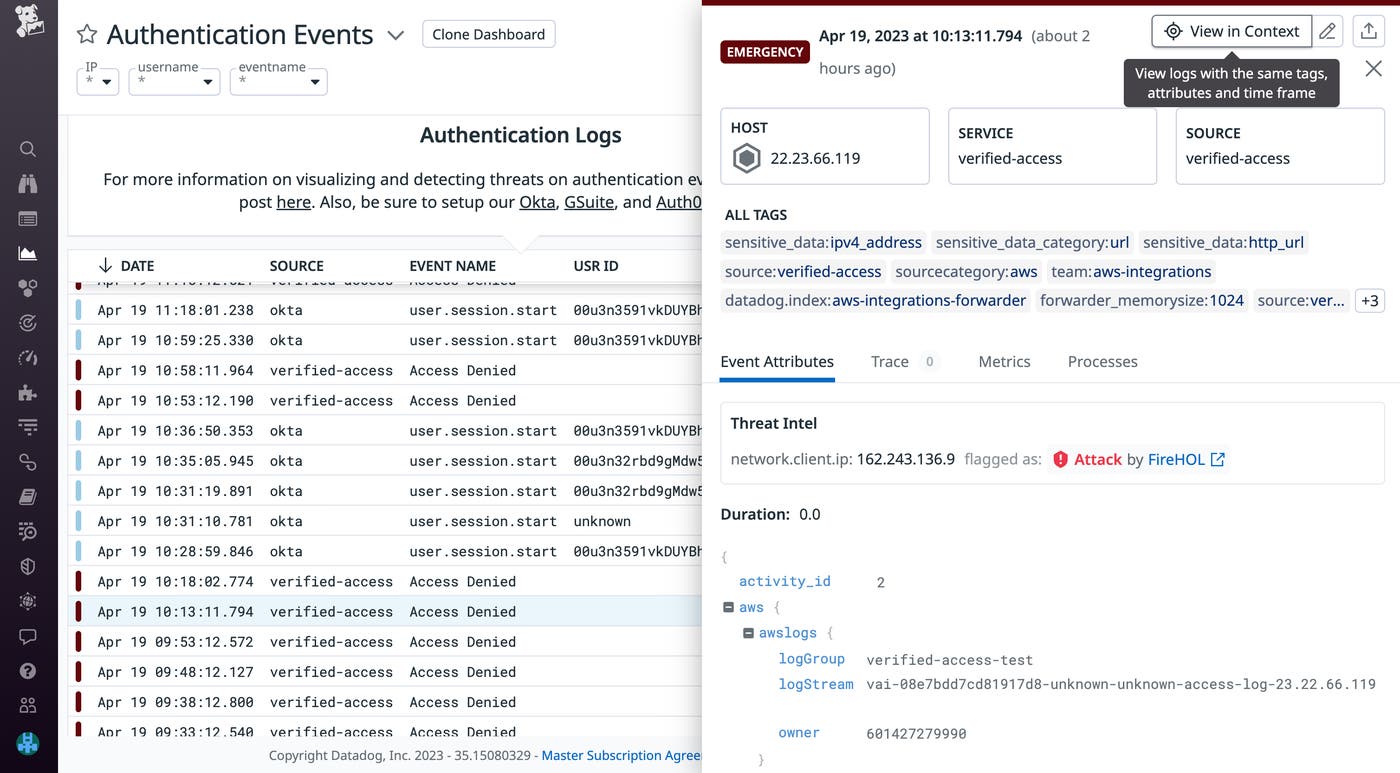
The Authentication Events dashboard helps you visualize trends in Verified Access security signals alongside other authentication-related events across all your applications.
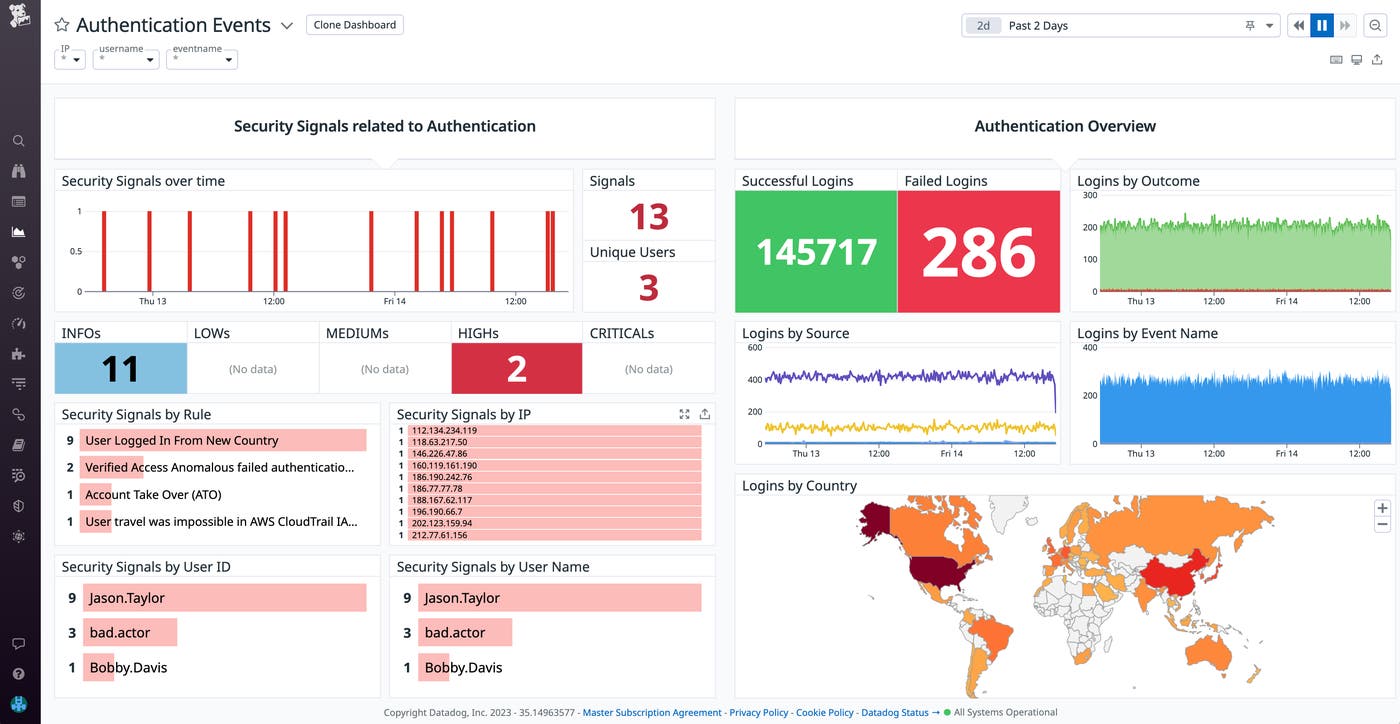
If you want to investigate a recent application authentication attempt rejected by Verified Access, you can inspect it from the log activity widget in the dashboard. Clicking “view in context” enables you to view other Verified Access logs generated in the same time frame, from the same host.
Trace malicious actors with Datadog Cloud SIEM
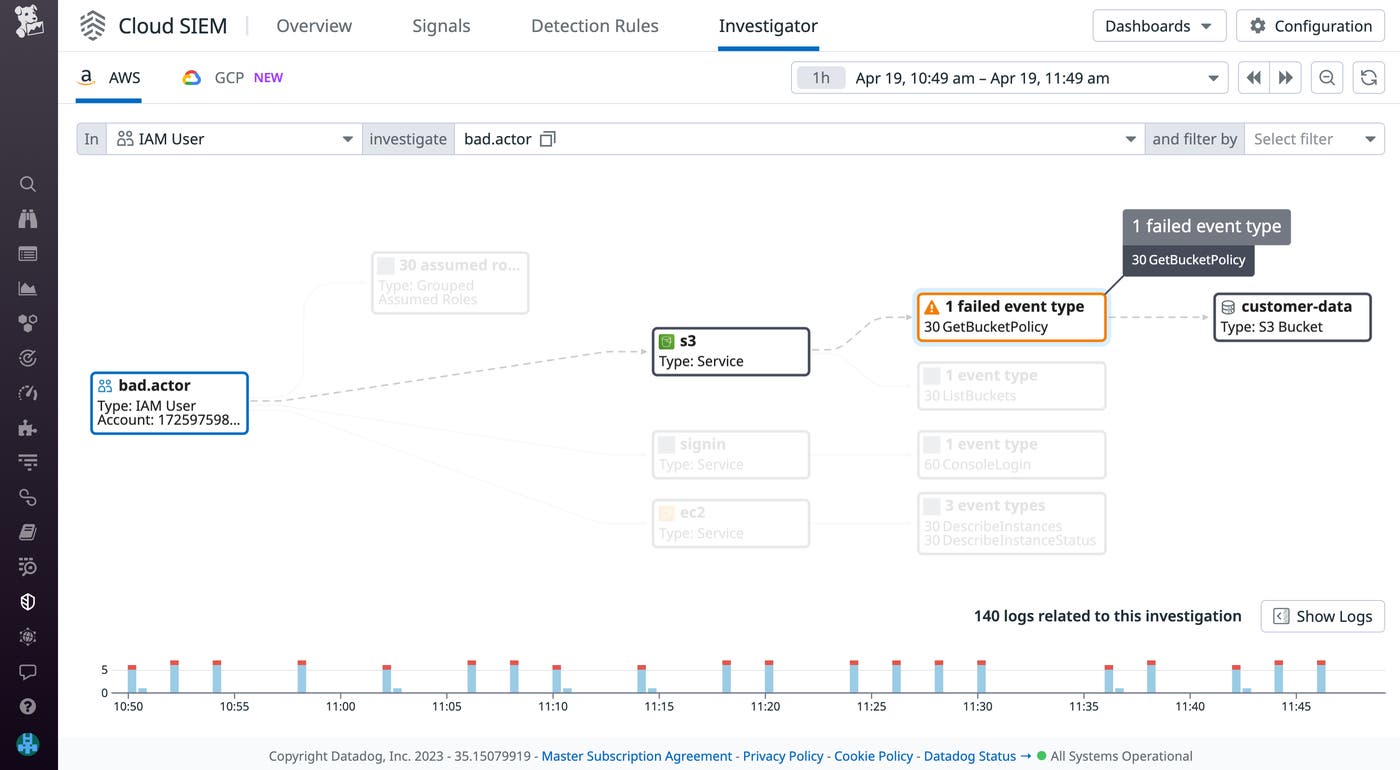
Verified Access detection rules generate security signals that can alert you to malicious entities attempting to breach your system. But once their activity is detected, you'll still need to investigate the scope of the impact. After identifying a compromised IAM user or role, you can use Cloud SIEM Investigator to track their recent digital footprint across your AWS infrastructure. Investigator enables you to better visualize the scope of services impacted in data breach incidents and failed event types that could indicate a malicious actor’s objective. By using the Investigator for context, DevOps engineers can quickly coordinate with security teams to verify whether the failed events were false positives (from activity such as load testing) or truly stemmed from compromised credentials.
Get started with AWS Verified Access and Datadog
AWS Verified Access allows organizations to securely connect employees to corporate applications. As part of our ongoing security and observability partnership with AWS, Datadog’s Verified Access integration enables you to increase visibility across your infrastructure and take immediate action if a breach occurs. You can also leverage our Security Lake integration to forward Verified Access logs to Datadog, where they can be analyzed by Cloud SIEM. To learn more about the Verified Access integration, you can view our documentation.
If you don't already have a Datadog account, sign up for a free 14-day trial today.