Partha Naidu
Product Manager
クラウドの導入規模やアプリケーションの複雑さが増すにつれ、組織はインフラストラクチャーやサービスのセキュリティ確保という課題に直面しています。セキュリティ侵害は数か月間発見されないことが多く、攻撃者に広範囲にわたる侵害を許す時間を与えてしまいます。また、組織が侵害に気づいても、すぐにログの保持期間が過ぎてしまうため、攻撃の完全な履歴を構成するログにアクセスできなくなる可能性があります。こうなると、チームは攻撃元、攻撃経路、攻撃期間に関する重要な質問に答えることができません。また、組織がログにアクセスできる場合でも、大量のログデータからパターンを検出して、インシデントの抑制と修復に必要な洞察を得ることは困難です。
この記事では、Datadog Cloud SIEM Investigator を使用して、発生からどれだけ時間が経過していても攻撃の範囲と影響を把握できる履歴セキュリティ調査を実施する方法を紹介します。
今回ご紹介するポイントは以下の通りです。 - ログを視覚化して攻撃を調査する - 関連するセキュリティシグナルのパターンとコンテキストを見つける - Workflow Automation で攻撃を管理しリスクを軽減する
セキュリティログを視覚化して攻撃の範囲を把握する
Cloud SIEM Investigator は、セキュリティインシデントの全履歴を提供するログの視覚化を可能にします。Datadog は、ログの詳細な履歴を保管する費用対効果の高い手段を提供しています。お客様はこれらのログを視覚化して、たとえずっと前に始まったセキュリティ侵害であってもその経過と影響を確認することができるようになりました。例えば、組織がデータ漏洩を発見した場合、Cloud SIEM Investigator を使用して、長期間にわたるログを検査し、徐々に古いログを振り返って、侵害の最初の兆候を特定することができます。
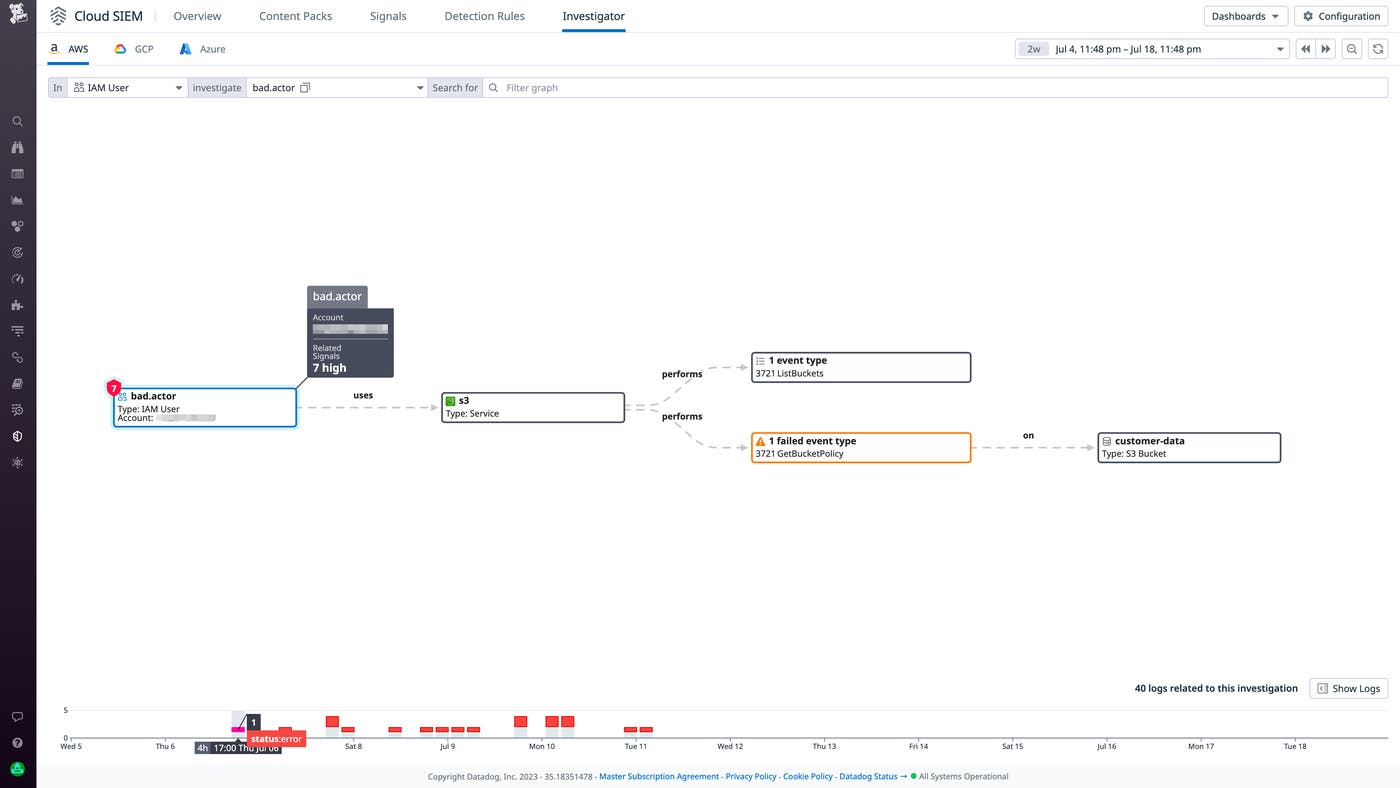
Cloud SIEM Investigator ビューにフィルターをかけることで、攻撃者の痕跡を明らかにするのに役立つ関連性のある記録を特定することができます。例えば、フィルターを使用して疑わしいユーザーやアカウントをハイライトしたり、攻撃者がどのサービスとやり取りしたかや、その結果 (攻撃者のサービスに対するリクエストが許可されたか拒否されたかなど) を確認したりできます。これにより、攻撃者の手口を理解することができます。あるユーザーが多数の Amazon EC2 インスタンスのメタデータを更新しようとしたが失敗した場合、そのユーザーは AWS 環境内に足場を築こうとしている悪意のある行為者であると疑うことができます。
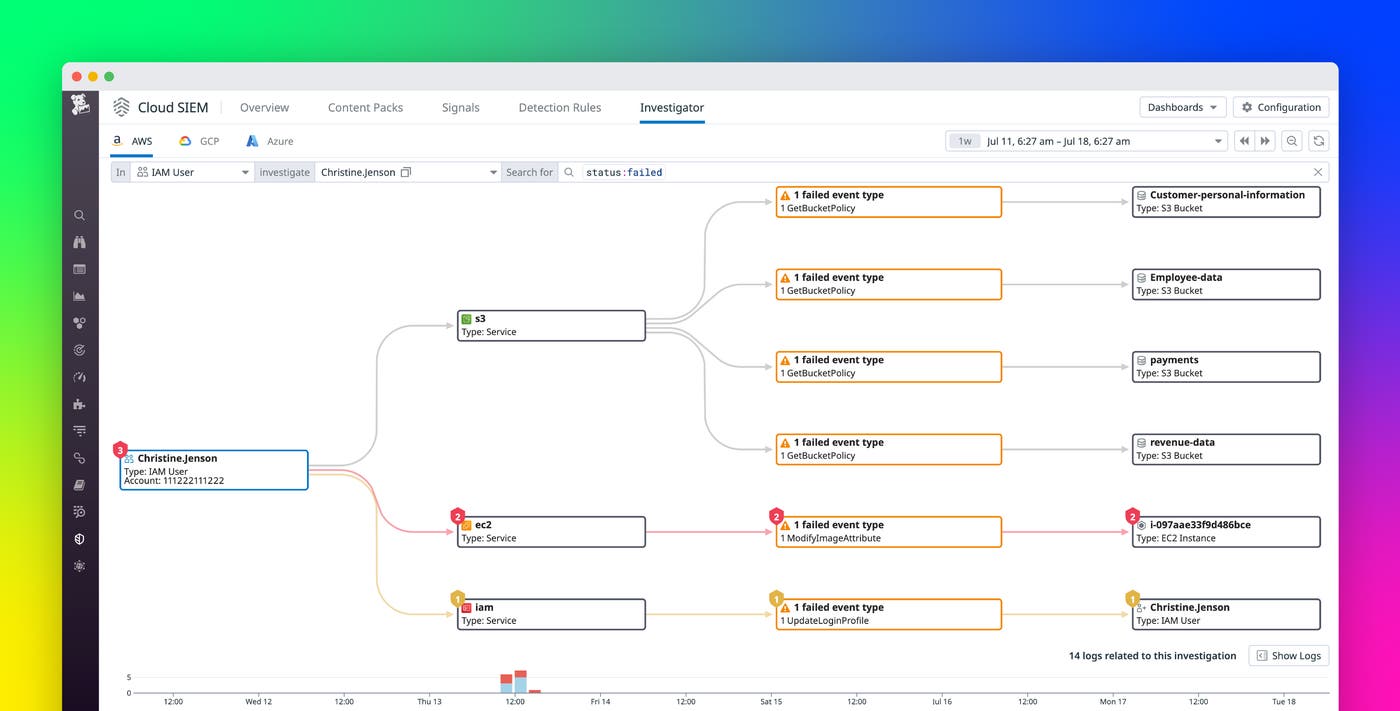
以下のスクリーンショットでは、Cloud SIEM Investigator が AWS CloudTrail のログを視覚化し、1 人の IAM ユーザーが Amazon S3 サービスにリクエストを行ったことを示しています。ページ下部のタイムラインは、このユーザーが数日間にわたってこのサービスとやり取りし、そのリクエストの大部分がエラーを発生させていることを示しています。ユーザーの S3 アクティビティを追跡すると、ユーザーは S3 バケットをリストアップし、そこから組織のインフラストラクチャーに関する知識を得ることができたことがわかります。また、ユーザーは customer-data バケットのバケットポリシーにアクセスしようとしたが失敗したことがわかります。これは、アクセス制御が緩いバケットを特定しようとした可能性があり、攻撃の始まりを示唆している可能性があります。
セキュリティシグナルを使用して調査のコンテキストを構築する
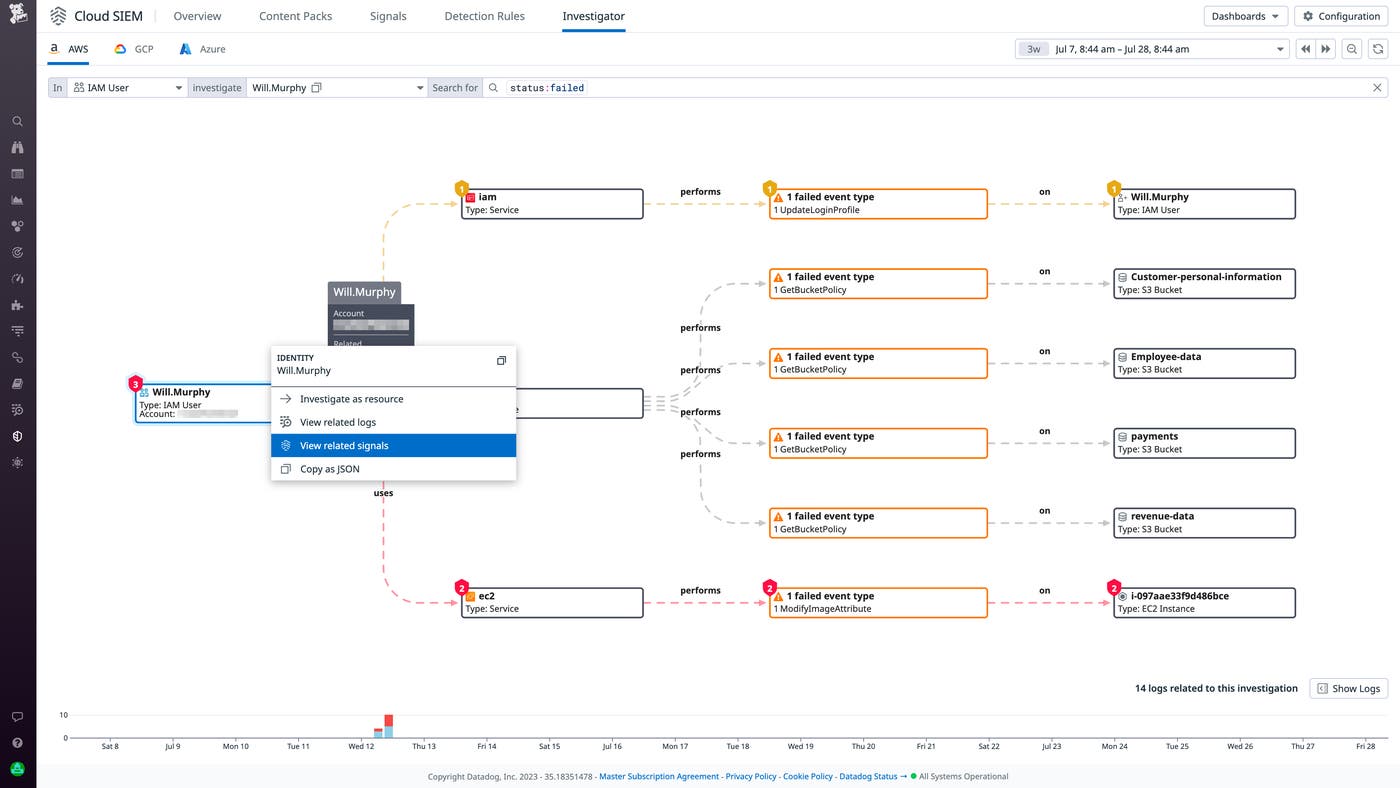
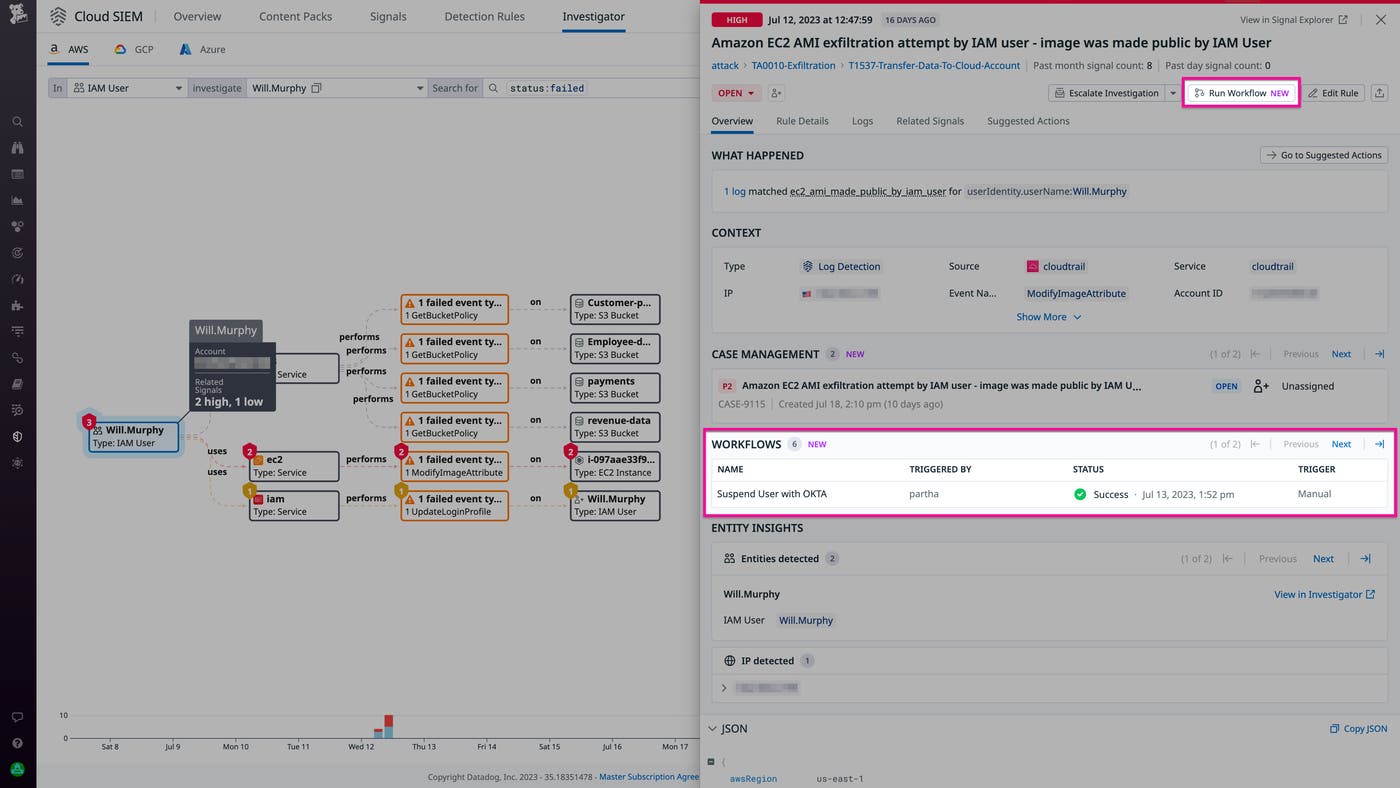
潜在的な攻撃のコンテキストを得るには、Cloud SIEM Investigator から簡単にピボットして、関与していると思われるアイデンティティ (アカウントやユーザーなど) やクラウドサービスに関連するセキュリティシグナルを確認することができます。Datadog Cloud SIEM は、セキュリティログを監視してリスクを検出し、検出ルールに違反した場合にセキュリティシグナルを生成します。これは、攻撃にさらされていることを示している可能性があります。以下のスクリーンショットは、Cloud SIEM Investigator から操作して、悪意のある行為者であると疑われる IAM ユーザーに関連するセキュリティシグナルを確認する方法を示しています。
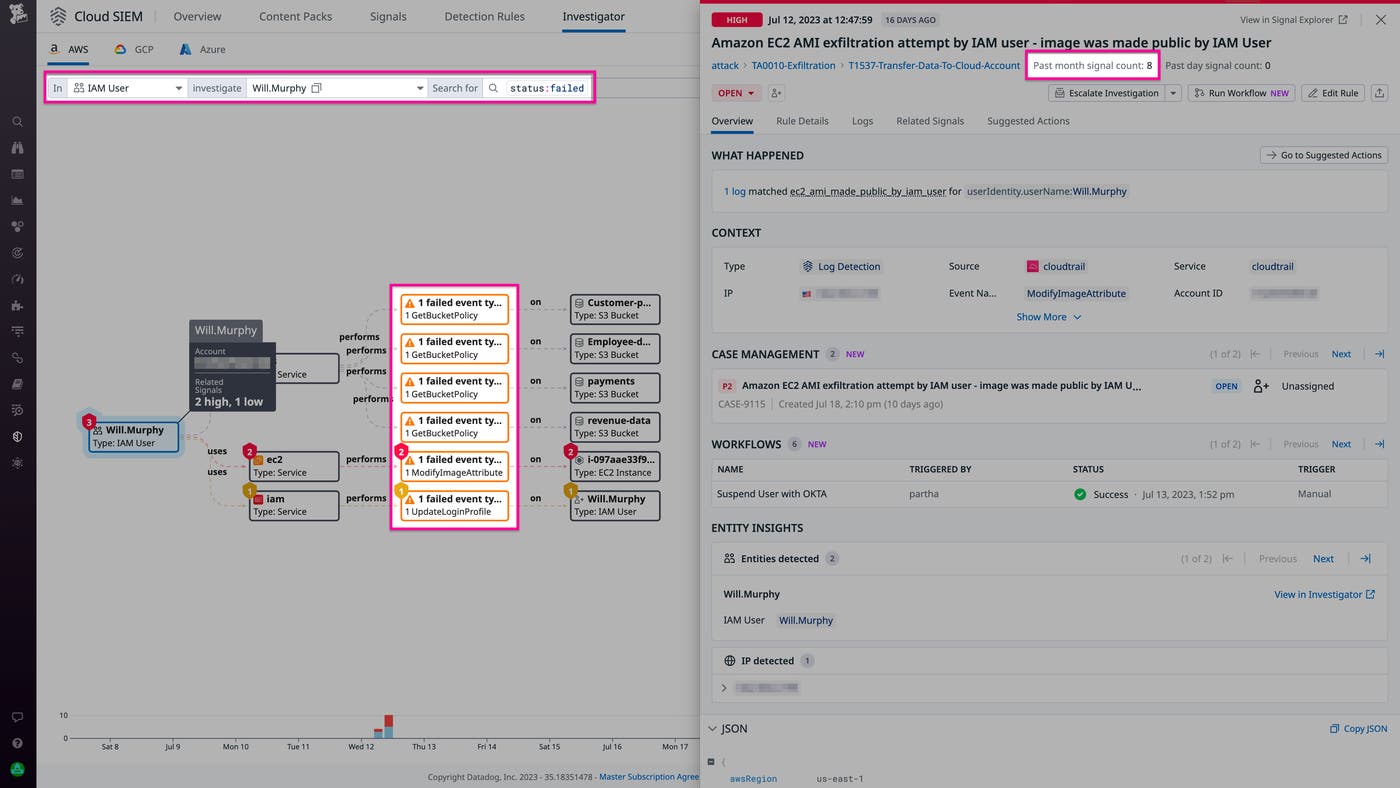
セキュリティシグナルデータを使用すれば、調査の焦点を絞って要する時間を短縮し、攻撃を受けているかどうかを迅速に確認できるほか、攻撃方法までもわかります。下のスクリーンショットでは、サイドパネルに不審な IAM ユーザーに起因するセキュリティシグナルが表示され、EC2 イメージを不正ユーザーが利用できるようにするためにそのユーザーが AMI を流出させようとしたことが示されています。このシグナルは過去 1 か月で 8 回発生しており、攻撃者が脆弱性を見つけて悪用しようと繰り返し行動していることを示しています。また、他のセキュリティシグナルを調査すれば、攻撃者の行動様式の全体像を把握することができます。例えば、攻撃の初期段階として権限昇格、侵害されたアクセスキー、ブルートフォースが使用されたことがわかるかもしれません。
Workflow Automation で攻撃を管理しリスクを軽減する
継続的な攻撃を検出した場合、侵害されたユーザーアカウントのロックやアクセスキーのローテーションなど、定義した修復ステップを適用するために迅速に対応する必要があります。Datadog Workflow Automation では、このようなアクションを自動化して、侵害に迅速に対応することができます。また、ブループリントを使用すれば簡単にワークフローを作成し、対応を簡素化、迅速化することができます。
例えば、以下に示すブループリントでは、ある Okta ユーザーアカウントを迅速に一時停止するワークフローを作成できます。ワークフローがトリガーされると、対応者に警告する Slack メッセージが送信され、このユーザーを一時停止する (または、問題を誤検出と判断してそれ以上のアクションを取らない) ことを確認するよう求めます。
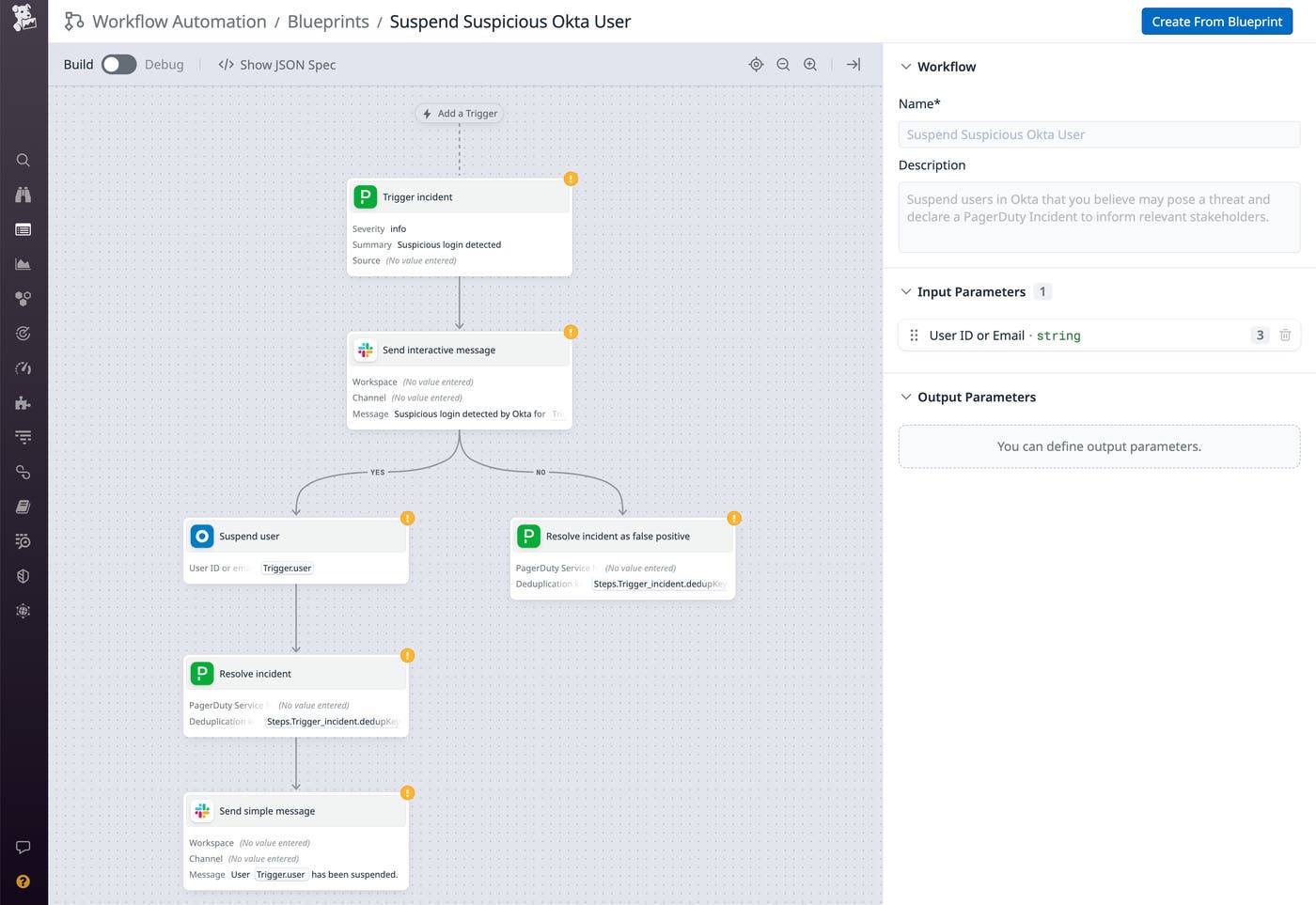
このようなワークフローは、セキュリティ調査によってユーザーに脅威があると判断された場合に、チームの対応を迅速化するのに役立ちます。自動化した対応の対象となる脅威をセキュリティシグナルが示す場合、直ちにそのワークフローをトリガーして攻撃を封じ込めることができます。具体的には、Cloud SIEM Investigator のサイドパネルで Run Workflow ボタンをクリックし、実行したいワークフローを選択するだけです。
Cloud SIEM Investigator で攻撃を把握・管理する
Cloud SIEM Investigator は、ログの詳細な履歴に基づいて過去にさかのぼってセキュリティ調査を実施できるようにすることで、ビジネスクリティカルなアプリケーションのセキュリティを確保するための強力なツールを提供します。また、Workflow Automation をすぐにトリガーして攻撃を修復し、将来的な露出を軽減することだってできます。Cloud SIEM Investigator は、AWS CloudTrail ログと Google Cloud 監査ログをサポートしています。AWS と GCP のログに脅威がないか監視するには Cloud SIEM ガイドを参照してください。Cloud SIEM Investigator の詳細についてはドキュメントをご覧ください。また、まだ Datadog をご利用でないお客様には、14 日間の無料トライアルをご用意しています。