Vera Chan

Lance Malacara

Yash Kumar
Security teams face a threat landscape shaped by AI-driven attacks and identity misuse. Adversaries increasingly rely on compromised identities to blend in as legitimate users, making attacks harder to detect and slower to contain. On average, organizations take 241 days to identify and contain a breach.1
While threats have evolved, legacy SIEMs have not kept pace. They struggle with the scale of modern data, lack sufficient context to prioritize risk, and require manual correlation across systems, which slows response.
At RSA 2026, we’re introducing new capabilities in Datadog Cloud SIEM to address these problems:
- Faster AI-powered investigations
- Enhanced threat intelligence, behavioral analytics, and risk insights
- Scalable security operations for enterprise environments
Lightning-fast investigations with AI-driven analysis
As attack volume and complexity increase, manual triage and reactive workflows are falling behind. When analysts must manually correlate fragmented signals, context is lost, dwell time increases, and real threats are missed.
Datadog Cloud SIEM now uses AI to automate this process, helping teams confidently move from triaging raw signals to reviewing validated conclusions.
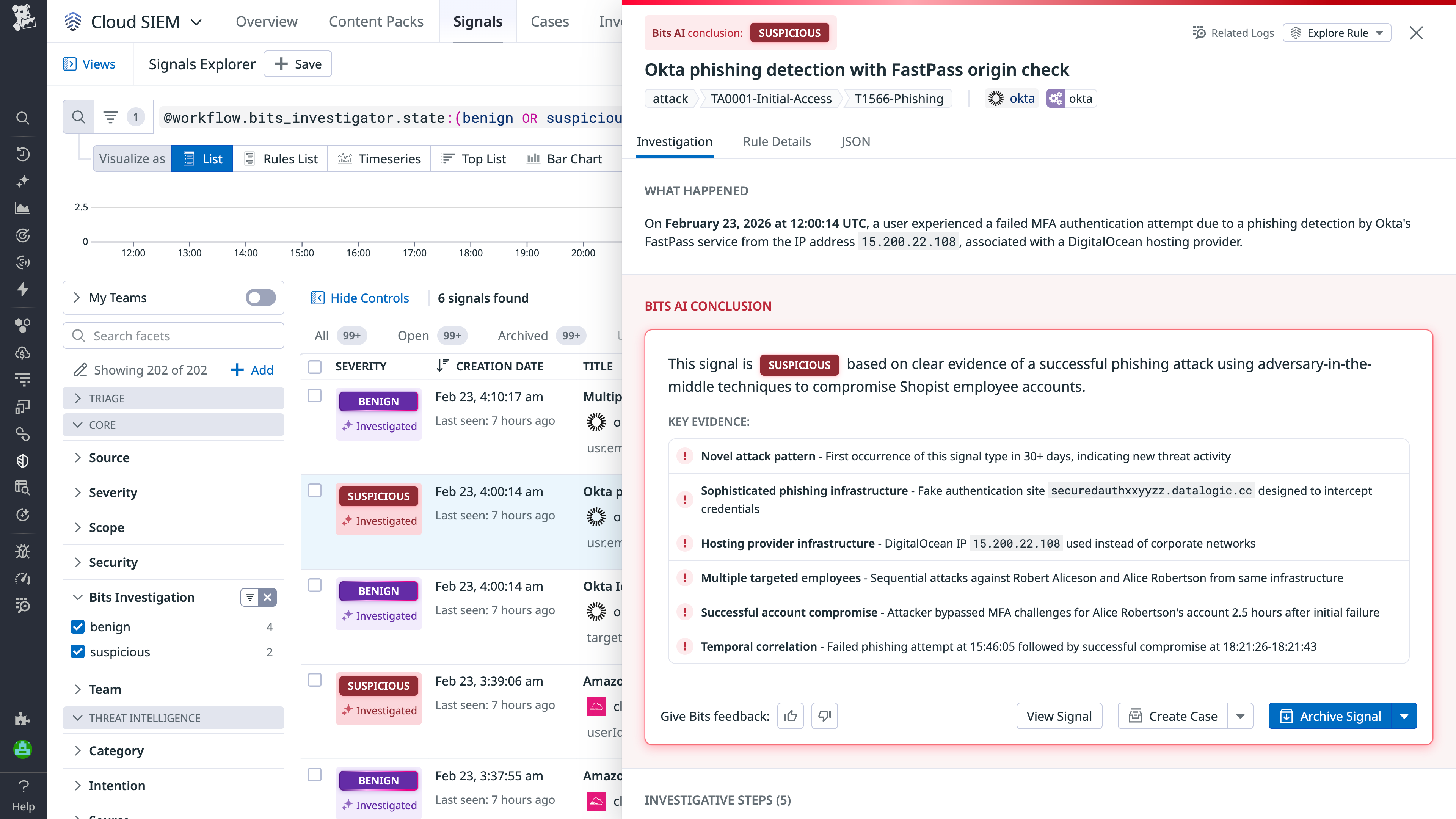
Autonomous investigations at machine speed with Bits AI Security Analyst
Bits AI autonomously investigates signals across cloud control planes, identity providers, endpoints, SaaS applications, and more to surface evidence-based verdicts. By automating correlation and analysis, Bits AI dramatically reduces investigation times by over 90%2, decreasing analyst workloads and helping teams prioritize high-risk threats.
Bits AI Security Analyst is now generally available in Datadog Cloud SIEM. Learn more in the product blog and keep up with our documentation as we support more data sources.
More actionable threat intelligence, behavioral analytics, and entity risk insights
Threat intelligence is most effective when it reflects your environment. Teams often need to manually piece together external indicators, identity signals, and activity logs across disconnected tools. This limits their ability to understand risk and appropriate next steps.
Datadog Cloud SIEM unifies signals through threat intelligence integrations, a comprehensive explorer for indicators of compromise (IoCs), and risk-based insights and notifications. Together these capabilities enable teams to correlate intelligence with real-time context and identify impacted users and assets more effectively.
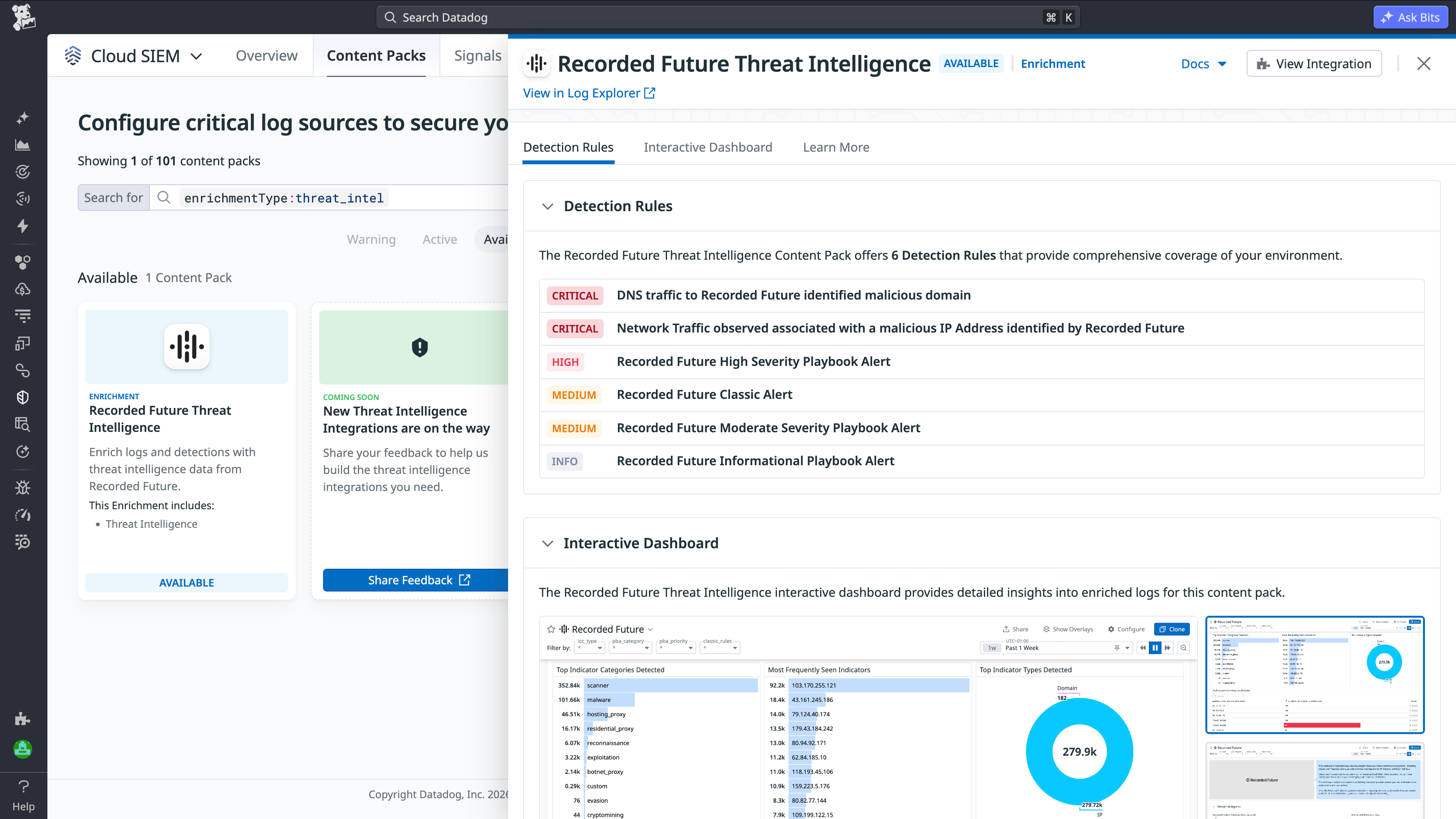
New threat intelligence integrations embedded into your security operations
Cloud SIEM integrates with providers like Recorded Future to bring high-fidelity threat intelligence directly into detections and investigations. These integrations enable you to centralize threat intelligence, reduce context switching, and improve response times. Support for additional integrations is coming soon.
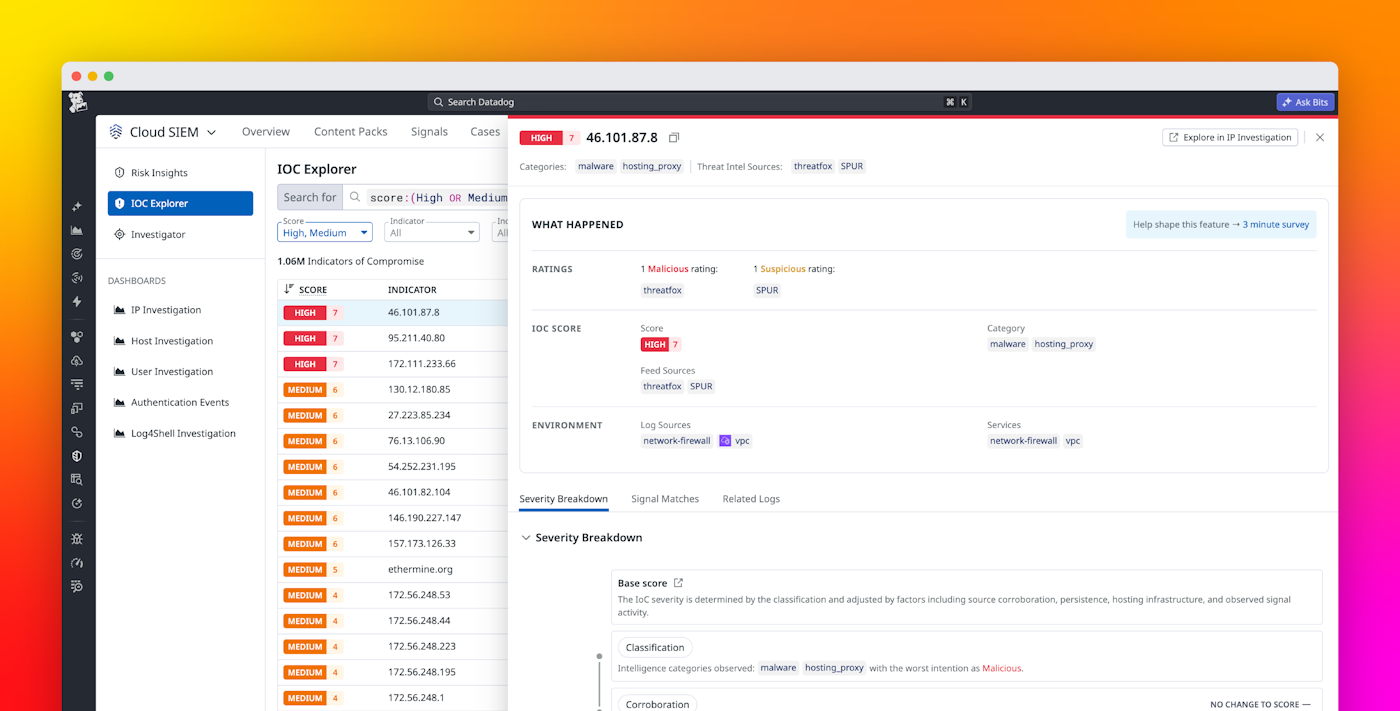
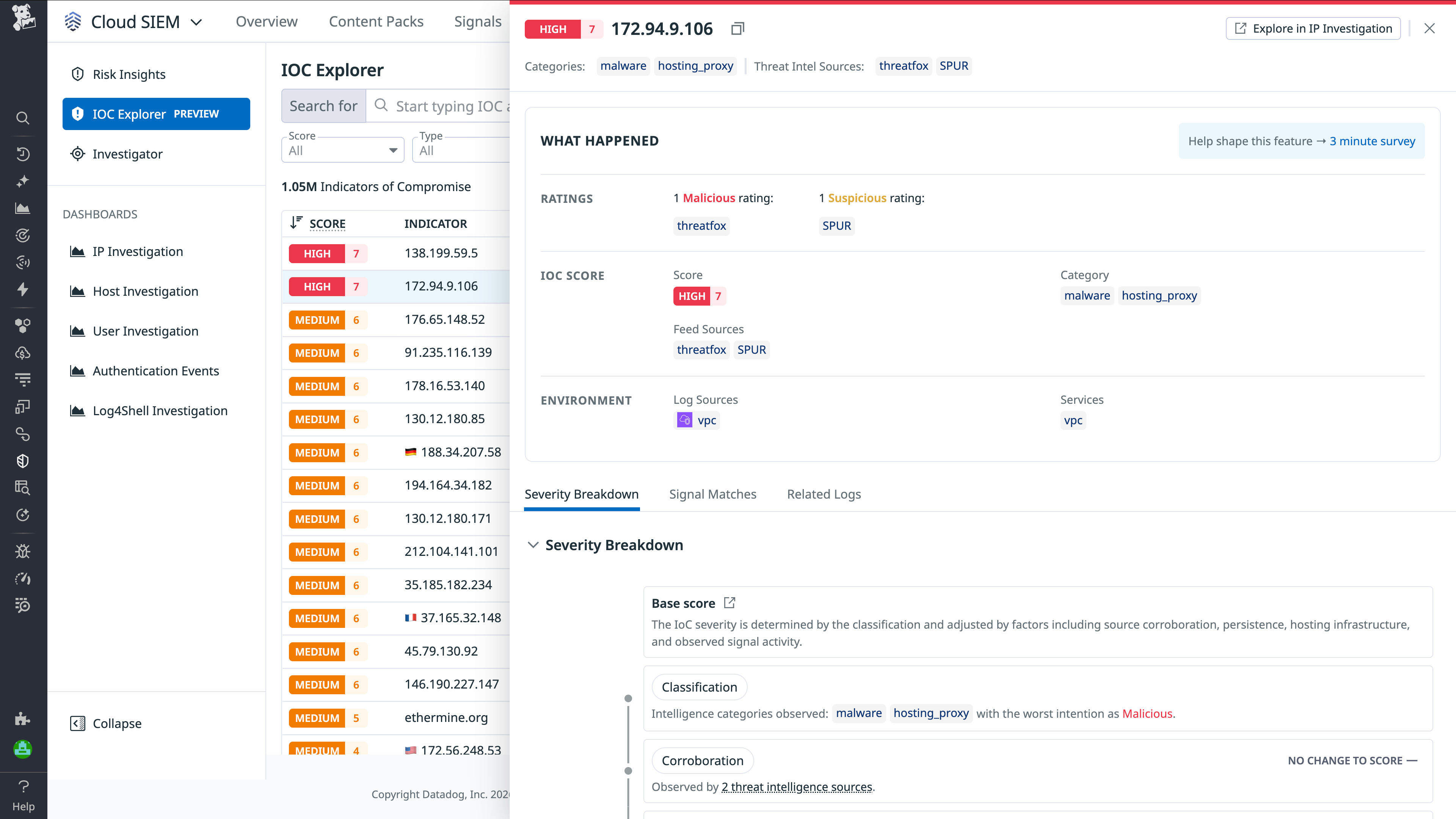
Turn Cloud SIEM into a threat intelligence hub with the IOC Explorer
Investigating IoCs often requires switching between multiple tools and data feeds. IOC Explorer centralizes threat intelligence sources and correlates them with your environment, enabling teams to assess impact, identify affected entities, and run threat hunts directly within Cloud SIEM.
Read our IOC Explorer documentation to learn more.
Detect signs of compromise before they escalate with User and Entity Behavioral Analytics (UEBA)
Attackers increasingly target identities such as user and service accounts, using credentials and access tokens to blend in and evade detection. UEBA in Datadog Cloud SIEM detects subtle signals of compromise by learning baseline behavior across your cloud users and entities. It surfaces anomalies that traditional detections may miss, helping teams identify insider and credential-based threats, reduce false positives, and respond more quickly.
Interested in early access? Sign up for the preview to help shape UEBA for Datadog.
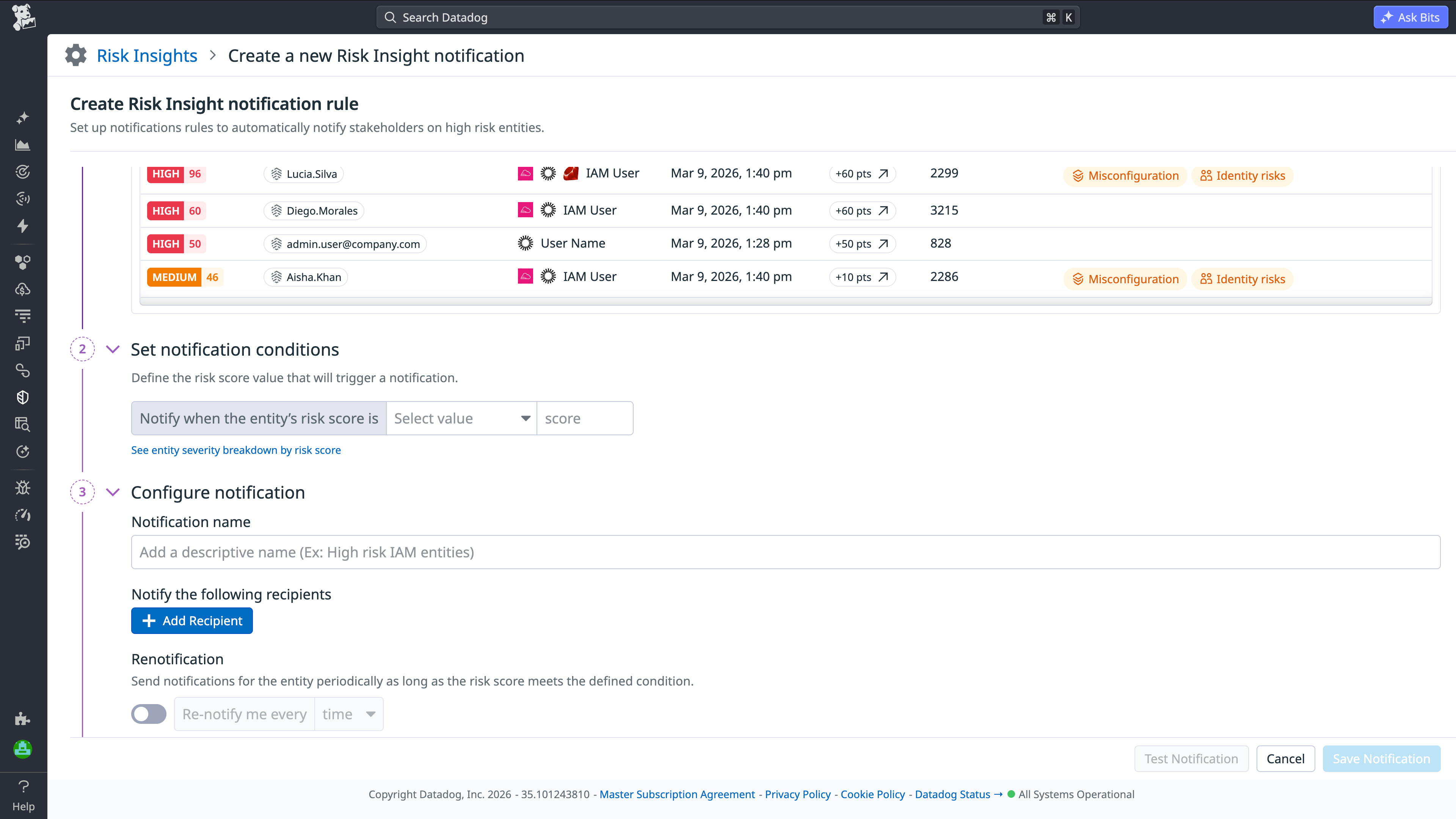
Turn entity risk into immediate action with Risk Insight Notifications
Prioritizing which entities to investigate requires security teams to constantly monitor risk scores across hundreds or thousands of users and assets. Risk Insight Notifications eliminates manual reviews by notifying teams when entities cross customizable risk thresholds.
For example, combined Okta phishing and MFA fatigue signals—each low priority on their own—can indicate a potential adversary-in-the-middle attack and increase a user’s risk score. Teams are notified in Slack, Microsoft Teams, email, or incident platforms, helping them prioritize and respond more quickly.
Check out our documentation to learn more about Risk Insight Notifications.
Scale security operations for the enterprise
As security programs mature, detection and response must operate like an engineering discipline that is governed, scalable, and measurable. Cloud SIEM now delivers a multi-engine detection platform with SQL-based rule creation and out-of-the-box OCSF datasets for maintaining detection hygiene. These capabilities help teams efficiently build and scale reliable detections.
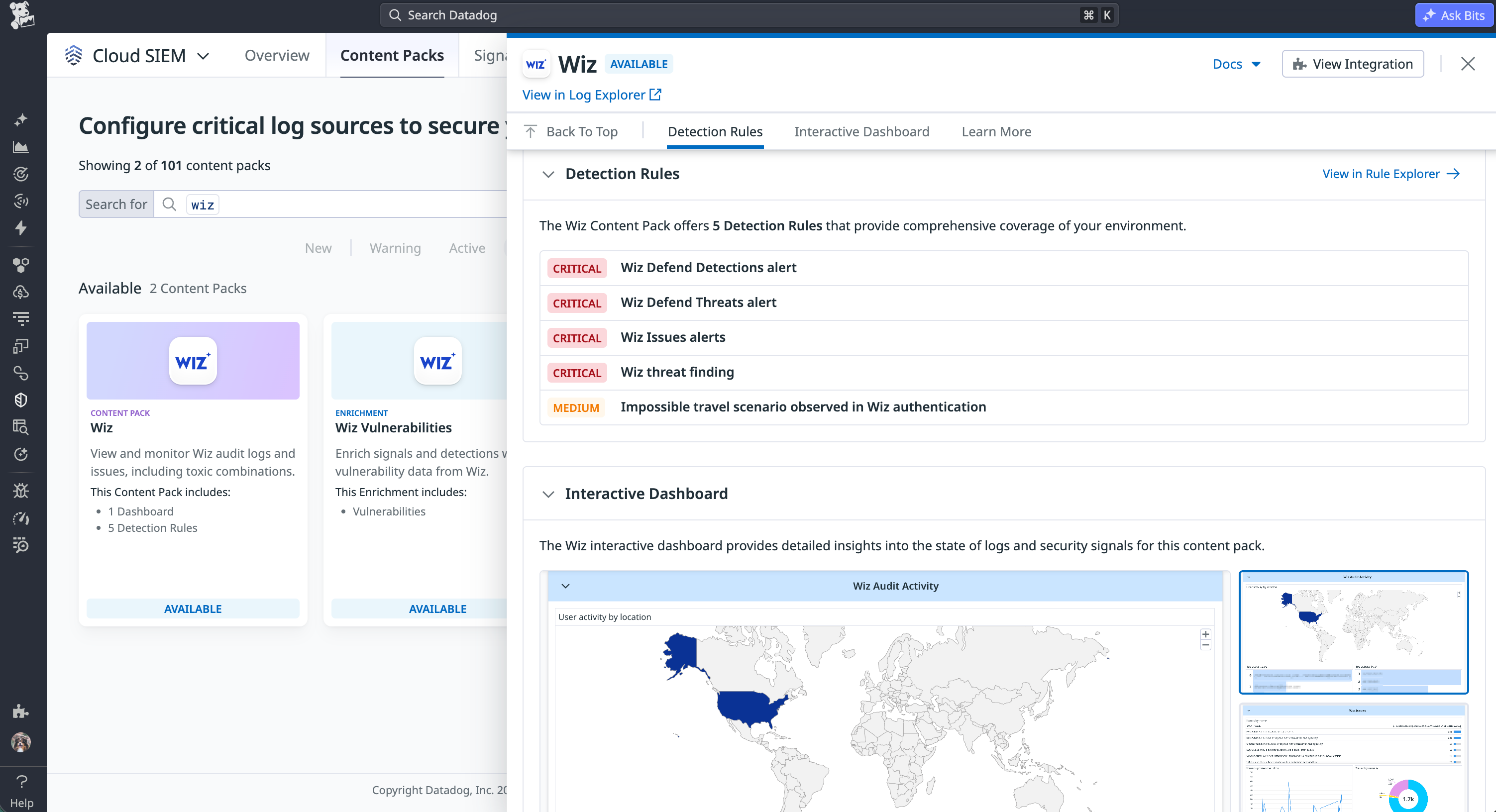
Accelerate time to value with pre-built detections and dashboards in the latest Content Packs
We’ve doubled the number of Content Packs, adding new detections, dashboards, and investigation workflows to improve deployment and standardize security coverage. These include integrations for Fortinet FortiGate, Next Gen Firewall, Wiz, and Zscaler Private Access.
The Wiz Content Pack includes detections for threat findings and authentication anomalies such as impossible travel, along with dashboards and workflows to help teams investigate alerts quickly.
Get started in-app or view our latest Content Packs.
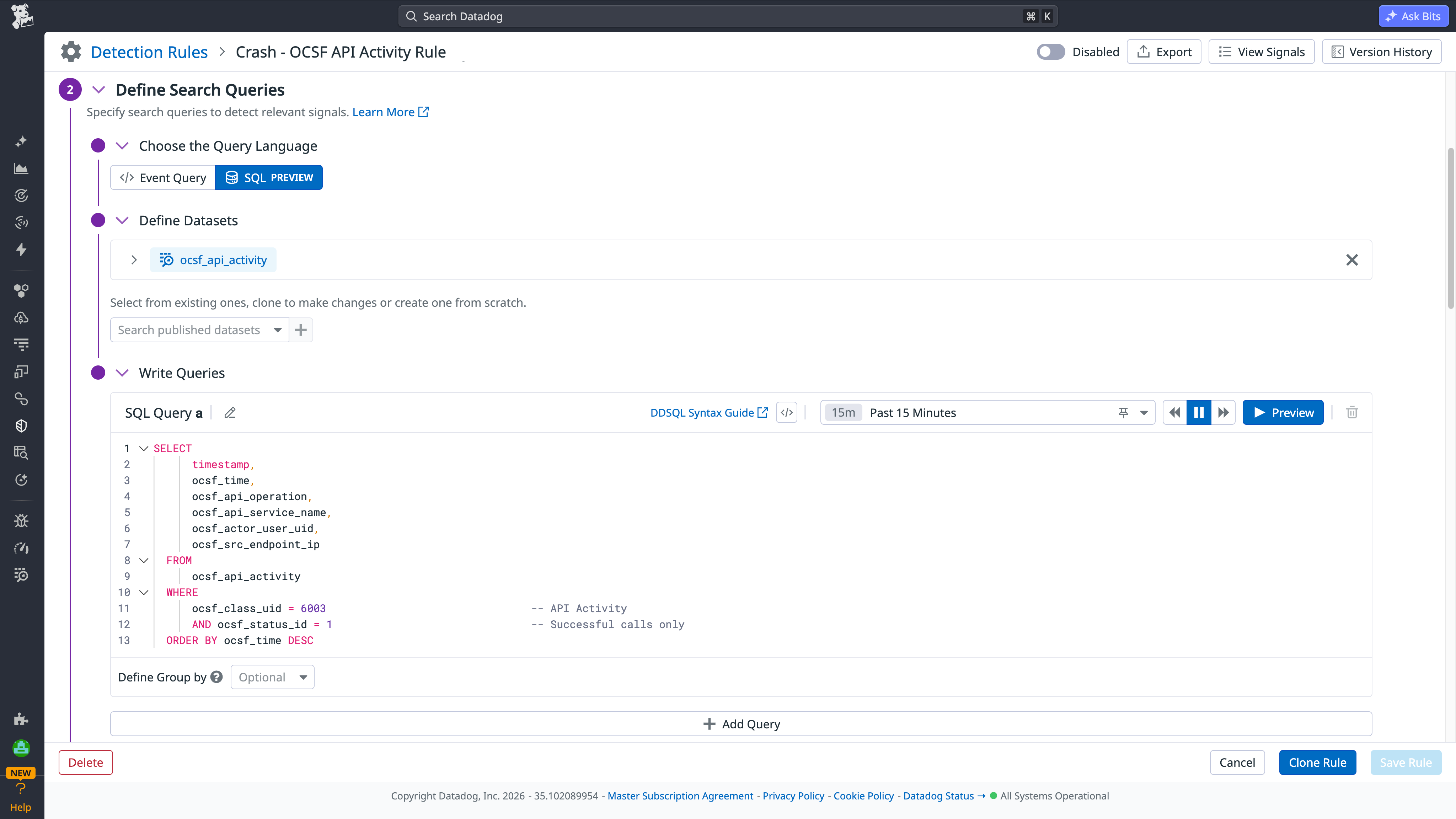
Build, migrate, and scale detections with SQL-based detections and OCSF
Enterprise SOC teams often struggle to migrate, scale, and govern detection programs as legacy SIEMs accumulate complex rulesets. Datadog Cloud SIEM enables SQL-based detections on normalized OCSF datasets, simplifying migration, rule creation, and governance.
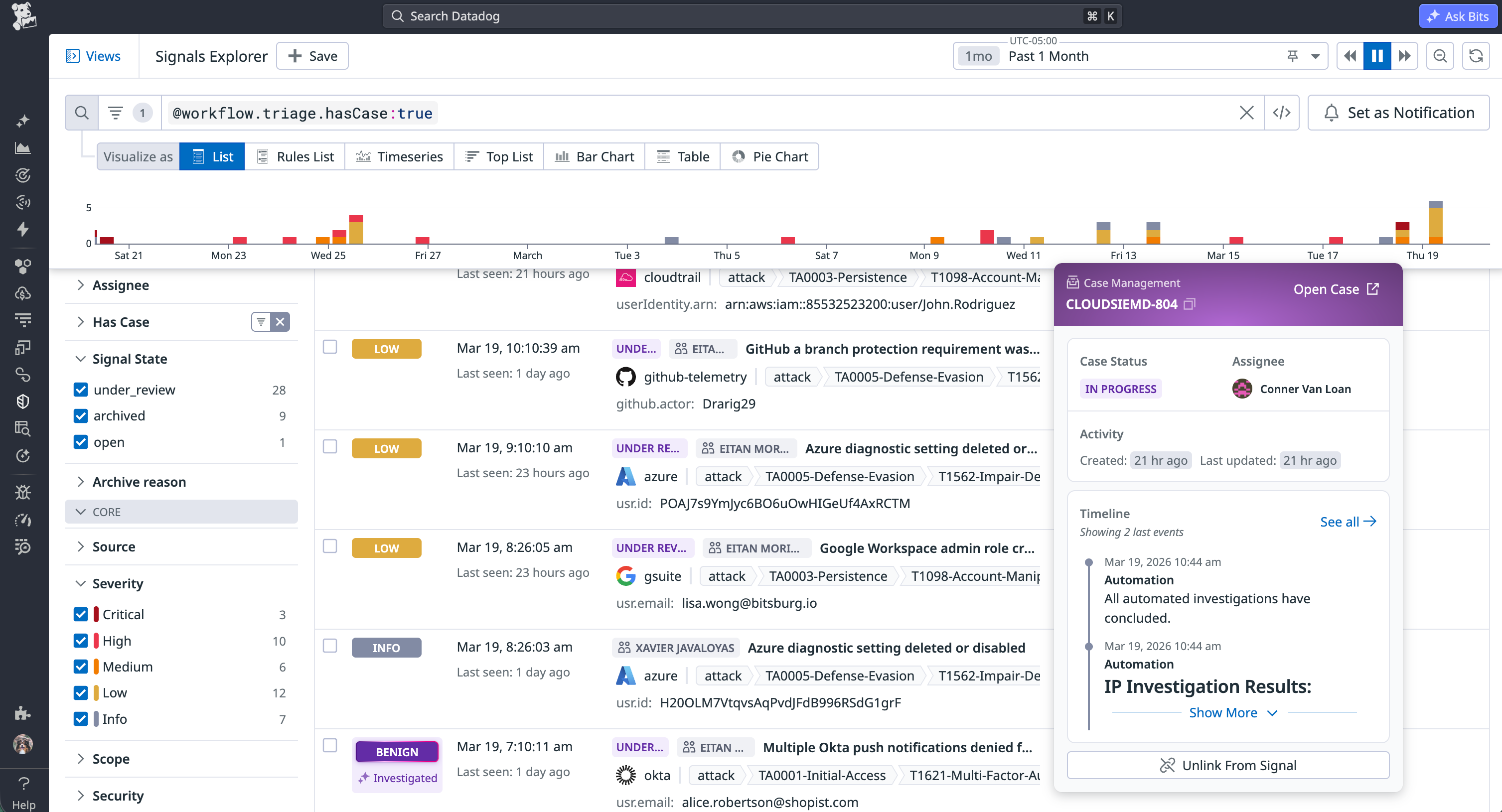
Streamline security investigations with integrated Security Case Management in Cloud SIEM
Security investigations often stall as analysts switch between signals and separate case management tools. Cloud SIEM’s integrated Security Case Management links signals directly to structured cases, bringing triage and investigation into a single workflow.
Analysts can assign ownership, track evidence, and collaborate through integrations such as Jira, keeping activity in sync and improving response times.
Learn more about Security Case Management in our documentation.
Modernize security operations for speed, actionable insights, and scale
As security operations evolve, the tools that support them must keep pace. Datadog Cloud SIEM brings together AI-driven investigations, identity-aware threat intelligence, and enterprise-scale detection and case management to help teams prioritize risk, automate investigations, and respond with confidence.
See our Cloud SIEM documentation for more information and to get started. If you’re new to Datadog, sign up for a free 14-day trial.

Footnotes
-
Coker, James. “Data Breach Costs Fall for First Time in Five Years.” Infosecurity Magazine, 30 July 2025 ↩
-
Results from internal data and research from the Bits AI Security Analyst early access program. ↩