- Product
Infrastructure
Applications
Data
Logs
Security
- Code Security
- Software Composition Analysis
- Static Code Analysis (SAST)
- Runtime Code Analysis (IAST)
- IaC Security
- Cloud Security
- Cloud Security Posture Management
- Cloud Infrastructure Entitlement Management
- Vulnerability Management
- Compliance
- Cloud SIEM
- Workload Protection
- App and API Protection
- Sensitive Data Scanner
- Security Labs Research
- Open Source Projects
- Secret Scanning
Digital Experience
Software Delivery
Service Management
AI
Platform Capabilities
- Bits AI Agents
- Metrics
- Watchdog
- Alerts
- Dashboards
- Notebooks
- Mobile App
- Fleet Automation
- Governance Console
- Access Control
- Incident Response
- Case Management
- Event Management
- Workflow Automation
- App Builder
- Cloudcraft
- CoScreen
- Teams
- OpenTelemetry
- Integrations
- IDE Plugins
- MCP Server
- Pup CLI
- Agent Directory
- API
- Marketplace
- DORA Metrics
- Customers
- Pricing
- Solutions
- Financial Services
- Manufacturing & Logistics
- Healthcare/Life Sciences
- Retail/E-Commerce
- Government
- Education
- Media & Entertainment
- Technology
- Gaming
- Amazon Web Services Monitoring
- Azure Monitoring
- Google Cloud Monitoring
- Oracle Cloud Monitoring
- Kubernetes Monitoring
- Red Hat OpenShift
- Pivotal Platform
- OpenAI
- SAP Monitoring
- OpenTelemetry
- Application Security
- Cloud Migration
- Monitoring Consolidation
- Unified Commerce Monitoring
- SOAR
- DevOps
- FinOps
- Shift-Left Testing
- Digital Experience Monitoring
- Security Analytics
- Compliance for CIS Benchmarks
- Hybrid Cloud Monitoring
- Edge Device Monitoring
- Real-Time BI
- On-Premises Monitoring
- Log Analysis & Correlation
- CNAPP
Industry
Technology
Use Case
- About
- Blog
- Docs
- Login
- Get Started
Enhance system security using industry-standard best practices
Maintaining regulatory compliance is necessary for organizations that do not want to leave their systems vulnerable to attacks or face costly audit penalties. CIS benchmarks, published by the Center for Internet Security (CIS), help organizations assess the current state of their environment's security configurations in order to reduce system vulnerabilities. Since the AWS CIS benchmarks cover a sizable list of AWS resources such as EC2, RDS and S3 buckets, organizations need the ability to identify and mitigate any compliance issues as quickly as possible.
Datadog Cloud Security Posture Management (CSPM) is an offering within the Datadog cloud security platform, which protects an organization's production environment with a full-stack offering providing threat detection, posture management, workload security, and application security. CSPM enables organizations to benchmark systems against CIS standards, so they can get a better understanding of their security posture. With Datadog's out-of-the-box compliance dashboards, teams can easily review violations at a glance, then notify the appropriate members using one of Datadog's collaboration integrations to resolve the issue.
Automatically detect system vulnerabilities
Organizations need to be proactive in catching system misconfigurations, or they risk compromising valuable and confidential customer data. Datadog's built-in cloud configuration rules require no extra setup and enable teams to routinely monitor all of their AWS resources. These rules are automatically mapped to the AWS CIS benchmarks, so organizations can actively monitor their systems against the most up-to-date benchmarks and surface vulnerabilities immediately.
Increase compliance visibility at cloud scale
Building and maintaining a secure environment requires thorough configuration management for every system resource—from AWS user policies to network traffic on individual nodes. Datadog scans every resource in real time, so organizations can identify and fill critical security gaps before they become more serious. If Datadog detects a potential compliance issue, teams are automatically alerted with clear steps to resolve the problem.
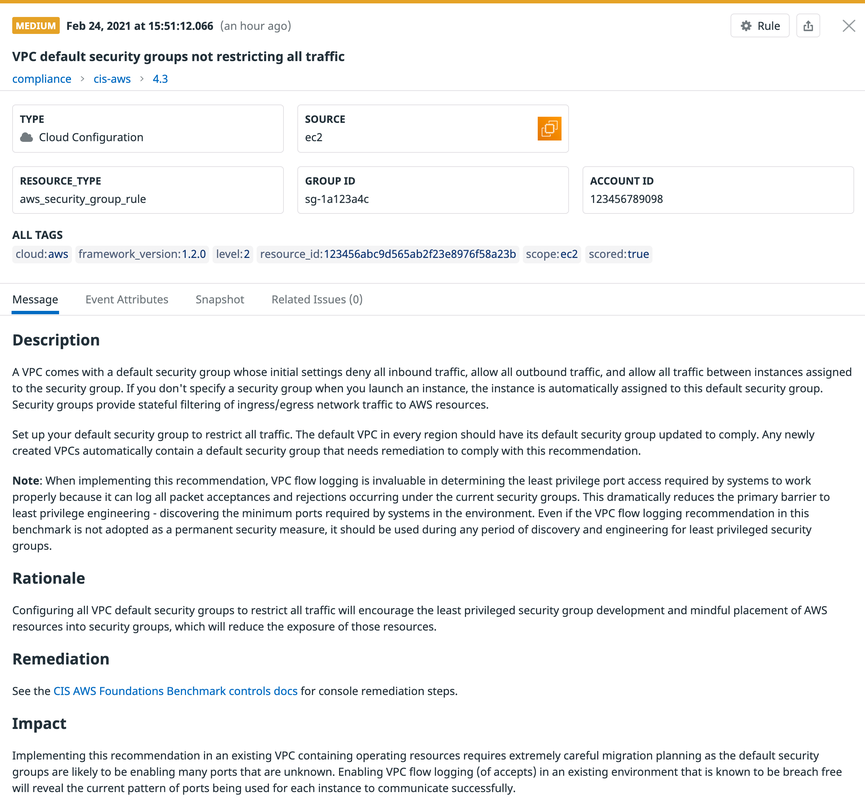
In the example above, Datadog CSPM identified a misconfigured AWS security group that was set to not block all traffic to the associated VPC, which can result in an attacker accessing and exposing sensitive data. You can mitigate this issue by updating the VPC security group to restrict all traffic.
Seamless integration for faster, easier audits
As part of the Datadog cloud security platform, CSPM seamlessly integrates with an organization's cloud environment and resources, so teams can gather the information needed to conduct thorough compliance audits without the need for third-party assessments or special training. For example, Datadog's compliance dashboards give teams a shareable report card of compliance findings across their cloud and local environments, so they can review the state of any resource at a glance. You can also build team dashboards that incorporate security, compliance, and infrastructure data from all of your AWS resources, allowing you to quickly see an issue’s overall impact. Dashboards are shareable, so you can collaborate with other engineering and GRC teams to resolve a compliance violation.
CSPM also integrates with the AWS Well-Architected (WAR) Tool by automatically mapping built-in AWS compliance rules to recommendations provided by the WAR Tool. This gives teams the ability to quickly identify and address misconfigurations found during the Well-Architected review process and improve their overall compliance posture. With the ability to collect, analyze, and retrieve relevant data in one place, organizations can significantly cut the time it takes to conduct third-party audits.



