Twingate is a network access platform that enables customers to deploy a zero trust authentication layer with their infrastructure as code (IAC) provider of choice. Using this model, you can program strict access control rules that can be updated and co-deployed alongside changes to your infrastructure. Each time a user establishes or closes a connection to a resource, Twingate documents the event with details such as the port, the volume of data transferred, and user identification.
By signing up for a Twingate subscription in the Datadog Marketplace and installing our integration, you can begin sending your Twingate events as logs to Datadog, where you can monitor them with an out-of-the-box dashboard. In this post, we’ll cover how to visualize key network events using the Twingate dashboard and configure automatic alerts on suspicious access activity.
Visualize network events using the Twingate dashboard
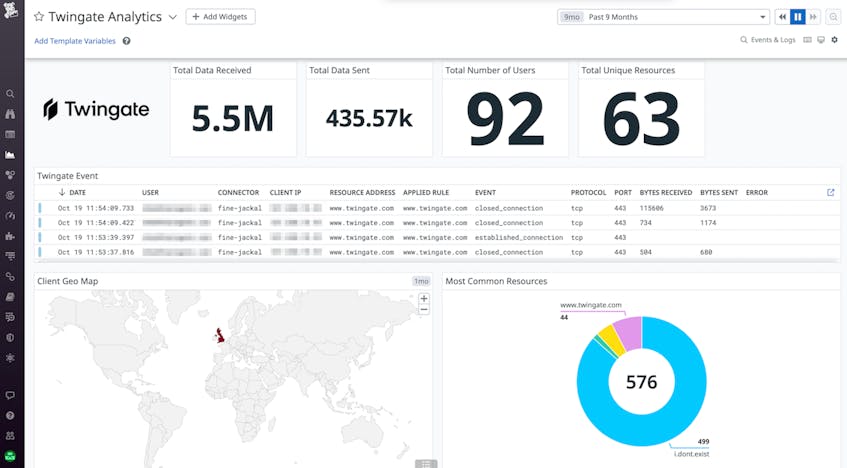
After installing the Twingate integration, Datadog will populate an out-of-the-box dashboard with a high-level overview of your network activity. This dashboard visualizes recent Twingate events, resources commonly accessed by clients, the total volume of data traveling across your network, and more. You can use the dashboard to help you monitor key security audit events, such as failed connections and large data transfers, in near-real time.
Datadog automatically tags clients accessing your network by geolocation as well—using the dashboard’s Client Geo Map, you can easily identify suspicious clients accessing your network from high-risk countries or those under imposed sanctions. Once a suspicious client has been identified, you can pivot to Datadog Cloud SIEM, where you can review related security signals and track an entity’s activity across cloud platforms such as AWS and GCP.
Set automatic alerts on suspicious access activity
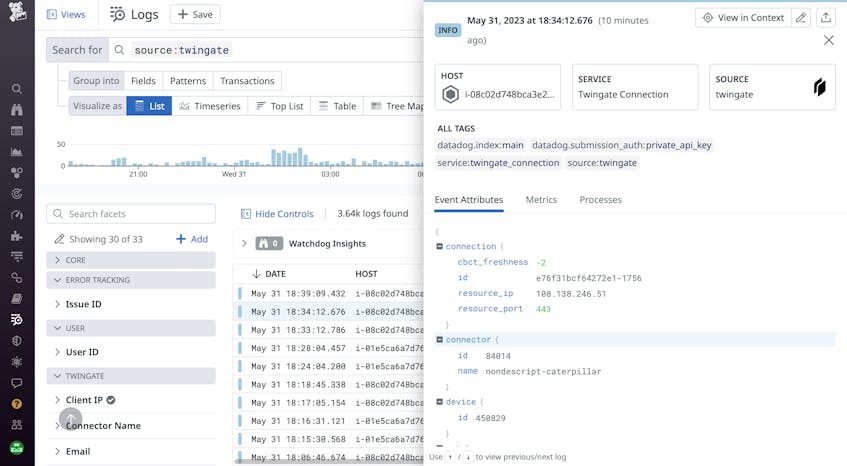
After you configure the Datadog Agent for log collection, you’ll be able to view your Twingate events as logs in Datadog Log Management.
By inspecting a Twingate log, you can gain insights into the user or device requesting access, as well as the resource they are attempting to access. Using the event fields available in the log’s JSON metadata, you can easily create queries in Datadog Log Management to investigate that user’s or device’s digital access trail across your resources.
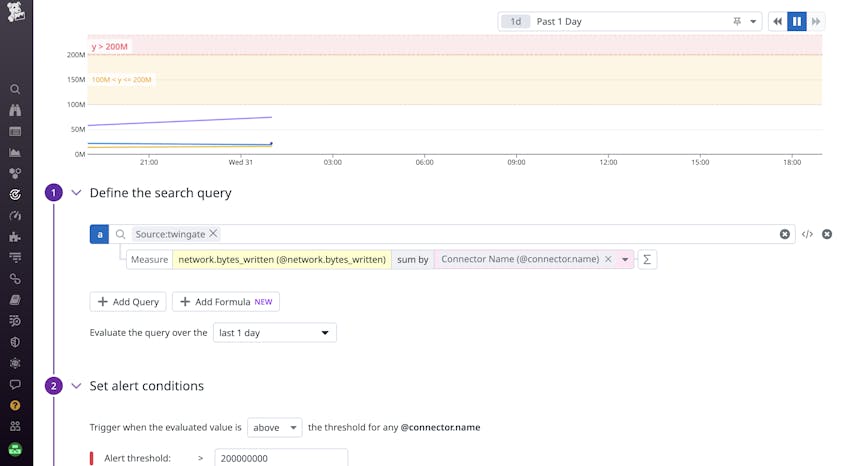
You can also configure log-based monitors in Datadog that can automatically alert you to suspicious activity, such as spikes in the volume of data transfers, access attempts from public IP addresses, and more. In the example below, we’ve configured a monitor that will trigger both warnings and alerts when network traffic from any connector crosses our set threshold.
Once an alert is triggered, you can declare an incident directly from the monitor to coordinate an immediate response within Datadog Incident Management. For example, if your monitor notifies you of an unauthorized access attempt to a protected resource, you can assign DevOps responders to investigate Twingate logs within Datadog to identify compromised accounts. Meanwhile, security engineers and administrators can pivot directly to and take immediate action in Twingate by locking the resource and removing access from suspected users.
Get started with Twingate and Datadog today
The Datadog Twingate integration enables you to monitor your network’s access activity alongside the rest of your environment in one unified platform. You can get started by purchasing a subscription to Twingate in the Datadog Marketplace, where you can explore all the partner tools available to begin monitoring your infrastructure. If you don’t already have a Datadog account, you can sign up for a free 14-day trial today.
The ability to promote branded marketing tools is a membership benefit offered through the Datadog Partner Network. If you’re interested in developing an integration or application that you’d like to promote, you can contact us at marketplace@datadog.com.