Creating security policies for the devices connected to your network is critical to ensuring that company data is safe. This is especially true as companies adopt a bring-your-own-device model and allow more personal phones, tablets, and laptops to connect to internal services. These devices, or endpoints, introduce unique vulnerabilities that can expose sensitive data if they are not monitored. For example, a user could unknowingly install malicious software on their personal phone and open up your network to a security breach once they connect to it. Or, you may need to create a policy that removes device access to internal services once an employee leaves your organization.
Carbon Black offers endpoint security software for your organization so you can easily monitor the safety of your network and connected devices and ensure security policies are applied across every device. And with Datadog’s integration with Carbon Black, you can now seamlessly monitor endpoints and triage potential threats to your network alongside other infrastructure data.
We’ll show you how Datadog’s integration can help you identify:
- endpoint activity in real time
- malicious software running on an endpoint
- compromised devices
Datadog + Carbon Black
Datadog’s Carbon Black integration collects CB Defense audit logs with Carbon Black’s syslog connector, enabling you to monitor data such as login attempts, compromised devices, and malicious software running on an endpoint. You can use this data to create your own dashboards, threat detection rules, and custom metrics to get better visibility into the devices that are accessing your network. With Datadog’s Logging without Limits™, you have control over what CB Defense logs you want to index—while still analyzing and archiving everything. And you can easily rehydrate logs if, for example, you need to perform a security audit.
Monitor endpoint activity in real time
Carbon Black audit logs capture information about activity across your network, including common threats outlined by the MITRE ATT&CK framework. Some of these include techniques for unauthorized access to your network, privilege escalation, and exfiltration. With Datadog, you can easily monitor endpoint activity to pinpoint trends in Carbon Black logs for your organization. This enables you to visualize the most common threats to your systems in real time.
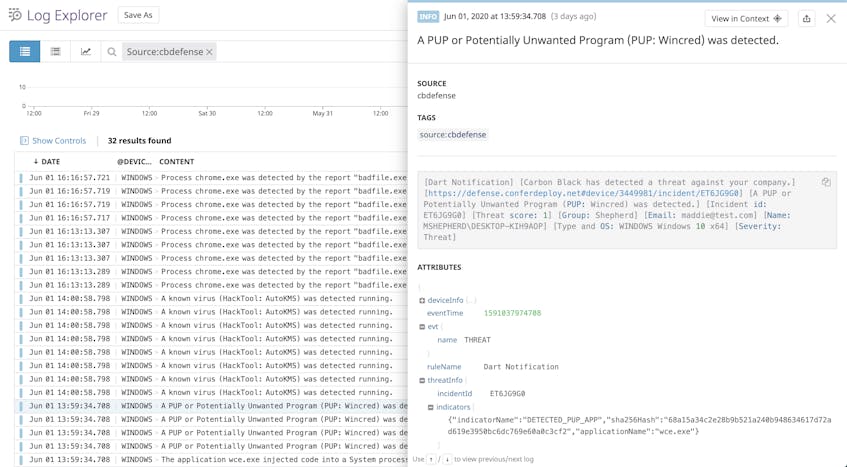
In the example log above, Carbon Black detected a potentially unwanted program running on devices in a network. Carbon Black logs include detailed information such as the name of the unwanted program and the name and IP address of the affected device, so you can quickly identify the machines that need to be isolated and repaired.
Focus on what’s important for protecting your network
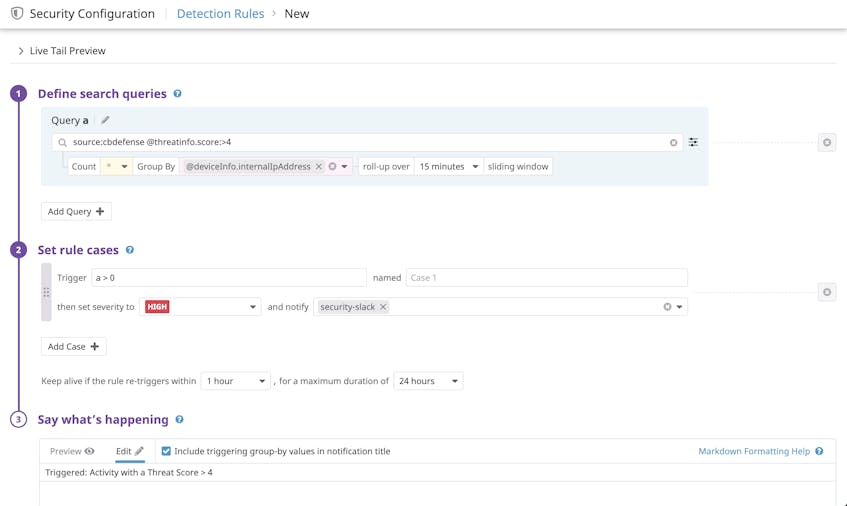
Carbon Black automatically applies a score to detected threats based on their severity, enabling you to focus on the most critical threats to your systems. With Datadog, you can create detection rules to alert you to threats based on their scores so that you can respond accordingly.
For example, you can create a detection rule that generates a signal when Carbon Black logs activity on an endpoint that is a threat level of four or greater. This could include malware or virus installations that are making unusual network connections or invoking unauthorized applications.
The example rule above creates signals grouped by the endpoint’s internal IP address. If this rule is triggered, Datadog automatically ties the IP address of the relevant device—along with the complete log sample—to the security signal. Datadog retains these log samples for 15 months at full granularity. This provides full context for the activity that generated the signal and enables you to quickly pinpoint the most vulnerable devices on your network.
Monitor and isolate compromised devices
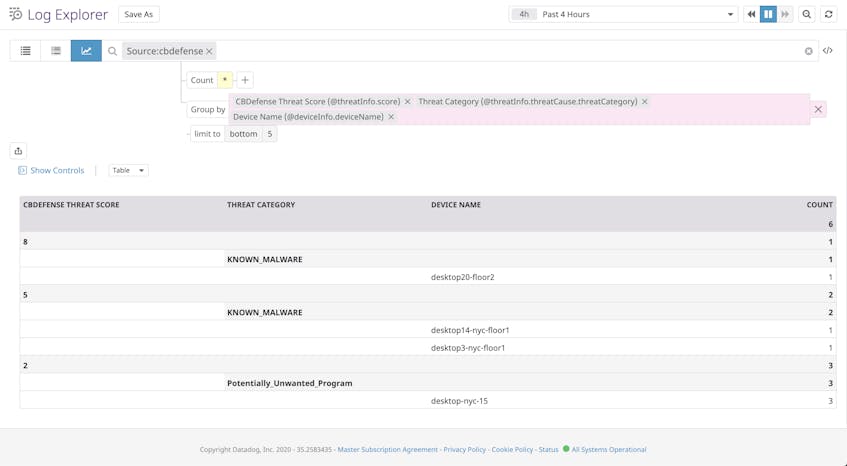
In addition to automatically notifying you of potential threats to your network with security signals, Datadog can help you get a better picture of which endpoints are compromised or vulnerable. For example, spearphishing is a common technique for installing malware on a machine in order to gain access. If a user who unknowingly has malware on a device connects to your network, you may be at risk of a data breach if you don’t quickly identify the device. You can create a table to review compromised devices and the level of severity for each associated threat, so you can prioritize repairing the most vulnerable systems.
You can click on a table cell in the “Device Name” column to view related logs for the device and get more details about the associated threat. Then you can quickly isolate the device by revoking its access to your network, giving you time to remove malware and push any necessary software or virus definition updates.
Start monitoring your defense logs with Datadog
Our Carbon Black integration works seamlessly with Datadog Cloud SIEM. And, with more than 700 other integrations, Datadog provides a rich centralized platform for overall vulnerability detection and infrastructure monitoring. Check out our documentation to start collecting Carbon Black audit logs or sign up for a free Datadog trial today.