Attackers (i.e., threat actors) often reuse techniques or resources, such as IP addresses, hashes, and domains, in multiple attempts to find and exploit vulnerabilities in your systems. Defenders can categorize this data as indicators of compromise (IOCs) and create collections of IOCs in order to look out for potential attacks. These IOC collections are known as threat intelligence. Developing, maintaining, and operationalizing threat intelligence is often challenging as it requires sifting through large volumes of data to surface legitimate instances of malicious activity. However, if done correctly, threat intelligence can be the key to identifying suspicious activity before it transforms into a more serious attack.
To help you simplify this process, Datadog Cloud SIEM now offers turn-key threat intelligence feeds curated by specialized threat intelligence partners. These feeds are constantly updated to include data about known suspicious activity (e.g., IOCs), so you can quickly identify which potential threats to your environment you should address. In this post, we’ll show you how Datadog:
- enriches all ingested logs with expert-curated threat intelligence in real time
- detects activity from known threat actors
- accelerates investigations and reduces noise by automatically surfacing relevant context within security alerts
Expert threat intelligence, managed by Datadog
Datadog works with expert partners, including IPinfo and GreyNoise, who specialize in curating and maintaining highly accurate and relevant threat intelligence by constantly researching both malicious and benign activity. Additionally, our partners categorize and label their threat intelligence so that you know whether an IP address was associated with an attack, a scanner, or an anonymizing service. To ensure that you have access to the highest quality intelligence, we regularly refresh these feeds, removing stale data and adding any new indicators that have been identified by our expert partners.
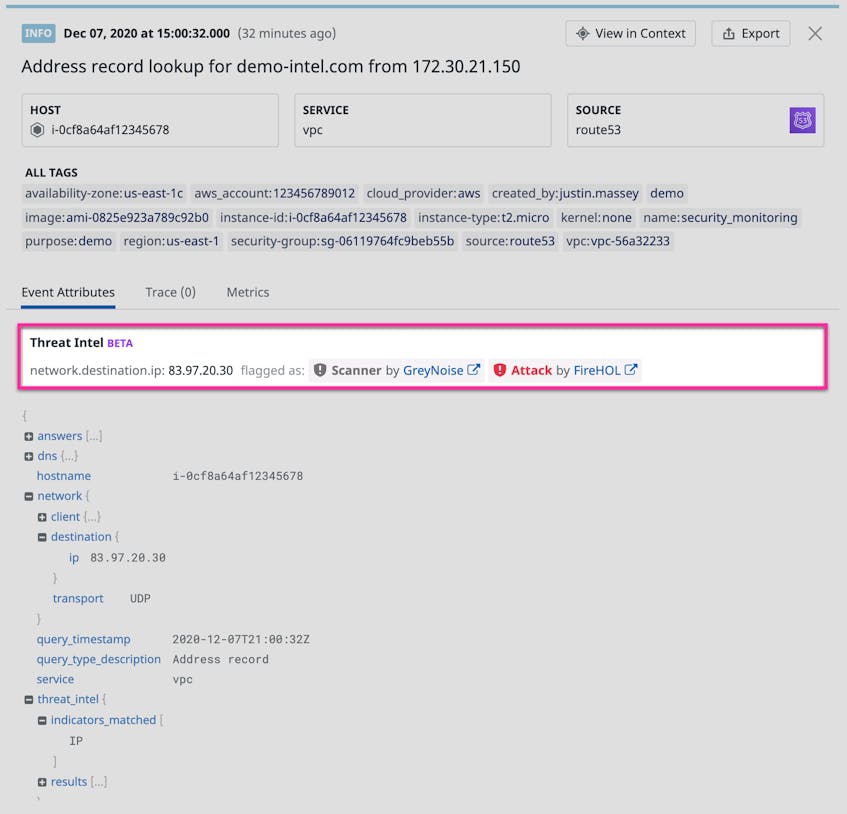
Datadog automatically operationalizes threat intelligence for you by analyzing all ingested logs that have relevant attributes. No matter the source of the data, if your logs have a network.client.ip standard attribute in them, we will analyze that against all IP addresses in our threat intelligence feeds. If Datadog finds an indicator of compromise in a log, such as an anonymized IP tied to a VPN, proxy, or Tor exit node, it appends a threat_intel attribute to the log event to provide additional insights based on available intelligence. Datadog will also include information such as the activity category (e.g., scanner, attack, abuse) and the actor’s intention (e.g., malicious or benign, if known) as new attributes, giving you rich context when investigating security alerts.
Detect activity from known threat actors
Threat intelligence includes indicators about the patterns that actors use to exploit vulnerabilities in your systems (for example, IPs that are known sources of attack). This data is indispensable for quickly and efficiently detecting any activity that other organizations have already observed as legitimate threats.
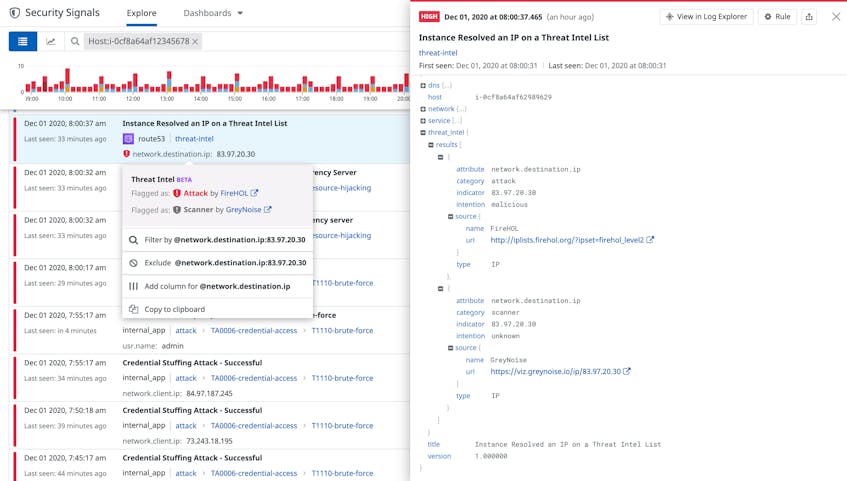
Datadog’s built-in Threat Detection Rules automatically look for whether known malicious IPs are interacting with your applications and services. If the IPs are on any threat intelligence feeds, Datadog will also categorize the detected threat and provide additional context around why the IP was flagged. This can include several different types of malicious activity, such as HTTP abuse (e.g., comment spamming) or acting as a scanner (e.g., SSH probing).
Threat Intelligence can also be used to create or customize new Detection Rules. For example, if you are analyzing application logs for brute force attacks, you may want to add threat intelligence data to your detection logic. If the brute force attempts are coming from a known malicious IP address, you could add a query that includes @threat_intel.indicators_matched:IP to escalate the severity of the resulting Security Signal and block the IP automatically at the edge.
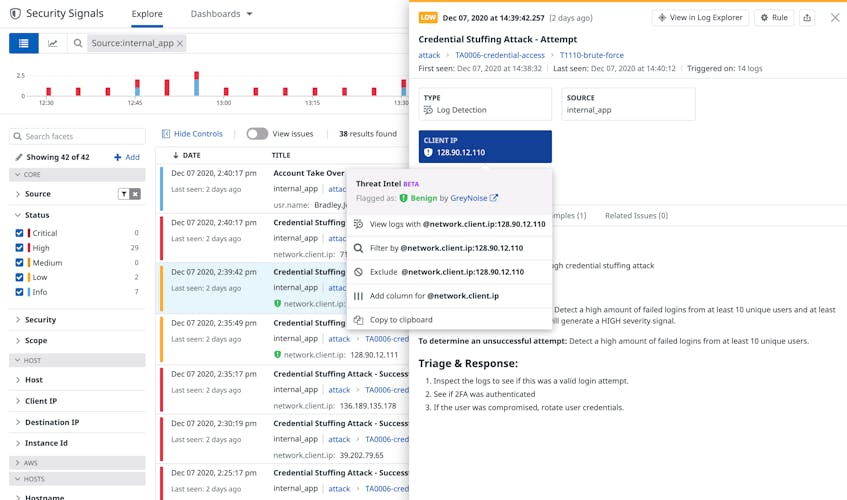
Accelerate investigations and reduce noise
In addition to detecting new threats, Threat Intelligence also provides relevant context that reduces false positives and accelerates triage of Security Signals. When a Threat Detection Rule triggers a Security Signal, Datadog Cloud SIEM automatically summarizes context from all triggering events. For example, if a credential stuffing attack originates from five specific IPs, Datadog automatically includes each IP in the resulting Security Signal. In turn, if any of these IPs appear in threat intelligence feeds, the Security Signal calls it out. This includes activity from benign security research actors, such as shodan.io, which you can safely ignore.
When it’s not clear whether an attacker’s intention is malicious or benign, determining whether their behavior is targeted or not is still a useful input in prioritizing alert triage. For example, a botnet scanning the internet at large for a new vulnerability is more likely engaged in a fully automated attack (e.g., installing a cryptominer on vulnerable instances) than in a targeted campaign against your organization. Datadog automatically links to threat intelligence partner portals in every affected log entry or triggered signal, so you can easily review more details associated with an indicator and confirm if it was a part of a targeted attack.
Get started with Threat Intelligence
Threat intelligence is built into Datadog Cloud SIEM, making it easy to leverage key knowledge from expert security partners to automatically surface threats to your applications and infrastructure. If you already use Cloud SIEM, we have automatically added you to the rollout plan for the beta, and you should start seeing threat intelligence matches appear in your Security Signals in the upcoming weeks. Otherwise, you can get started with Cloud SIEM. If you don’t yet use Datadog, you can sign up for a free 14-day trial today.