In order to maintain compliance, enforce governance, and build transparency, teams across your organization need deep insight into how their users and automation interact with Datadog. For stakeholders in leadership roles, such as CIOs and CDOs, knowing what actions users took and when is essential for spotting gaps in enablement, budgeting, and reporting, as well as building a modern compliance strategy for the organization as a whole. At the same time, administrators and security analysts need visibility to ensure that operational workflows stay intact and to follow up when incidents occur.
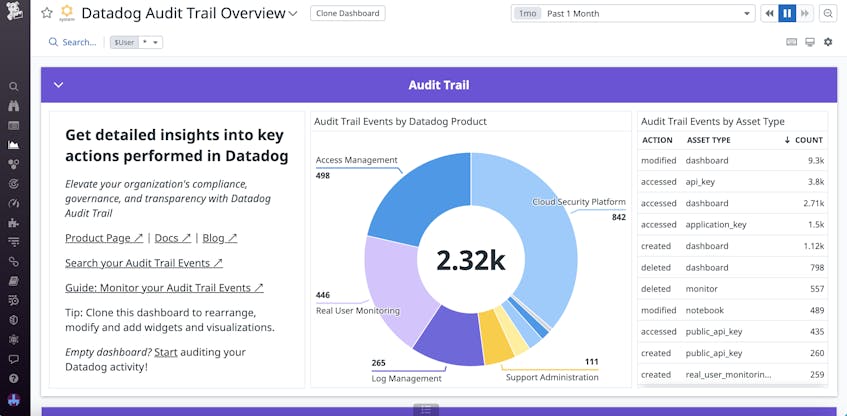
With Datadog Audit Trail, you have access to granular, centralized records of user and API activity throughout the platform. You can easily analyze these records in our out-of-the-box dashboard, as well as alert on key system events that have billing and access impact. This information allows your organization to keep up with compliance checks, ensure best practices, and share insights with stakeholders.
Build a modern compliance strategy with Datadog
Datadog Audit Trail provides end-to-end visibility into user actions, so you can see the path each user took in the app, and then use that information to diagnose issues and implement measures to keep your systems compliant.
You can leverage Audit Trail to help your organization meet crucial privacy and reporting standards like the Health Insurance Portability and Accountability Act (HIPAA), General Data Protection Regulation (GDPR), Federal Risk and Authorization Management Program (FedRAMP), and California Consumer Privacy Act (CCPA). The information you obtain from Audit Trail can assist you with customizing log index retention times elsewhere in the system, and you can view Audit Trail events for up to 90 days in Datadog with archiving options for long-term storage. Additionally, you can use Audit Trail alongside Datadog Cloud Security Information and Event Management (SIEM) to unify security tasks across your organization.
Audit Trail comes with an out-of-the-box dashboard that allows you to visualize day-to-day user activity. Detailed graphics help you to spot unusual behavior, such as spikes in authentication events that could be caused by automated attacks. You can also set up alerts on system events to automatically notify you about anomalies or outliers, then dive into Audit Trail to investigate. In the case of a security breach, Audit Trail allows you to identify the malicious users, see what they may have accessed, and manage the blast radius.
Building a modern compliance strategy requires that you both monitor and assess system activity. When used alongside Role Based Access Control (RBAC) and Sensitive Data Scanner (SDS), Audit Trail allows you to do just this. RBAC and Sensitive Data Scanner both help you proactively manage access in Datadog, and Audit Trail gives you the data you need to retrospectively investigate and diagnose security issues that can affect compliance.
A common scenario for organizations is to use RBAC to restrict access to dashboards that contain sensitive user information, such as usernames and passwords, and then use Sensitive Data Scanner to redact that information elsewhere in Datadog. For example, let’s say you notice that a recent change to a custom role allows certain users to see dashboards they shouldn’t have access to. After fixing the configuration, you can use Audit Trail to determine which Datadog users viewed the dashboards. You’re then able to confirm that only users with the proper authorization saw the exposed information.
Ensure Datadog platform governance across teams
Unintentional changes to Datadog resources—such as API keys, monitors, dashboards, and log pipelines—can disrupt your team’s workflows. Automated systems can magnify the impact of interruptions even more, potentially breaking CI/CD pipelines or tools like Terraform. These disruptions can be difficult to prevent, with blindspots in asset ownership or process design making it hard to catch problematic changes and figure out who to contact. And even after you fix any issues with your own workflow, there may be other system-wide impacts that go unnoticed.
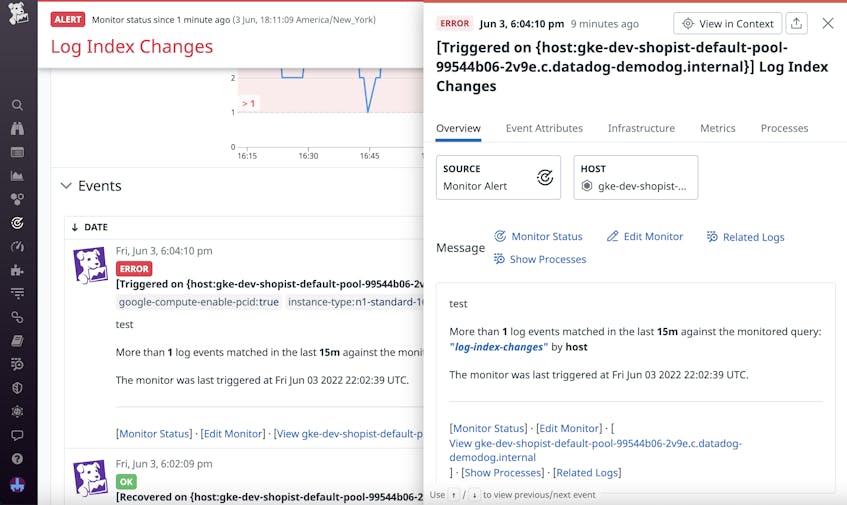
With Datadog Audit Trail, you can easily view a list of recent actions performed in the system to help you investigate and diagnose issues caused by configuration changes. By narrowing the Audit Trail events to a certain timeframe, you can identify any unusual activity around the time the incident occurred. You can also use filters such as event ID and authentication method to quickly identify the root cause, as well as view associated user IDs and emails to determine who controls the resource in question.
Let’s say a monitor your team relies on for infrastructure health updates is no longer showing data from your hosts. By digging into the audit events, you notice that a member of a frontend dev team recently made changes to the monitor. You reach out to this user and determine that they accidentally modified it while configuring one for their own team. You’re then able to work together to undo the updates and create new best practices to prevent future misconfigurations.
Audit Trail also gives you visibility into Datadog configuration changes that may affect your budget, such as modifications to log index retention times and sampling of noisy log events. Log indexes can be useful for managing cost by allowing your organization to retain only the most essential data long-term. Using Audit Trail, you can set up monitors to notify you about any log index or exclusion filter changes. If a user adjusts either of these configurations, you can reach out to them to confirm whether it was a mistake.
Increase transparency using context-rich insights
With Datadog Audit Trail, you can easily share findings and reports about your Datadog usage with other stakeholders, including audit, security, and Governance, Risk, and Compliance (GRC) teams. You can export views and events directly to monitors, incidents, notebooks, and dashboards to enrich your resources with added context. Additionally, you can also send these views directly to team members who may be involved in an audit or other investigation.
In the situation described above, you could share the modified indexes event with your organization’s billing team. They would then be able to investigate these changes to determine any impact to your organization’s cost and take remediatory steps, such as reducing the retention periods for other unnecessary data to compensate. You could also send the event details to your security and GRC teams to determine whether this user should’ve had the access needed to change these indexes in the first place. If not, you could add these findings to follow-up audit reports.
Start monitoring Datadog platform adoption with Audit Trail today
Datadog Audit Trail gives you full visibility into your Datadog platform adoption, enabling you to meet compliance, governance, and transparency standards across your organization. You can use Audit Trail alongside other Datadog services, such as Cloud SIEM, RBAC, and Sensitive Data Scanner, for greater visibility into and control over your teams’ Datadog usage. Additionally, Audit Trail can be used with or without Datadog Log Management.
If you’re an existing customer, you can get started with Datadog Audit Trail using our documentation. Or, if you’re new to Datadog, you can sign up for a 14-day free trial.