Governance, risk, and compliance (GRC) are major inhibitors for organizations moving to the cloud—and for good reason. Cloud environments are complex, and even a single misconfigured security group can result in a serious data breach. In fact, misconfigurations were the leading cause of cloud security breaches in 2020. This puts a lot of pressure on developer and operations teams to properly secure their services and maintain regulatory compliance. And to add fuel to the fire, these tasks are becoming increasingly arduous, as safe and compliant configurations must be enforced across multiple cloud platforms, consoles, and cloud security tools. It’s not unusual for site reliability and security engineers to lose hundreds of hours cataloguing asset inventory data and collecting relevant logs for third-party audits.
We’re excited to announce the general availability of Cloud Security Posture Management (CSPM), which enables you to easily track the compliance posture of your production environment, automate audit evidence collection, and catch misconfigurations that leave your organization vulnerable to attacks. With support for industry-standard compliance frameworks like PCI DSS, SOC 2, and CIS (Center for Internet Security), Cloud Security Posture Management lets developers and security engineers detect misconfigurations in the context of other security threats and application performance, and prevent security issues—all from within the same Datadog platform they use every day.
Continuously check the configurations of cloud resources and workloads
When it comes to production cloud environments, evidence for audits and compliance findings is often spread across endless streams of system and application logs, network traffic, live process telemetry, configurations, and vulnerability assessments.
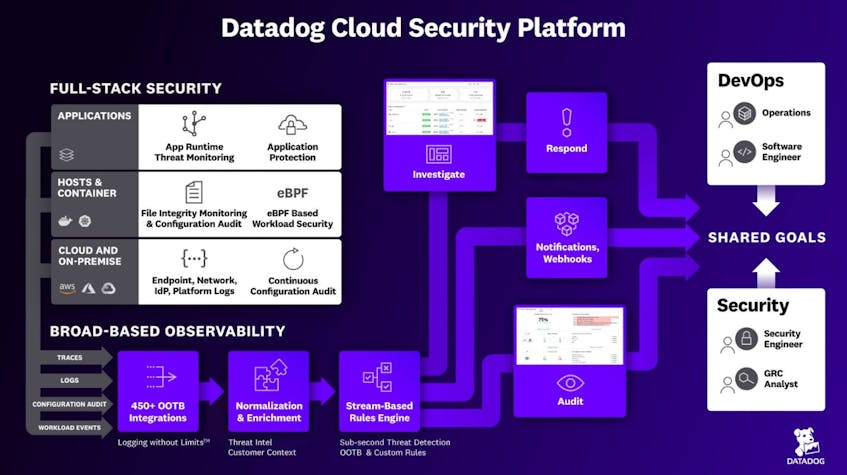
As a centralized observability platform with comprehensive access to telemetry across every level of your environment, Datadog is uniquely positioned to meet this challenge. In addition to Datadog’s more than 750 technology integrations, CSPM enhances security visibility by:
- Continuously auditing the configuration of your cloud accounts, hosts, and containers, no matter how short lived.
- Leveraging our enhanced Datadog Agent to review local configuration information from servers, containers, and Kubernetes clusters.
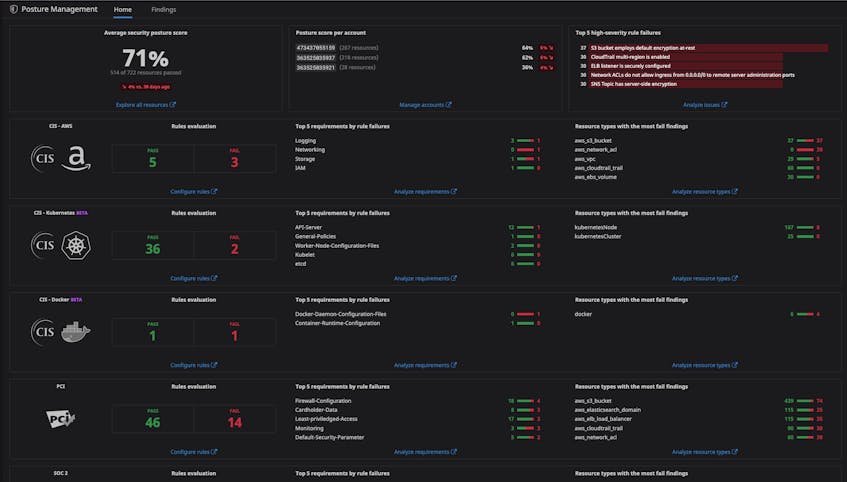
Expert-built security posture dashboards
Datadog’s out-of-the-box security posture dashboards display the number of tracked resources in your cloud environment, the types of compliance violations detected (grouped by severity, control, requirement, and resource type), as well as variations in detected compliance findings over time. Currently, Datadog tracks controls within PCI, SOC 2, HIPAA, GDPR, and CIS Benchmarks for AWS, Azure, Docker, and Kubernetes. More support for industry benchmarks and compliance standards is on the way.
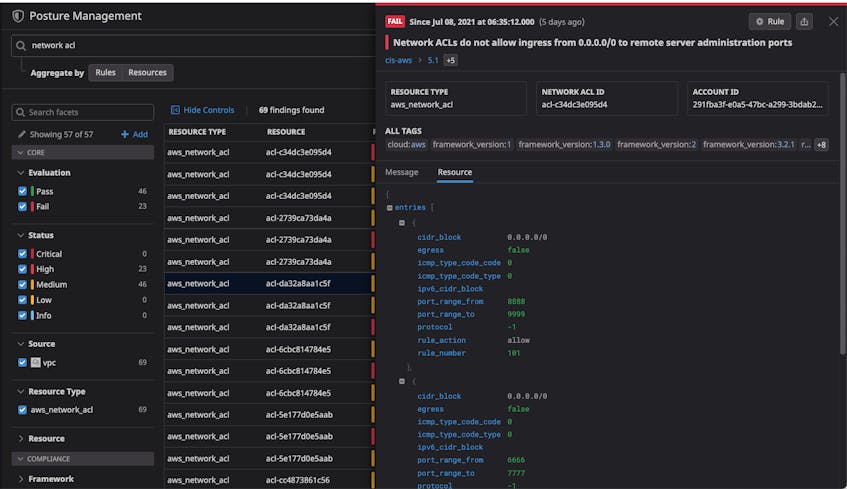
Monitoring the configuration of cloud resources
Misconfigurations in your cloud environment, such as an asset with unrestricted access from the public internet, can lead to major security breaches if left unaddressed. It’s critical that the teams responsible for securing cloud services can identify and address misconfigurations right as they occur. CSPM continuously assesses the configuration of cloud services, giving your team immediate visibility into security issues across your cloud accounts.
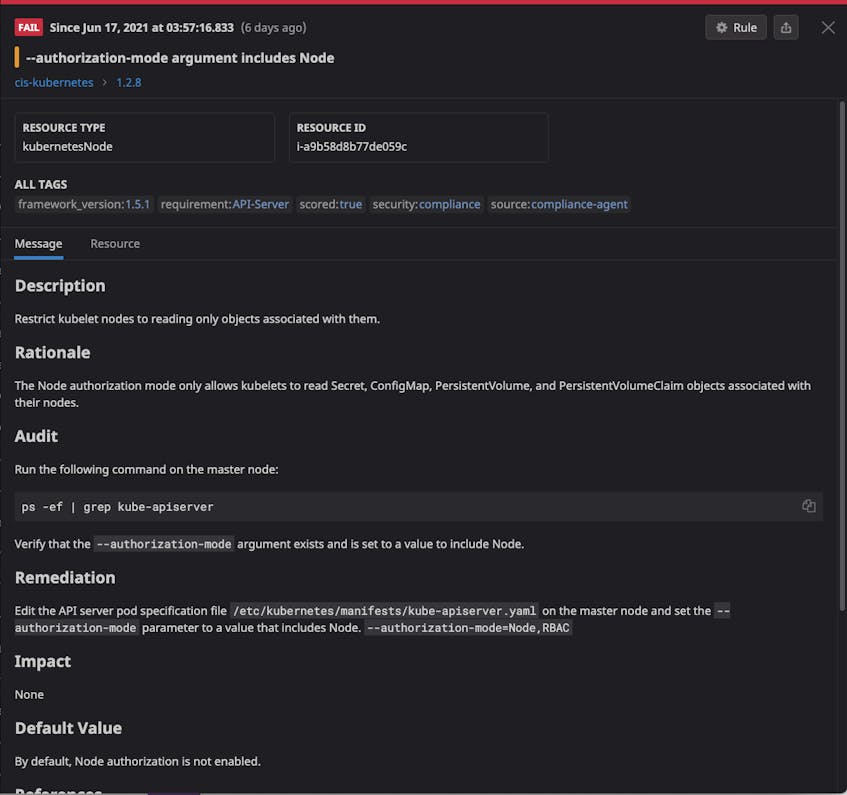
Monitoring container and Kubernetes configurations
With the move towards containerized environments, security and compliance teams are expected to demonstrate that the configuration baselines for their container runtime (e.g., Docker) and orchestrator (e.g., Kubernetes) are managed securely. A popular solution is to enforce configuration checks in continuous build and integration pipelines. While this approach provides a valuable point-in-time guardrail, it also assumes that your production environment will never change. To provide a holistic solution, we’ve expanded the Datadog Agent to continuously check the configuration of your Docker containers and Kubernetes control plane against CIS leading practices.
Detect drift from critical compliance controls
CSPM comes with over 250 out-of-the-box rules to evaluate controls within PCI, SOC 2, HIPAA, GDPR, and other compliance frameworks. Datadog runs these rules against your servers, containers, Kubernetes clusters, AWS services, and Azure services (private beta), with support for GCP on the way. These rulesets are customizable, and you can extend each rule to your specific needs with just a few clicks.
Prioritize and remediate potential misconfigurations
Whether from within your cloud resources or your hosts and containers, when Datadog detects a compliance violation it records:
- the state of the misconfigured asset
- the configuration rule that was broken
- the relative severity of the failure
This allows you to quickly assess the scope of potential compliance violations in terms of teams, services, and environments that might be affected. In turn, this means you can assess the potential risk of each violation to accurately prioritize their remediation.
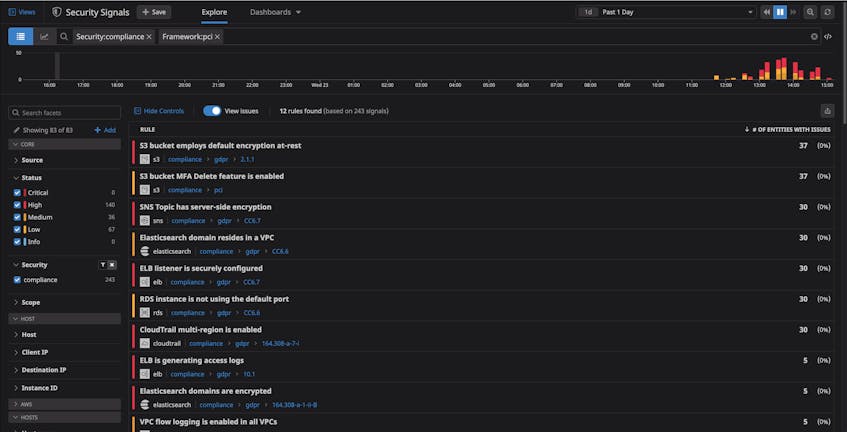
Correlate findings with other security issues
You can view all of your findings in the Security Explorer, alongside any other security issue that might be related to a misconfiguration. For example, a security signal might tell you that Datadog detected traffic from an external IP address to an internal service, while a finding tells you that an AWS security group has recently been misconfigured to allow public internet access. From there, you can check your AWS CloudTrail logs to determine how the offending changes occurred and, using Datadog’s collaboration integrations with services like Slack and PagerDuty, notify the right people to get the problem fixed.
Get started with CSPM today
Datadog Cloud Security Posture Management expands the scope of your security operations and makes it easy to keep up with a rapidly evolving compliance landscape. If you already use Datadog, you can self-enroll in-app or request a trial from your CSM. Otherwise, get started with a 14-day free trial.